
IBM token ring
Encyclopedia



Local area network
A local area network is a computer network that interconnects computers in a limited area such as a home, school, computer laboratory, or office building...
(LAN) technology is a local area network protocol which resides at the data link layer
Data link layer
The data link layer is layer 2 of the seven-layer OSI model of computer networking. It corresponds to, or is part of the link layer of the TCP/IP reference model....
(DLL) of the OSI model
OSI model
The Open Systems Interconnection model is a product of the Open Systems Interconnection effort at the International Organization for Standardization. It is a prescription of characterizing and standardizing the functions of a communications system in terms of abstraction layers. Similar...
. It uses a special three-byte frame called a token that travels around the ring. Token-possession grants the possessor permission to transmit on the medium. Token ring frames travel completely around the loop.
Initially used only in IBM computers, it was eventually standardized with protocol IEEE 802.5.
Description
Stations on a token ring LAN are logically organized in a ring topologyRing network
A ring network is a network topology in which each node connects to exactly two other nodes, forming a single continuous pathway for signals through each node - a ring...
with data being transmitted sequentially from one ring station to the next with a control token circulating around the ring controlling access. This token passing
Token passing
In telecommunication, token passing is a channel access method where a signal called a token is passed between nodes that authorizes the node to communicate. The most well-known examples are token ring and ARCNET....
mechanism is shared by ARCNET
ARCNET
ARCNET is a local area network protocol, similar in purpose to Ethernet or Token Ring. ARCNET was the first widely available networking system for microcomputers and became popular in the 1980s for office automation tasks...
, token bus
Token bus
Token bus is a network implementing the token ring protocol over a "virtual ring" on a coaxial cable. A token is passed around the network nodes and only the node possessing the token may transmit. If a node doesn't have anything to send, the token is passed on to the next node on the virtual ring...
, and FDDI, and has theoretical advantages over the stochastic
Stochastic
Stochastic refers to systems whose behaviour is intrinsically non-deterministic. A stochastic process is one whose behavior is non-deterministic, in that a system's subsequent state is determined both by the process's predictable actions and by a random element. However, according to M. Kac and E...
CSMA/CD of Ethernet
Ethernet
Ethernet is a family of computer networking technologies for local area networks commercially introduced in 1980. Standardized in IEEE 802.3, Ethernet has largely replaced competing wired LAN technologies....
.
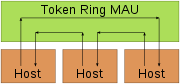
Physically, a token ring network is wired as a star
Star network
Star networks are one of the most common computer network topologies. In its simplest form, a star network consists of one central switch, hub or computer, which acts as a conduit to transmit messages...
, with 'hubs' and arms out to each station and the loop going out-and-back through each.
Cabling is generally IBM "Type-1" shielded twisted pair
Twisted pair
Twisted pair cabling is a type of wiring in which two conductors are twisted together for the purposes of canceling out electromagnetic interference from external sources; for instance, electromagnetic radiation from unshielded twisted pair cables, and crosstalk between neighboring pairs...
, with unique hermaphroditic connectors, commonly referred to as IBM data connectors. The connectors have the disadvantage of being quite bulky, requiring at least 3 x 3 cm panel space, and being relatively fragile.
Initially (in 1985) token ring ran at 4 Mbit/s, but in 1989 IBM introduced the first 16 Mbit/s token ring products and the 802.5 standard was extended to support this. In 1981, Apollo Computer
Apollo Computer
Apollo Computer, Inc., founded 1980 in Chelmsford, Massachusetts by William Poduska and others, developed and produced Apollo/Domain workstations in the 1980s. Along with Symbolics and Sun Microsystems, Apollo was one of the first vendors of graphical workstations in the 1980s...
introduced their proprietary 12 Mbit/s Apollo token ring (ATR) and Proteon introduced their 10 Mbit/s ProNet-10 token ring network in 1984. However, IBM token ring was not compatible with ATR or ProNet-10.
Each station passes or repeats the special token frame around the ring to its nearest downstream neighbour. This token-passing process is used to arbitrate access to the shared ring media. Stations that have data frames to transmit must first acquire the token before they can transmit them. Token ring LANs normally use differential Manchester encoding
Differential Manchester encoding
Differential Manchester encoding, also called biphase mark code or FM1, is a line code in which data and clock signals are combined to form a single 2-level self-synchronizing data stream. It is a differential encoding, using the presence or absence of transitions to indicate logical value...
of bits on the LAN media.
IBM popularized the use of token ring LANs in the mid 1980s when it released its IBM token ring architecture based on active MAUs (Media Access Unit
Media Access Unit
A Media Access Unit is a device to attach multiple network stations in a star topology in a token ring network, internally wired to connect the stations into a logical ring. The MAU contains relays to short out nonoperating stations...
, not to be confused with Medium Attachment Unit
Medium Attachment Unit
A Medium Attachment Unit is a transceiver which converts signals on an Ethernet cable to and from Attachment Unit Interface signals.On original 10BASE5 Ethernet, the MAU was typically clamped to the Ethernet cable...
) and the IBM Structured Cabling System. The Institute of Electrical and Electronics Engineers (IEEE) later standardized a token ring LAN system as IEEE 802.5.
Token ring LAN speeds of 4 Mbit/s and 16 Mbit/s were standardized by the IEEE 802.5 working group. An increase to 100 Mbit/s was standardized and marketed during the wane of token ring's existence while a 1000 Mbit/s speed was actually approved in 2001, but no products were ever brought to market.
When token ring LANs were first introduced at 4 Mbit/s, there were widely circulated claims that they were superior to Ethernet
Ethernet
Ethernet is a family of computer networking technologies for local area networks commercially introduced in 1980. Standardized in IEEE 802.3, Ethernet has largely replaced competing wired LAN technologies....
, but these claims were fiercely debated.
With the development of switched
Network switch
A network switch or switching hub is a computer networking device that connects network segments.The term commonly refers to a multi-port network bridge that processes and routes data at the data link layer of the OSI model...
Ethernet and faster variants of Ethernet, token ring architectures lagged behind Ethernet, and the higher sales of Ethernet allowed economies of scale
Economies of scale
Economies of scale, in microeconomics, refers to the cost advantages that an enterprise obtains due to expansion. There are factors that cause a producer’s average cost per unit to fall as the scale of output is increased. "Economies of scale" is a long run concept and refers to reductions in unit...
which drove down prices further, and added a compelling price advantage.
Token ring networks have since declined in usage and the standards activity has since come to a standstill as 100Mbps switched Ethernet has dominated the LAN/layer 2 networking market.
Token frame
When no station is transmitting a data frame, a special token frame circles the loop. This special token frame is repeated from station to station until arriving at a station that needs to transmit data. When a station needs to transmit data, it converts the token frame into a data frame for transmission. Once the sending station receives its own data frame, it converts the frame back into a token. If a transmission error occurs and no token frame, or more than one, is present, a special station referred to as the Active Monitor detects the problem and removes and/or reinserts tokens as necessary (see Active and standby monitors). On 4 Mbit/s Token Ring, only one token may circulate; on 16 Mbit/s Token Ring, there may be multiple tokens.The special token frame consists of three bytes as described below (J and K are special non-data characters, referred to as code violations).
Token priority
Token ring specifies an optional medium access scheme allowing a station with a high-priority transmission to request priority access to the token.8 priority levels, 0–7, are used. When the station wishing to transmit receives a token or data frame with a priority less than or equal to the station's requested priority, it sets the priority bits to its desired priority. The station does not immediately transmit; the token circulates around the medium until it returns to the station. Upon sending and receiving its own data frame, the station downgrades the token priority back to the original priority.
Token ring frame format
A data token ring frame is an expanded version of the token frame that is used by stations to transmit media access controlMedia Access Control
The media access control data communication protocol sub-layer, also known as the medium access control, is a sublayer of the data link layer specified in the seven-layer OSI model , and in the four-layer TCP/IP model...
(MAC) management frames or data frames from upper layer protocols and applications.
Token Ring and IEEE 802.5 support two basic frame types: tokens and data/command frames. Tokens
are 3 bytes in length and consist of a start delimiter, an access control byte, and an end delimiter.
Data/command frames vary in size, depending on the size of the Information field. Data frames carry
information for upper-layer protocols, while command frames contain control information and have no
data for upper-layer protocols.
Data/Command Frame
| SD | AC | FC | DA | SA | PDU from LLC (IEEE 802.2) | CRC | ED | FS |
|---|---|---|---|---|---|---|---|---|
| 8 bits | 8 bits | 8 bits | 48 bits | 48 bits | up to 18200x8 bits | 32 bits | 8 bits | 8 bits |
Starting Delimiter : consists of a special bit pattern denoting the beginning of the frame. The bits from most significant to least significant are J,K,0,J,K,0,0,0. J and K are code violations. Since Manchester encoding is self clocking, and has a transition for every encoded bit 0 or 1, the J and K codings violate this, and will be detected by the hardware.
| J | K | 0 | J | K | 0 | 0 | 0 |
|---|---|---|---|---|---|---|---|
| 1 bit | 1 bit | 1 bit | 1 bit | 1 bit | 1 bit | 1 bit | 1 bit |
Access Control : this byte field consists of the following bits from most significant to least significant bit order: P,P,P,T,M,R,R,R. The P bits are priority bits, T is the token bit which when set specifies that this is a token frame, M is the monitor bit which is set by the Active Monitor (AM) station when it sees this frame, and R bits are reserved bits.
| + | Bits 0–2 | 3 | 4 | 5–7 | ||||||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 0 | Priority | Token | Monitor | Reservation | ||||||||||||||||||||||||||||
Frame Control : a one byte field that contains bits describing the data portion of the frame contents which indicates whether the frame contains data or control information. In control frames, this byte specifies the type of control information.
| + | Bits 0–2 | Bits 3–7 | ||||||
|---|---|---|---|---|---|---|---|---|
| 0 | Frame type | Control Bits | ||||||
Frame type – 01 indicates LLC frame IEEE 802.2 (data) and ignore control bits;
00 indicates MAC frame and control bits indicate the type of MAC
Media Access Control
The media access control data communication protocol sub-layer, also known as the medium access control, is a sublayer of the data link layer specified in the seven-layer OSI model , and in the four-layer TCP/IP model...
control frame
Destination address : a six byte field used to specify the destination(s) physical address .
Source address :Contains physical address of sending station . It is six byte field that is either the local assigned address (LAA) or universally assigned address (UAA) of the sending station adapter.
Data : a variable length field of 0 or more bytes, the maximum allowable size depending on ring speed containing MAC management data or upper layer information.Maximum length of 4500 bytes
Frame Check Sequence : a four byte field used to store the calculation of a CRC for frame integrity verification by the receiver.
Ending Delimiter : The counterpart to the starting delimiter, this field marks the end of the frame and consists of the following bits from most significant to least significant: J,K,1,J,K,1,I,E. I is the intermediate frame bit and E is the error bit.
| J | K | 1 | J | K | 1 | I | E |
|---|---|---|---|---|---|---|---|
| 1 bit | 1 bit | 1 bit | 1 bit | 1 bit | 1 bit | 1 bit | 1 bit |
Frame Status : a one byte field used as a primitive acknowledgement scheme on whether the frame was recognized and copied by its intended receiver.
| A | C | 0 | 0 | A | C | 0 | 0 |
|---|---|---|---|---|---|---|---|
| 1 bit | 1 bit | 1 bit | 1 bit | 1 bit | 1 bit | 1 bit | 1 bit |
A = 1 , Address recognized
C = 1 , Frame copied
Token Frame
| Start Delimeter | Access Control | End Delimeter |
|---|---|---|
| 8 bits | 8 bits | 8 bits |
Abort Frame
| SD | ED |
|---|---|
| 8 bits | 8 bits |
Used to abort transmission by the sending station
Active and standby monitors
Every station in a token ring network is either an active monitor (AM) or standby monitor (SM) station.However, there can be only one active monitor on a ring at a time.
The active monitor is chosen through an election or monitor contention process.
The monitor contention process is initiated when
- a loss of signal on the ring is detected.
- an active monitor station is not detected by other stations on the ring.
- a particular timer on an end station expires such as the case when a station hasn't seen a token frame in the past 7 seconds.
When any of the above conditions take place and a station decides that a new monitor is needed, it will transmit a "claim token" frame, announcing that it wants to become the new monitor. If that token returns back to the sender, it is OK for it to become the monitor. If some other station tries to become the monitor at the same time then the station with the highest MAC address
MAC address
A Media Access Control address is a unique identifier assigned to network interfaces for communications on the physical network segment. MAC addresses are used for numerous network technologies and most IEEE 802 network technologies, including Ethernet...
will win the election process. Every other station becomes a standby monitor. All stations must be capable of becoming an active monitor station if necessary.
The active monitor performs a number of ring administration functions. The first function is to operate as the master clock for the ring in order to provide synchronization of the signal for stations on the wire. Another function of the AM is to insert a 24-bit delay into the ring, to ensure that there is always sufficient buffering in the ring for the token to circulate. A third function for the AM is to ensure that exactly one token circulates whenever there is no frame being transmitted, and to detect a broken ring. Lastly, the AM is responsible for removing circulating frames from the ring.
Token ring insertion process
Token ring stations must go through a 5-phase ring insertion process before being allowed to participate in the ring network. If any of these phases fail, the token ring station will not insert into the ring and the token ring driver may report an error.- Phase 0 (Lobe Check) — A station first performs a lobe media check. A station is wrapped at the MSAU and is able to send 2000 test frames down its transmit pair which will loop back to its receive pair. The station checks to ensure it can receive these frames without error.
- Phase 1 (Physical Insertion) — A station then sends a 5 volt signal to the MSAU to open the relay.
- Phase 2 (Address Verification) — A station then transmits MAC frames with its own MAC address in the destination address field of a token ring frame. When the frame returns and if the address copied , the station must participate in the periodic (every 7 seconds) ring poll process. This is where stations identify themselves on the network as part of the MAC management functions.
- Phase 3 (Participation in ring poll) — A station learns the address of its Nearest Active Upstream Neighbour (NAUN) and makes its address known to its nearest downstream neighbour, leading to the creation of the ring map. Station waits until it receives an AMP or SMP frame with the ARI and FCI bits set to 0. When it does, the station flips both bits (ARI and FCI) to 1, if enough resources are available, and queues an SMP frame for transmission. If no such frames are received within 18 seconds, then the station reports a failure to open and de-inserts from the ring. If the station successfully participates in a ring poll, it proceeds into the final phase of insertion, request initialization.
- Phase 4 (Request Initialization) — Finally a station sends out a special request to a parameter server to obtain configuration information. This frame is sent to a special functional address, typically a token ring bridge, which may hold timer and ring number information with which to tell the new station about.
See also
- Cambridge RingCambridge RingThe Cambridge Ring was an experimental local area network architecture developed at the Cambridge University Computer Laboratory in the mid-late 1970s and early 1980s. It used a ring topology with a theoretical limit of 255 nodes , around which cycled a fixed number of packets...
- List of device bandwidths

