Secret sharing
Overview
Secrecy
Secrecy is the practice of hiding information from certain individuals or groups, perhaps while sharing it with other individuals...
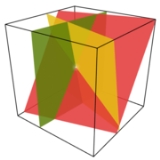
amongst a group of participants, each of whom is allocated a share of the secret. The secret can be reconstructed only when a sufficient number of shares are combined together; individual shares are of no use on their own.
More formally, in a secret sharing scheme there is one dealer and n players.

