Ciphertext
Encyclopedia
In cryptography
, ciphertext (or cyphertext) is the result of encryption
performed on plaintext
using an algorithm, called a cipher
. Ciphertext is also known as encrypted or encoded information because it contains a form of the original plaintext that is unreadable by a human or computer without the proper cipher to decrypt it. Decryption, the inverse of encryption, is the process of turning ciphertext into readable plaintext. Ciphertext is not to be confused with codetext because the latter is a result of a Code
, not a cipher.
 be the plaintext message that Alice wants to secretly transmit to Bob and let
be the plaintext message that Alice wants to secretly transmit to Bob and let  be the encryption cipher, where
be the encryption cipher, where  is a secret key. Alice must first transform the plaintext into ciphertext,
is a secret key. Alice must first transform the plaintext into ciphertext,  , in order to securely send the message to Bob.
, in order to securely send the message to Bob.
Both Alice and Bob must know the choice of key, , or else the ciphertext is useless. Once the message is encrypted as ciphertext, Alice can safely transmit it to Bob (assuming no one else knows the key). In order to read Alice's message, Bob must decrypt the ciphertext using
, or else the ciphertext is useless. Once the message is encrypted as ciphertext, Alice can safely transmit it to Bob (assuming no one else knows the key). In order to read Alice's message, Bob must decrypt the ciphertext using  which is known as the decryption cipher,
which is known as the decryption cipher,  .
.
begins thousands of years ago and contains a variety of different types of encryption. Earlier algorithms were performed by hand and are substantially different from modern algorithms, which are generally executed by a machine.
s. They include:
Historical ciphers are not generally used as a standalone encryption solution because they are quite easy to crack. Many of the classical ciphers can be cracked using brute force
or by analyzing only ciphertext with the exception of the one-time pad.
In a symmetric key algorithm (e.g., DES
and AES
), the sender and receiver must have a shared key set up in advance and kept secret from all other parties; the sender uses this key for encryption, and the receiver uses the same key for decryption. In an asymmetric key algorithm (e.g., RSA), there are two separate keys: a public key is published and enables any sender to perform encryption, while a private key is kept secret by the receiver and enables only him to perform correct decryption.
Symmetric key ciphers can be divided into block cipher
s and stream cipher
s. Block ciphers operate on fixed-length groups of bits, called blocks, with an unvarying transformation. Stream ciphers encrypt plaintext digits one at a time on a continuous stream of data and the transformation of successive digits varies during the encryption process.
Cryptanalysis is the study of methods for obtaining the meaning of encrypted information, without access to the secret information that is normally required to do so. Typically, this involves knowing how the system works and finding a secret key. Cryptanalysis is also referred to as codebreaking or cracking the code
. Ciphertext is generally the easiest part of a cryptosystem
to obtain and therefore is a important part of cryptanalysis. Depending on what information is available and what type of cipher is being analyzed, crypanalysts can follow one or more attack model
s to crack a cipher.
The ciphertext-only attack model is the weakest attack because it implies that the cryptanalyst has nothing but ciphertext. Modern ciphers rarely fail under this attack.
:Category:Uncracked codes and ciphers
Cryptography
Cryptography is the practice and study of techniques for secure communication in the presence of third parties...
, ciphertext (or cyphertext) is the result of encryption
Encryption
In cryptography, encryption is the process of transforming information using an algorithm to make it unreadable to anyone except those possessing special knowledge, usually referred to as a key. The result of the process is encrypted information...
performed on plaintext
Plaintext
In cryptography, plaintext is information a sender wishes to transmit to a receiver. Cleartext is often used as a synonym. Before the computer era, plaintext most commonly meant message text in the language of the communicating parties....
using an algorithm, called a cipher
Cipher
In cryptography, a cipher is an algorithm for performing encryption or decryption — a series of well-defined steps that can be followed as a procedure. An alternative, less common term is encipherment. In non-technical usage, a “cipher” is the same thing as a “code”; however, the concepts...
. Ciphertext is also known as encrypted or encoded information because it contains a form of the original plaintext that is unreadable by a human or computer without the proper cipher to decrypt it. Decryption, the inverse of encryption, is the process of turning ciphertext into readable plaintext. Ciphertext is not to be confused with codetext because the latter is a result of a Code
Code (cryptography)
In cryptography, a code is a method used to transform a message into an obscured form, preventing those who do not possess special information, or key, required to apply the transform from understanding what is actually transmitted. The usual method is to use a codebook with a list of common...
, not a cipher.
Symmetric key example
Let be the plaintext message that Alice wants to secretly transmit to Bob and let
be the plaintext message that Alice wants to secretly transmit to Bob and let  be the encryption cipher, where
be the encryption cipher, where  is a secret key. Alice must first transform the plaintext into ciphertext,
is a secret key. Alice must first transform the plaintext into ciphertext,  , in order to securely send the message to Bob.
, in order to securely send the message to Bob.Both Alice and Bob must know the choice of key,
 , or else the ciphertext is useless. Once the message is encrypted as ciphertext, Alice can safely transmit it to Bob (assuming no one else knows the key). In order to read Alice's message, Bob must decrypt the ciphertext using
, or else the ciphertext is useless. Once the message is encrypted as ciphertext, Alice can safely transmit it to Bob (assuming no one else knows the key). In order to read Alice's message, Bob must decrypt the ciphertext using  which is known as the decryption cipher,
which is known as the decryption cipher,  .
.Types of ciphers
The history of cryptographyHistory of cryptography
The history of cryptography begins thousands of years ago. Until recent decades, it has been the story of what might be called classic cryptography — that is, of methods of encryption that use pen and paper, or perhaps simple mechanical aids...
begins thousands of years ago and contains a variety of different types of encryption. Earlier algorithms were performed by hand and are substantially different from modern algorithms, which are generally executed by a machine.
Historical ciphers
Historical pen and paper ciphers used in the past are sometimes known as classical cipherClassical cipher
A cipher is a means of concealing a message, where letters of the message are substituted or transposed for other letters, letter pairs, and sometimes for many letters. In cryptography, a classical cipher is a type of cipher that was used historically but now has fallen, for the most part, into...
s. They include:
- Substitution cipherSubstitution cipherIn cryptography, a substitution cipher is a method of encryption by which units of plaintext are replaced with ciphertext according to a regular system; the "units" may be single letters , pairs of letters, triplets of letters, mixtures of the above, and so forth...
: the units of plaintext are replaced with ciphertext (Caesar cipherCaesar cipherIn cryptography, a Caesar cipher, also known as a Caesar's cipher, the shift cipher, Caesar's code or Caesar shift, is one of the simplest and most widely known encryption techniques. It is a type of substitution cipher in which each letter in the plaintext is replaced by a letter some fixed number...
and One-time padOne-time padIn cryptography, the one-time pad is a type of encryption, which has been proven to be impossible to crack if used correctly. Each bit or character from the plaintext is encrypted by a modular addition with a bit or character from a secret random key of the same length as the plaintext, resulting...
) - Transposition cipherTransposition cipherIn cryptography, a transposition cipher is a method of encryption by which the positions held by units of plaintext are shifted according to a regular system, so that the ciphertext constitutes a permutation of the plaintext. That is, the order of the units is changed...
: the ciphertext is a permutationPermutationIn mathematics, the notion of permutation is used with several slightly different meanings, all related to the act of permuting objects or values. Informally, a permutation of a set of objects is an arrangement of those objects into a particular order...
of the plaintext (Rail fence cipher) - Polyalphabetic substitution cipher: a substitution cipher using multiple substitution alphabets (Vigenère cipherVigenère cipherThe Vigenère cipher is a method of encrypting alphabetic text by using a series of different Caesar ciphers based on the letters of a keyword. It is a simple form of polyalphabetic substitution....
and Enigma machineEnigma machineAn Enigma machine is any of a family of related electro-mechanical rotor cipher machines used for the encryption and decryption of secret messages. Enigma was invented by German engineer Arthur Scherbius at the end of World War I...
) - Permutation cipherPermutation cipherIn classical cryptography, a permutation cipher is a transposition cipher in which the key is a permutation.To apply a cipher, a random permutation of size e is generated...
: a transposition cipher in which the key is a permutation
Historical ciphers are not generally used as a standalone encryption solution because they are quite easy to crack. Many of the classical ciphers can be cracked using brute force
Brute force attack
In cryptography, a brute-force attack, or exhaustive key search, is a strategy that can, in theory, be used against any encrypted data. Such an attack might be utilized when it is not possible to take advantage of other weaknesses in an encryption system that would make the task easier...
or by analyzing only ciphertext with the exception of the one-time pad.
Modern ciphers
Modern ciphers are more secure than classical ciphers and are designed to withstand a wide range of attacks. An attacker should not be able to find the key used in a modern cipher, even if he knows any amount of plaintext and corresponding ciphertext. Modern encryption methods can be divided into the following categories:- Private-key cryptography (symmetric key algorithm): the same key is used for encryption and decryption
- Public-key cryptographyPublic-key cryptographyPublic-key cryptography refers to a cryptographic system requiring two separate keys, one to lock or encrypt the plaintext, and one to unlock or decrypt the cyphertext. Neither key will do both functions. One of these keys is published or public and the other is kept private...
(asymmetric key algorithm): two different keys are used for encryption and decryption
In a symmetric key algorithm (e.g., DES
Data Encryption Standard
The Data Encryption Standard is a block cipher that uses shared secret encryption. It was selected by the National Bureau of Standards as an official Federal Information Processing Standard for the United States in 1976 and which has subsequently enjoyed widespread use internationally. It is...
and AES
Advanced Encryption Standard
Advanced Encryption Standard is a specification for the encryption of electronic data. It has been adopted by the U.S. government and is now used worldwide. It supersedes DES...
), the sender and receiver must have a shared key set up in advance and kept secret from all other parties; the sender uses this key for encryption, and the receiver uses the same key for decryption. In an asymmetric key algorithm (e.g., RSA), there are two separate keys: a public key is published and enables any sender to perform encryption, while a private key is kept secret by the receiver and enables only him to perform correct decryption.
Symmetric key ciphers can be divided into block cipher
Block cipher
In cryptography, a block cipher is a symmetric key cipher operating on fixed-length groups of bits, called blocks, with an unvarying transformation. A block cipher encryption algorithm might take a 128-bit block of plaintext as input, and output a corresponding 128-bit block of ciphertext...
s and stream cipher
Stream cipher
In cryptography, a stream cipher is a symmetric key cipher where plaintext digits are combined with a pseudorandom cipher digit stream . In a stream cipher the plaintext digits are encrypted one at a time, and the transformation of successive digits varies during the encryption...
s. Block ciphers operate on fixed-length groups of bits, called blocks, with an unvarying transformation. Stream ciphers encrypt plaintext digits one at a time on a continuous stream of data and the transformation of successive digits varies during the encryption process.
Cryptanalysis
Cryptanalysis is the study of methods for obtaining the meaning of encrypted information, without access to the secret information that is normally required to do so. Typically, this involves knowing how the system works and finding a secret key. Cryptanalysis is also referred to as codebreaking or cracking the code
Password cracking
Password cracking is the process of recovering passwords from data that has been stored in or transmitted by a computer system. A common approach is to repeatedly try guesses for the password...
. Ciphertext is generally the easiest part of a cryptosystem
Cryptosystem
There are two different meanings of the word cryptosystem. One is used by the cryptographic community, while the other is the meaning understood by the public.- General meaning :...
to obtain and therefore is a important part of cryptanalysis. Depending on what information is available and what type of cipher is being analyzed, crypanalysts can follow one or more attack model
Attack model
Attack models or attack types specify how much information a cryptanalyst has access to when cracking an encrypted message...
s to crack a cipher.
Attack Models
- Ciphertext-onlyCiphertext-only attackIn cryptography, a ciphertext-only attack or known ciphertext attack is an attack model for cryptanalysis where the attacker is assumed to have access only to a set of ciphertexts....
: the cryptanalyst has access only to a collection of ciphertexts or codetexts. - Known-plaintextKnown-plaintext attackThe known-plaintext attack is an attack model for cryptanalysis where the attacker has samples of both the plaintext , and its encrypted version . These can be used to reveal further secret information such as secret keys and code books...
: the attacker has a set of ciphertexts to which he knows the corresponding plaintext. - Chosen-plaintext attackChosen-plaintext attackA chosen-plaintext attack is an attack model for cryptanalysis which presumes that the attacker has the capability to choose arbitrary plaintexts to be encrypted and obtain the corresponding ciphertexts. The goal of the attack is to gain some further information which reduces the security of the...
: the attacker can obtain the ciphertexts corresponding to an arbitrary set of plaintexts of his own choosing.- Batch chosen-plaintext attack: where the cryptanalyst chooses all plaintexts before any of them are encrypted. This is often the meaning of an unqualified use of "chosen-plaintext attack".
- Adaptive chosen-plaintext attack: where the cryptanalyst makes a series of interactive queries, choosing subsequent plaintexts based on the information from the previous encryptions.
- Chosen-ciphertext attackChosen-ciphertext attackA chosen-ciphertext attack is an attack model for cryptanalysis in which the cryptanalyst gathers information, at least in part, by choosing a ciphertext and obtaining its decryption under an unknown key. In the attack, an adversary has a chance to enter one or more known ciphertexts into the...
: the attacker can obtain the plaintexts corresponding to an arbitrary set of ciphertexts of his own choosing.- Adaptive chosen-ciphertext attackAdaptive chosen-ciphertext attackAn adaptive chosen-ciphertext attack is an interactive form of chosen-ciphertext attack in which an attacker sends a number of ciphertexts to be decrypted, then uses the results of these decryptions to select subsequent ciphertexts...
- Indifferent chosen-ciphertext attack
- Adaptive chosen-ciphertext attack
- Related-key attackRelated-key attackIn cryptography, a related-key attack is any form of cryptanalysis where the attacker can observe the operation of a cipher under several different keys whose values are initially unknown, but where some mathematical relationship connecting the keys is known to the attacker...
: like a chosen-plaintext attack, except the attacker can obtain ciphertexts encrypted under two different keys. The keys are unknown, but the relationship between them is known; for example, two keys that differ in the one bit.
The ciphertext-only attack model is the weakest attack because it implies that the cryptanalyst has nothing but ciphertext. Modern ciphers rarely fail under this attack.
Famous ciphertexts
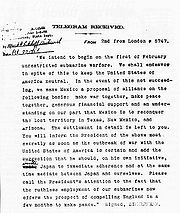
- The Babington PlotBabington PlotThe Babington Plot was a Catholic plot in 1586 to assassinate Queen Elizabeth, a Protestant, and put Mary, Queen of Scots, a Catholic, on the English throne. It led to the execution of Mary. The long-term goal was an invasion by the Spanish forces of King Philip II and the Catholic league in...
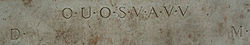
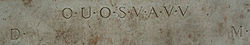
ciphers - The Shugborough inscriptionShugborough inscriptionThe Shugborough inscription is a sequence of letters - O U O S V A V V, between the letters D M - carved on the 18th-century Shepherd's Monument in the grounds of Shugborough Hall in Staffordshire, England, below a mirror image of Nicolas Poussin's painting, the Shepherds of Arcadia...
- The Zimmermann TelegramZimmermann TelegramThe Zimmermann Telegram was a 1917 diplomatic proposal from the German Empire to Mexico to make war against the United States. The proposal was caught by the British before it could get to Mexico. The revelation angered the Americans and led in part to a U.S...
- The Magic Words are Squeamish OssifrageThe Magic Words are Squeamish OssifrageThe text "The Magic Words are Squeamish Ossifrage" was the solution to a challenge ciphertext posed by the inventors of the RSA cipher in 1977. The problem appeared in Martin Gardner's Mathematical Games column in Scientific American. It was solved in 1993–1994 by a large joint computer...
- The cryptogramCryptogramA cryptogram is a type of puzzle which consists of a short piece of encrypted text. Generally the cipher used to encrypt the text is simple enough that cryptogram can be solved by hand. Frequently used are substitution ciphers where each letter is replaced by a different letter or number. To solve...
in "The Gold-BugThe Gold-Bug"The Gold-Bug" is a short story by Edgar Allan Poe. Set on Sullivan's Island, South Carolina, the plot follows William Legrand, who was recently bitten by a gold-colored bug. His servant Jupiter fears him to be going insane and goes to Legrand's friend, an unnamed narrator who agrees to visit his...
" - Beale ciphersBeale ciphersThe Beale ciphers are a set of three ciphertexts, one of which allegedly states the location of a buried treasure of gold, silver and jewels estimated to be worth over USD$63 million as of September, 2011. The other two ciphertexts allegedly describe the content of the treasure, and list the names...
- KryptosKryptosKryptos is an encrypted sculpture by American artist Jim Sanborn located on the grounds of the Central Intelligence Agency in Langley, Virginia. Since its dedication on November 3, 1990, there has been much speculation about the meaning of the encrypted messages it bears...
- Zodiac KillerZodiac KillerThe Zodiac Killer was a serial killer who operated in Northern California in the late 1960s and early 1970s. The killer's identity remains unknown. The Zodiac murdered victims in Benicia, Vallejo, Lake Berryessa and San Francisco between December 1968 and October 1969. Four men and three women...
ciphers
See also
- :RED/BLACK concept
- :Frequency analysis
- :Books on cryptography
- :Cryptographic hash function
:Category:Uncracked codes and ciphers
Further reading
- Helen Fouché Gaines, “Cryptanalysis”, 1939, Dover. ISBN 0-486-20097-3
- David Kahn, The Codebreakers - The Story of Secret Writing (ISBN 0-684-83130-9) (1967)
- Abraham SinkovAbraham SinkovDr. Abraham Sinkov was a US cryptanalyst.-Biography:Sinkov, the son of immigrants from Russia, was born in Philadelphia, but grew up in Brooklyn. After graduating from Boys High School—what today would be called a "magnet school" -- he took his B.S. in mathematics from City College of New York...
, Elementary Cryptanalysis: A Mathematical Approach, Mathematical Association of America, 1966. ISBN 0-88385-622-0