Transport Layer Security
Encyclopedia
Transport Layer Security (TLS) and its predecessor, Secure Sockets Layer (SSL), are cryptographic protocol
s that provide communication security
over the Internet
. TLS and SSL encrypt the segments of network connections above the Transport Layer
, using asymmetric cryptography
for key exchange, symmetric encryption
for privacy, and message authentication code
s for message integrity.
Several versions of the protocols are in widespread use in applications such as web browsing, electronic mail
, Internet fax
ing, instant messaging
and voice-over-IP (VoIP).
TLS is an IETF
standards track
protocol, last updated in RFC 5246, and is based on the earlier SSL specifications developed by Netscape
Communications.
and tampering
.
Since most protocols can be used either with or without TLS (or SSL) it is necessary to indicate to the server whether the client is making a TLS connection or not. There are two main ways of achieving this, one option is to use a different port number for TLS connections (for example port 443 for HTTPS
). The other is to use to the regular port number and have the client request that the server switch the connection to TLS using a protocol specific mechanism (for example STARTTLS
for mail
and news
protocols).
Once the client and server have decided to use TLS they negotiate a stateful connection by using a handshaking procedure. During this handshake, the client and server agree on various parameters used to establish the connection's security.
This concludes the handshake and begins the secured connection, which is encrypted and decrypted with the key material until the connection closes.
If any one of the above steps fails, the TLS handshake fails and the connection is not created.
(API), which in 1993 explored the approach of having a secure transport layer API closely resembling Berkeley sockets
, to facilitate retrofitting preexisting network applications with security measures.
working with Netscape engineers Phil Karlton and Alan Freier. Newer versions of SSL/TLS are based on SSL 3.0.
On September 23, 2011 researchers Thai Duong and Juliano Rizzo demonstrated a "proof of concept" called BEAST (using a Java Applet to violate "same origin policy" constraints) for a long-known Cipher block chaining (CBC) vulnerability in TLS 1.0. Practical exploits had not been previously demonstrated for this vulnerability, which was originally discovered by Phillip Rogaway in 2002.
Mozilla updated the development versions of their NSS
libraries to mitigate BEAST-like attacks. NSS is used by Mozilla Firefox
and Google Chrome
to implement SSL. Some webservers that have a broken implementation of the SSL specification may stop working as a result.
The TLS 1.0-specific BEAST attack can be prevented by removing all CBC ciphers from your list of allowed ciphers—leaving only the RC4
cipher, which is still widely supported on most websites. Microsoft is releasing tools to support TLS 1.1 (which fixes this CBC attack vulnerability) on Microsoft servers and browsers.
TLS 1.2 was further refined in RFC 6176 in March 2011 redacting its backward compatibility with SSL such that TLS sessions will never negotiate the use of Secure Sockets Layer (SSL) version 2.0.
protocols, encapsulating the application-specific protocols such as HTTP
, FTP
, SMTP
, NNTP
and XMPP
. Historically it has been used primarily with reliable transport protocols such as the Transmission Control Protocol
(TCP). However, it has also been implemented with datagram-oriented transport protocols, such as the User Datagram Protocol
(UDP) and the Datagram Congestion Control Protocol
(DCCP), usage which has been standardized independently using the term Datagram Transport Layer Security
(DTLS).
A prominent use of TLS is for securing World Wide Web traffic carried by HTTP to form HTTPS
. Notable applications are electronic commerce
and asset management
. Increasingly, the Simple Mail Transfer Protocol
(SMTP) is also protected by TLS. These applications use public key certificate
s to verify the identity of endpoints.
TLS can also be used to tunnel an entire network stack to create a VPN
, as is the case with OpenVPN
. Many vendors now marry TLS's encryption and authentication capabilities with authorization. There has also been substantial development since the late 1990s in creating client technology outside of the browser to enable support for client/server applications. When compared against traditional IPsec
VPN technologies, TLS has some inherent advantages in firewall and NAT
traversal that make it easier to administer for large remote-access populations.
TLS is also a standard method to protect Session Initiation Protocol
(SIP) application signaling. TLS can be used to provide authentication and encryption of the SIP signaling associated with VoIP and other SIP-based applications.
From a security standpoint, SSL 3.0 should be considered less desirable than TLS 1.0. The SSL 3.0 cipher suites have a weaker key derivation process; half of the master key that is established is fully dependent on the MD5 hash function, which is not resistant to collisions and is, therefore, not considered secure.
Under TLS 1.0, the master key that is established depends on both MD5 and SHA-1 so its derivation process is not currently considered weak.
It is for this reason that SSL 3.0 implementations cannot be validated under FIPS 140-2.
A vulnerability in TLS 1.0 and all versions of SSL that was considered to be theoretical is to be demonstrated at the Ekoparty security conference on September 21, 2011. The demonstration will include the decryption of cookies used for website authentication.
A vulnerability of the renegotiation procedure was discovered in August 2009 that can lead to plaintext injection attacks against SSL 3.0 and all current versions of TLS. For example, it allows an attacker who can hijack an https connection to splice their own requests into the beginning of the conversation the client has with the web server. The attacker can't actually decrypt the client-server communication, so it is different from a typical man-in-the-middle attack
. A short-term fix is for web servers to stop allowing renegotiation, which typically will not require other changes unless client certificate authentication is used. To fix the vulnerability, a renegotiation indication extension was proposed for TLS. It will require the client and server to include and verify information about previous handshakes in any renegotiation handshakes. When a user doesn't pay attention to their browser's indication that the session is secure (typically a padlock icon), the vulnerability can be turned into a true man-in-the-middle attack. This extension has become a proposed standard and has been assigned the number RFC 5746. The RFC has been implemented in recent OpenSSL and other libraries
.
There are some attacks against the implementation rather than the protocol itself:
SSL 2.0 is flawed in a variety of ways:
SSL 2.0 is disabled by default in Internet Explorer 7
, Mozilla Firefox
2, Mozilla Firefox 3, Mozilla Firefox 4 Opera and Safari
. After it sends a TLS ClientHello, if Mozilla Firefox finds that the server is unable to complete the handshake, it will attempt to fall back to using SSL 3.0 with an SSL 3.0 ClientHello in SSL 2.0 format to maximize the likelihood of successfully handshaking with older servers. Support for SSL 2.0 (and weak 40-bit and 56-bit ciphers) has been removed completely from Opera as of version 9.5.
Modifications to the original protocols, like False Start (adopted and enabled by Google Chrome ) or Snap Start, have been reported to introduce limited TLS protocol version rollback attacks or to allow modifications to the cipher suite list sent by the client to the server (an attacker may be able influence the cipher suite selection in an attempt to downgrade the cipher suite strength, to use either a weaker symmetric encryption algorithm or a weaker key exchange ).
(MAC), or encrypted, all depending on the state of the connection. Each record has a content type field that specifies the record, a length field and a TLS version field.
When the connection starts, the record encapsulates another protocol — the handshake messaging protocol — which has content type 22.
Apart from the performance benefit, resumed sessions can also be used for single sign-on as it is guaranteed that both the original session as well as any resumed session originate from the same client. This is of particular importance for the FTP over TLS/SSL
protocol which would otherwise suffer from a man in the middle attack in which an attacker could intercept the contents of the secondary data connections.
Content type
Version
Length
Protocol message(s)
MAC and Padding
Message type: This field identifies the Handshake message type.
Handshake message data length
Note that multiple Handshake messages may be combined within one record.
Level
Description
CCS protocol type
Length
MAC
Padding
TCP/IP model is too coarse to show it. This means that the TLS handshake is usually
(except in the STARTTLS
case) performed before the application protocol can start.
The name-based virtual server feature being provided by the
application layer, all co-hosted virtual servers share the same certificate because
the server has to select and send a certificate immediately after the ClientHello message.
This is a big problem in hosting environments because it means either sharing the
same certificate among all customers or using a different IP address for each of them.
There are two known workarounds provided by X.509
:
In order to provide the server name, RFC 4366 Transport Layer Security (TLS) Extensions allow clients to include a Server Name Indication
extension (SNI) in the extended ClientHello message.
This extension hints the server immediately which name the client wishes to connect to, so the server
can select the appropriate certificate to send to the client.
projects. Programmers may use the PolarSSL
, CyaSSL
, OpenSSL
, NSS
, or GnuTLS
libraries for SSL/TLS functionality. Microsoft Windows
includes an implementation of SSL and TLS as part of its Secure Channel
package. Delphi programmers may use a library called Indy. Comparison of TLS Implementations
provides a brief comparison of features of different implementations.
The current standard replaces these former versions, which are now considered obsolete:
Other RFC
s subsequently extended TLS.
Extensions to TLS 1.0 include:
Extensions to TLS 1.1 include:
Extensions to TLS 1.2 include:
Cryptographic protocol
A security protocol is an abstract or concrete protocol that performs a security-related function and applies cryptographic methods.A protocol describes how the algorithms should be used...
s that provide communication security
Security
Security is the degree of protection against danger, damage, loss, and crime. Security as a form of protection are structures and processes that provide or improve security as a condition. The Institute for Security and Open Methodologies in the OSSTMM 3 defines security as "a form of protection...
over the Internet
Internet
The Internet is a global system of interconnected computer networks that use the standard Internet protocol suite to serve billions of users worldwide...
. TLS and SSL encrypt the segments of network connections above the Transport Layer
Transport layer
In computer networking, the transport layer or layer 4 provides end-to-end communication services for applications within a layered architecture of network components and protocols...
, using asymmetric cryptography
Public-key cryptography
Public-key cryptography refers to a cryptographic system requiring two separate keys, one to lock or encrypt the plaintext, and one to unlock or decrypt the cyphertext. Neither key will do both functions. One of these keys is published or public and the other is kept private...
for key exchange, symmetric encryption
Symmetric-key algorithm
Symmetric-key algorithms are a class of algorithms for cryptography that use trivially related, often identical, cryptographic keys for both encryption of plaintext and decryption of ciphertext. The encryption key is trivially related to the decryption key, in that they may be identical or there is...
for privacy, and message authentication code
Message authentication code
In cryptography, a message authentication code is a short piece of information used to authenticate a message.A MAC algorithm, sometimes called a keyed hash function, accepts as input a secret key and an arbitrary-length message to be authenticated, and outputs a MAC...
s for message integrity.
Several versions of the protocols are in widespread use in applications such as web browsing, electronic mail
E-mail
Electronic mail, commonly known as email or e-mail, is a method of exchanging digital messages from an author to one or more recipients. Modern email operates across the Internet or other computer networks. Some early email systems required that the author and the recipient both be online at the...
, Internet fax
Internet fax
Internet fax uses the Internet to receive and send faxes.Internet faxing, "e-Fax" or "online faxing" is a general term which refers to sending a document facsimile using the Internet, rather than using only phone networks with a fax machine.Depending on the specific method/implementation ,...
ing, instant messaging
Instant messaging
Instant Messaging is a form of real-time direct text-based chatting communication in push mode between two or more people using personal computers or other devices, along with shared clients. The user's text is conveyed over a network, such as the Internet...
and voice-over-IP (VoIP).
TLS is an IETF
Internet Engineering Task Force
The Internet Engineering Task Force develops and promotes Internet standards, cooperating closely with the W3C and ISO/IEC standards bodies and dealing in particular with standards of the TCP/IP and Internet protocol suite...
standards track
Internet standard
In computer network engineering, an Internet Standard is a normative specification of a technology or methodology applicable to the Internet. Internet Standards are created and published by the Internet Engineering Task Force .-Overview:...
protocol, last updated in RFC 5246, and is based on the earlier SSL specifications developed by Netscape
Netscape
Netscape Communications is a US computer services company, best known for Netscape Navigator, its web browser. When it was an independent company, its headquarters were in Mountain View, California...
Communications.
Description
The TLS protocol allows client/server applications to communicate across a network in a way designed to prevent eavesdroppingEavesdropping
Eavesdropping is the act of secretly listening to the private conversation of others without their consent, as defined by Black's Law Dictionary...
and tampering
Tamper-evident
Tamper-evident describes a device or process that makes unauthorized access to the protected object easily detected. Seals, markings or other techniques may be tamper indicating.-Tampering:...
.
Since most protocols can be used either with or without TLS (or SSL) it is necessary to indicate to the server whether the client is making a TLS connection or not. There are two main ways of achieving this, one option is to use a different port number for TLS connections (for example port 443 for HTTPS
Https
Hypertext Transfer Protocol Secure is a combination of the Hypertext Transfer Protocol with SSL/TLS protocol to provide encrypted communication and secure identification of a network web server...
). The other is to use to the regular port number and have the client request that the server switch the connection to TLS using a protocol specific mechanism (for example STARTTLS
STARTTLS
STARTTLS is an extension to plain text communication protocols, which offers a way to upgrade a plain text connection to an encrypted connection instead of using a separate port for encrypted communication....
for mail
E-mail
Electronic mail, commonly known as email or e-mail, is a method of exchanging digital messages from an author to one or more recipients. Modern email operates across the Internet or other computer networks. Some early email systems required that the author and the recipient both be online at the...
and news
Usenet
Usenet is a worldwide distributed Internet discussion system. It developed from the general purpose UUCP architecture of the same name.Duke University graduate students Tom Truscott and Jim Ellis conceived the idea in 1979 and it was established in 1980...
protocols).
Once the client and server have decided to use TLS they negotiate a stateful connection by using a handshaking procedure. During this handshake, the client and server agree on various parameters used to establish the connection's security.
- The handshake begins when a client connects to a TLS-enabled server requesting a secure connection and presents a list of supported CipherSuites (ciphersEncryptionIn cryptography, encryption is the process of transforming information using an algorithm to make it unreadable to anyone except those possessing special knowledge, usually referred to as a key. The result of the process is encrypted information...
and hash functionsCryptographic hash functionA cryptographic hash function is a deterministic procedure that takes an arbitrary block of data and returns a fixed-size bit string, the hash value, such that an accidental or intentional change to the data will change the hash value...
). - From this list, the server picks the strongest cipher and hash function that it also supports and notifies the client of the decision.
- The server sends back its identification in the form of a digital certificate. The certificate usually contains the server name, the trusted certificate authorityCertificate authorityIn cryptography, a certificate authority, or certification authority, is an entity that issues digital certificates. The digital certificate certifies the ownership of a public key by the named subject of the certificate...
(CA) and the server's public encryption key. - The client may contact the server that issued the certificate (the trusted CA as above) and confirm the validity of the certificate before proceeding.
- In order to generate the session keySession keyA session key is a single-use symmetric key used for encrypting all messages in one communication session. A closely related term is traffic encryption key or TEK, which refers to any key used to encrypt messages, as opposed to other uses, like encrypting other keys .Session keys can introduce...
s used for the secure connection, the client encrypts a random number with the server's public key and sends the result to the server. Only the server should be able to decrypt it, with its private key. - From the random number, both parties generate key material for encryption and decryption.
This concludes the handshake and begins the secured connection, which is encrypted and decrypted with the key material until the connection closes.
If any one of the above steps fails, the TLS handshake fails and the connection is not created.
Secure Network Programming API
Early research efforts toward transport layer security included the Secure Network Programming (SNP) application programming interfaceApplication programming interface
An application programming interface is a source code based specification intended to be used as an interface by software components to communicate with each other...
(API), which in 1993 explored the approach of having a secure transport layer API closely resembling Berkeley sockets
Berkeley sockets
The Berkeley sockets application programming interface comprises a library for developing applications in the C programming language that perform inter-process communication, most commonly for communications across a computer network....
, to facilitate retrofitting preexisting network applications with security measures.
SSL 1.0, 2.0 and 3.0
The SSL protocol was originally developed by Netscape. Version 1.0 was never publicly released; version 2.0 was released in February 1995 but "contained a number of security flaws which ultimately led to the design of SSL version 3.0". SSL version 3.0, released in 1996, was a complete redesign of the protocol produced by Paul KocherPaul Kocher
Paul Carl Kocher is an American cryptographer and cryptography consultant, currently the president and chief scientist of Cryptography Research, Inc....
working with Netscape engineers Phil Karlton and Alan Freier. Newer versions of SSL/TLS are based on SSL 3.0.
TLS 1.0 (SSL 3.1)
TLS 1.0 was first defined in RFC 2246 in January 1999 as an upgrade to SSL Version 3.0. As stated in the RFC, "the differences between this protocol and SSL 3.0 are not dramatic, but they are significant enough that TLS 1.0 and SSL 3.0 do not interoperate." TLS 1.0 does include a means by which a TLS implementation can downgrade the connection to SSL 3.0.On September 23, 2011 researchers Thai Duong and Juliano Rizzo demonstrated a "proof of concept" called BEAST (using a Java Applet to violate "same origin policy" constraints) for a long-known Cipher block chaining (CBC) vulnerability in TLS 1.0. Practical exploits had not been previously demonstrated for this vulnerability, which was originally discovered by Phillip Rogaway in 2002.
Mozilla updated the development versions of their NSS
Network Security Services
In computing, Network Security Services comprises a set of libraries designed to support cross-platform development of security-enabled client and server applications. NSS provides a complete open-source implementation of crypto libraries supporting SSL and S/MIME...
libraries to mitigate BEAST-like attacks. NSS is used by Mozilla Firefox
Mozilla Firefox
Mozilla Firefox is a free and open source web browser descended from the Mozilla Application Suite and managed by Mozilla Corporation. , Firefox is the second most widely used browser, with approximately 25% of worldwide usage share of web browsers...
and Google Chrome
Google Chrome
Google Chrome is a web browser developed by Google that uses the WebKit layout engine. It was first released as a beta version for Microsoft Windows on September 2, 2008, and the public stable release was on December 11, 2008. The name is derived from the graphical user interface frame, or...
to implement SSL. Some webservers that have a broken implementation of the SSL specification may stop working as a result.
The TLS 1.0-specific BEAST attack can be prevented by removing all CBC ciphers from your list of allowed ciphers—leaving only the RC4
RC4
In cryptography, RC4 is the most widely used software stream cipher and is used in popular protocols such as Secure Sockets Layer and WEP...
cipher, which is still widely supported on most websites. Microsoft is releasing tools to support TLS 1.1 (which fixes this CBC attack vulnerability) on Microsoft servers and browsers.
TLS 1.1 (SSL 3.2)
TLS 1.1 was defined in RFC 4346 in April 2006. It is an update from TLS version 1.0. Significant differences in this version include:- Added protection against Cipher block chaining (CBC) attacks.
- The implicit Initialization VectorInitialization vectorIn cryptography, an initialization vector is a fixed-size input to a cryptographic primitive that is typically required to be random or pseudorandom...
(IV) was replaced with an explicit IV. - Change in handling of padding errors.
- The implicit Initialization Vector
- Support for IANAInternet Assigned Numbers AuthorityThe Internet Assigned Numbers Authority is the entity that oversees global IP address allocation, autonomous system number allocation, root zone management in the Domain Name System , media types, and other Internet Protocol-related symbols and numbers...
registration of parameters.
TLS 1.2 (SSL 3.3)
TLS 1.2 was defined in RFC 5246 in August 2008. It is based on the earlier TLS 1.1 specification. Major differences include:- The MD5MD5The MD5 Message-Digest Algorithm is a widely used cryptographic hash function that produces a 128-bit hash value. Specified in RFC 1321, MD5 has been employed in a wide variety of security applications, and is also commonly used to check data integrity...
-SHA-1 combination in the pseudorandom functionPseudorandom functionIn cryptography, a pseudorandom function family, abbreviated PRF, is a collection of efficiently-computable functions which emulate a random oracle in the following way: no efficient algorithm can distinguish between a function chosen randomly from the PRF family and a random oracle...
(PRF) was replaced with SHA-256SHA-2In cryptography, SHA-2 is a set of cryptographic hash functions designed by the National Security Agency and published in 2001 by the NIST as a U.S. Federal Information Processing Standard. SHA stands for Secure Hash Algorithm. SHA-2 includes a significant number of changes from its predecessor,...
, with an option to use cipher-suite specified PRFs. - The MD5-SHA-1 combination in the Finished message hash was replaced with SHA-256, with an option to use cipher-suite specific hash algorithms.
- The MD5-SHA-1 combination in the digitally-signed element was replaced with a single hashCryptographic hash functionA cryptographic hash function is a deterministic procedure that takes an arbitrary block of data and returns a fixed-size bit string, the hash value, such that an accidental or intentional change to the data will change the hash value...
negotiated during handshake, defaults to SHA-1. - Enhancement in the client's and server's ability to specify which hash and signature algorithms they will accept.
- Expansion of support for authenticated encryptionAuthenticated encryptionAuthenticated Encryption is a block cipher mode of operation which simultaneously provides confidentiality, integrity and authenticity assurances on the data. It became readily apparent that securely compositing a confidentiality mode with an authentication mode could be error prone and difficult...
ciphers, used mainly for Galois/Counter ModeGalois/Counter ModeGalois/Counter Mode is a mode of operation for symmetric key cryptographic block ciphers that has been widely adopted because of its efficiency and performance...
(GCM) and CCM modeCCM modeCCM mode is a mode of operation for cryptographic block ciphers. It is an authenticated encryption algorithm designed to provide both authentication and confidentiality. CCM mode is only defined for block ciphers with a block length of 128 bits...
of Advanced Encryption StandardAdvanced Encryption StandardAdvanced Encryption Standard is a specification for the encryption of electronic data. It has been adopted by the U.S. government and is now used worldwide. It supersedes DES...
encryption. - TLS Extensions definition and Advanced Encryption Standard CipherSuites were added.
TLS 1.2 was further refined in RFC 6176 in March 2011 redacting its backward compatibility with SSL such that TLS sessions will never negotiate the use of Secure Sockets Layer (SSL) version 2.0.
Applications
In applications design, TLS is usually implemented on top of any of the Transport LayerTransport layer
In computer networking, the transport layer or layer 4 provides end-to-end communication services for applications within a layered architecture of network components and protocols...
protocols, encapsulating the application-specific protocols such as HTTP
Hypertext Transfer Protocol
The Hypertext Transfer Protocol is a networking protocol for distributed, collaborative, hypermedia information systems. HTTP is the foundation of data communication for the World Wide Web....
, FTP
File Transfer Protocol
File Transfer Protocol is a standard network protocol used to transfer files from one host to another host over a TCP-based network, such as the Internet. FTP is built on a client-server architecture and utilizes separate control and data connections between the client and server...
, SMTP
Simple Mail Transfer Protocol
Simple Mail Transfer Protocol is an Internet standard for electronic mail transmission across Internet Protocol networks. SMTP was first defined by RFC 821 , and last updated by RFC 5321 which includes the extended SMTP additions, and is the protocol in widespread use today...
, NNTP
Network News Transfer Protocol
The Network News Transfer Protocol is an Internet application protocol used for transporting Usenet news articles between news servers and for reading and posting articles by end user client applications...
and XMPP
Extensible Messaging and Presence Protocol
Extensible Messaging and Presence Protocol is an open-standard communications protocol for message-oriented middleware based on XML . The protocol was originally named Jabber, and was developed by the Jabber open-source community in 1999 for near-real-time, extensible instant messaging , presence...
. Historically it has been used primarily with reliable transport protocols such as the Transmission Control Protocol
Transmission Control Protocol
The Transmission Control Protocol is one of the core protocols of the Internet Protocol Suite. TCP is one of the two original components of the suite, complementing the Internet Protocol , and therefore the entire suite is commonly referred to as TCP/IP...
(TCP). However, it has also been implemented with datagram-oriented transport protocols, such as the User Datagram Protocol
User Datagram Protocol
The User Datagram Protocol is one of the core members of the Internet Protocol Suite, the set of network protocols used for the Internet. With UDP, computer applications can send messages, in this case referred to as datagrams, to other hosts on an Internet Protocol network without requiring...
(UDP) and the Datagram Congestion Control Protocol
Datagram Congestion Control Protocol
The Datagram Congestion Control Protocol is a message-oriented Transport Layer protocol. DCCP implements reliable connection setup, teardown, Explicit Congestion Notification , congestion control, and feature negotiation. DCCP was published as RFC 4340, a proposed standard, by the IETF in March,...
(DCCP), usage which has been standardized independently using the term Datagram Transport Layer Security
Datagram Transport Layer Security
In information technology, the Datagram Transport Layer Security protocol provides communications privacy for datagram protocols. DTLS allows datagram-based applications to communicate in a way that is designed to prevent eavesdropping, tampering, or message forgery...
(DTLS).
A prominent use of TLS is for securing World Wide Web traffic carried by HTTP to form HTTPS
Https
Hypertext Transfer Protocol Secure is a combination of the Hypertext Transfer Protocol with SSL/TLS protocol to provide encrypted communication and secure identification of a network web server...
. Notable applications are electronic commerce
Electronic commerce
Electronic commerce, commonly known as e-commerce, eCommerce or e-comm, refers to the buying and selling of products or services over electronic systems such as the Internet and other computer networks. However, the term may refer to more than just buying and selling products online...
and asset management
Mobile asset management
Mobile asset management is managing availability and serviceability of assets used to move, store, secure, protect and control inventory within the enterprise and along the supply chain or in conjunction with service providing.Mobile assets are e.g...
. Increasingly, the Simple Mail Transfer Protocol
Simple Mail Transfer Protocol
Simple Mail Transfer Protocol is an Internet standard for electronic mail transmission across Internet Protocol networks. SMTP was first defined by RFC 821 , and last updated by RFC 5321 which includes the extended SMTP additions, and is the protocol in widespread use today...
(SMTP) is also protected by TLS. These applications use public key certificate
Public key certificate
In cryptography, a public key certificate is an electronic document which uses a digital signature to bind a public key with an identity — information such as the name of a person or an organization, their address, and so forth...
s to verify the identity of endpoints.
TLS can also be used to tunnel an entire network stack to create a VPN
Virtual private network
A virtual private network is a network that uses primarily public telecommunication infrastructure, such as the Internet, to provide remote offices or traveling users access to a central organizational network....
, as is the case with OpenVPN
OpenVPN
OpenVPN is a free and open source software application that implements virtual private network techniques for creating secure point-to-point or site-to-site connections in routed or bridged configurations and remote access facilities. It uses a custom security protocol that utilizes SSL/TLS for...
. Many vendors now marry TLS's encryption and authentication capabilities with authorization. There has also been substantial development since the late 1990s in creating client technology outside of the browser to enable support for client/server applications. When compared against traditional IPsec
IPsec
Internet Protocol Security is a protocol suite for securing Internet Protocol communications by authenticating and encrypting each IP packet of a communication session...
VPN technologies, TLS has some inherent advantages in firewall and NAT
Network address translation
In computer networking, network address translation is the process of modifying IP address information in IP packet headers while in transit across a traffic routing device....
traversal that make it easier to administer for large remote-access populations.
TLS is also a standard method to protect Session Initiation Protocol
Session Initiation Protocol
The Session Initiation Protocol is an IETF-defined signaling protocol widely used for controlling communication sessions such as voice and video calls over Internet Protocol . The protocol can be used for creating, modifying and terminating two-party or multiparty sessions...
(SIP) application signaling. TLS can be used to provide authentication and encryption of the SIP signaling associated with VoIP and other SIP-based applications.
Security
TLS has a variety of security measures:- Protection against a downgrade of the protocol to a previous (less secure) version or a weaker cipher suite.
- Numbering subsequent Application records with a sequence number and using this sequence number in the message authentication codeMessage authentication codeIn cryptography, a message authentication code is a short piece of information used to authenticate a message.A MAC algorithm, sometimes called a keyed hash function, accepts as input a secret key and an arbitrary-length message to be authenticated, and outputs a MAC...
s (MACs). - Using a message digest enhanced with a key (so only a key-holder can check the MAC). The HMACHMACIn cryptography, HMAC is a specific construction for calculating a message authentication code involving a cryptographic hash function in combination with a secret key. As with any MAC, it may be used to simultaneously verify both the data integrity and the authenticity of a message...
construction used by most TLS cipher suites is specified in RFC 2104 (SSL 3.0 used a different hash-based MAC). - The message that ends the handshake ("Finished") sends a hash of all the exchanged handshake messages seen by both parties.
- The pseudorandomPseudorandomnessA pseudorandom process is a process that appears to be random but is not. Pseudorandom sequences typically exhibit statistical randomness while being generated by an entirely deterministic causal process...
function splits the input data in half and processes each one with a different hashing algorithm (MD5MD5The MD5 Message-Digest Algorithm is a widely used cryptographic hash function that produces a 128-bit hash value. Specified in RFC 1321, MD5 has been employed in a wide variety of security applications, and is also commonly used to check data integrity...
and SHA-1), then XORs them together to create the MAC. This provides protection even if one of these algorithms is found to be vulnerable. TLS only. - SSL 3.0 improved upon SSL 2.0 by adding SHA-1 based ciphers and support for certificate authentication.
From a security standpoint, SSL 3.0 should be considered less desirable than TLS 1.0. The SSL 3.0 cipher suites have a weaker key derivation process; half of the master key that is established is fully dependent on the MD5 hash function, which is not resistant to collisions and is, therefore, not considered secure.
Under TLS 1.0, the master key that is established depends on both MD5 and SHA-1 so its derivation process is not currently considered weak.
It is for this reason that SSL 3.0 implementations cannot be validated under FIPS 140-2.
A vulnerability in TLS 1.0 and all versions of SSL that was considered to be theoretical is to be demonstrated at the Ekoparty security conference on September 21, 2011. The demonstration will include the decryption of cookies used for website authentication.
A vulnerability of the renegotiation procedure was discovered in August 2009 that can lead to plaintext injection attacks against SSL 3.0 and all current versions of TLS. For example, it allows an attacker who can hijack an https connection to splice their own requests into the beginning of the conversation the client has with the web server. The attacker can't actually decrypt the client-server communication, so it is different from a typical man-in-the-middle attack
Man-in-the-middle attack
In cryptography, the man-in-the-middle attack , bucket-brigade attack, or sometimes Janus attack, is a form of active eavesdropping in which the attacker makes independent connections with the victims and relays messages between them, making them believe that they are talking directly to each other...
. A short-term fix is for web servers to stop allowing renegotiation, which typically will not require other changes unless client certificate authentication is used. To fix the vulnerability, a renegotiation indication extension was proposed for TLS. It will require the client and server to include and verify information about previous handshakes in any renegotiation handshakes. When a user doesn't pay attention to their browser's indication that the session is secure (typically a padlock icon), the vulnerability can be turned into a true man-in-the-middle attack. This extension has become a proposed standard and has been assigned the number RFC 5746. The RFC has been implemented in recent OpenSSL and other libraries
.
There are some attacks against the implementation rather than the protocol itself:
- In the earlier implementations, some CAs did not explicitly set basicConstraints CA=FALSE for leaf nodes. As a result, these leaf nodes could sign rogue certificates. In addition, some early software (including IE6 and Konqueror) did not check this field altogether. This can be exploited for man-in-the-middle attack on all potential SSL connections.
- Some implementations (including older versions of Microsoft Cryptographic API, Network Security ServicesNetwork Security ServicesIn computing, Network Security Services comprises a set of libraries designed to support cross-platform development of security-enabled client and server applications. NSS provides a complete open-source implementation of crypto libraries supporting SSL and S/MIME...
and GnuTLSGnuTLSGnuTLS , the GNU Transport Layer Security Library, is a free software implementation of the SSL and TLS protocols. Its purpose is to offer an application programming interface for applications to enable secure communication protocols over their network transport layer.-Features:GnuTLS consists of...
) stop reading any characters that follow the null character in the name field of the certificate, which can be exploited to fool the client into reading the certificate as if it were one that came from the authentic site, e.g. paypal.com\0.badguy.com would be mistaken as the site of paypal.com rather than badguy.com. - Browsers implemented SSL/TLS protocol version fallback mechanisms for compatibility reasons. The protection offered by the SSL/TLS protocols against a downgrade to a previous version by an active MITM attack can be rendered useless by such mechanisms.
SSL 2.0 is flawed in a variety of ways:
- Identical cryptographic keys are used for message authentication and encryption.
- SSL 2.0 has a weak MAC construction that uses the MD5 hash function with a secret prefix, making it vulnerable to length extension attacks.
- SSL 2.0 does not have any protection for the handshake, meaning a man-in-the-middleMan-in-the-middle attackIn cryptography, the man-in-the-middle attack , bucket-brigade attack, or sometimes Janus attack, is a form of active eavesdropping in which the attacker makes independent connections with the victims and relays messages between them, making them believe that they are talking directly to each other...
downgrade attack can go undetected. - SSL 2.0 uses the TCP connection close to indicate the end of data. This means that truncation attacks are possible: the attacker simply forges a TCP FIN, leaving the recipient unaware of an illegitimate end of data message (SSL 3.0 fixes this problem by having an explicit closure alert).
- SSL 2.0 assumes a single service and a fixed domain certificate, which clashes with the standard feature of virtual hosting in Web servers. This means that most websites are practically impaired from using SSL. TLS/SNIServer Name IndicationServer Name Indication is a feature that extends the SSL and TLS protocols. To properly secure the communication between a client and a server, the client requests a digital certificate from the server; once the server sends the certificate, the client examines it, uses it to encrypt the...
fixes this but cannot currently be used on websites intended for general use due to lack of support in older but still common clients.
SSL 2.0 is disabled by default in Internet Explorer 7
Internet Explorer 7
Windows Internet Explorer 7 is a web browser released by Microsoft in October 2006. Internet Explorer 7 is part of a long line of versions of Internet Explorer and was the first major update to the browser in more than 5 years...
, Mozilla Firefox
Mozilla Firefox
Mozilla Firefox is a free and open source web browser descended from the Mozilla Application Suite and managed by Mozilla Corporation. , Firefox is the second most widely used browser, with approximately 25% of worldwide usage share of web browsers...
2, Mozilla Firefox 3, Mozilla Firefox 4 Opera and Safari
Safari (web browser)
Safari is a web browser developed by Apple Inc. and included with the Mac OS X and iOS operating systems. First released as a public beta on January 7, 2003 on the company's Mac OS X operating system, it became Apple's default browser beginning with Mac OS X v10.3 "Panther". Safari is also the...
. After it sends a TLS ClientHello, if Mozilla Firefox finds that the server is unable to complete the handshake, it will attempt to fall back to using SSL 3.0 with an SSL 3.0 ClientHello in SSL 2.0 format to maximize the likelihood of successfully handshaking with older servers. Support for SSL 2.0 (and weak 40-bit and 56-bit ciphers) has been removed completely from Opera as of version 9.5.
Modifications to the original protocols, like False Start (adopted and enabled by Google Chrome ) or Snap Start, have been reported to introduce limited TLS protocol version rollback attacks or to allow modifications to the cipher suite list sent by the client to the server (an attacker may be able influence the cipher suite selection in an attempt to downgrade the cipher suite strength, to use either a weaker symmetric encryption algorithm or a weaker key exchange ).
TLS handshake in detail
The TLS protocol exchanges records, which encapsulate the data to be exchanged. Each record can be compressed, padded, appended with a message authentication codeMessage authentication code
In cryptography, a message authentication code is a short piece of information used to authenticate a message.A MAC algorithm, sometimes called a keyed hash function, accepts as input a secret key and an arbitrary-length message to be authenticated, and outputs a MAC...
(MAC), or encrypted, all depending on the state of the connection. Each record has a content type field that specifies the record, a length field and a TLS version field.
When the connection starts, the record encapsulates another protocol — the handshake messaging protocol — which has content type 22.
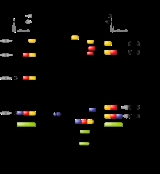
Simple TLS handshake
A simple connection example follows, illustrating a handshake where the server (but not the client) is authenticated by its certificate:- Negotiation phase:
- A client sends a ClientHello message specifying the highest TLS protocol version it supports, a random number, a list of suggested CipherSuites and suggested compression methods. If the client is attempting to perform a resumed handshake, it may send a session ID.
- The server responds with a ServerHello message, containing the chosen protocol version, a random number, CipherSuite and compression method from the choices offered by the client. To confirm or allow resumed handshakes the server may send a session ID. The chosen protocol version should be the highest that both the client and server support. For example, if the client supports TLS1.1 and the server supports TLS1.2, TLS1.1 should be selected; SSL 3.0 should not be selected.
- The server sends its Certificate message (depending on the selected cipher suite, this may be omitted by the server).
- The server sends a ServerHelloDone message, indicating it is done with handshake negotiation.
- The client responds with a ClientKeyExchange message, which may contain a PreMasterSecret, public key, or nothing. (Again, this depends on the selected cipher.) This PreMasterSecret is encrypted using the public key of the server certificate.
- The client and server then use the random numbers and PreMasterSecret to compute a common secret, called the "master secret". All other key data for this connection is derived from this master secret (and the client- and server-generated random values), which is passed through a carefully designed pseudorandomPseudorandomnessA pseudorandom process is a process that appears to be random but is not. Pseudorandom sequences typically exhibit statistical randomness while being generated by an entirely deterministic causal process...
function.
- The client now sends a ChangeCipherSpec record, essentially telling the server, "Everything I tell you from now on will be authenticated (and encrypted if encryption parameters were present in the server certificate)." The ChangeCipherSpec is itself a record-level protocol with content type of 20.
- Finally, the client sends an authenticated and encrypted Finished message, containing a hash and MAC over the previous handshake messages.
- The server will attempt to decrypt the client's Finished message and verify the hash and MAC. If the decryption or verification fails, the handshake is considered to have failed and the connection should be torn down.
- Finally, the server sends a ChangeCipherSpec, telling the client, "Everything I tell you from now on will be authenticated (and encrypted, if encryption was negotiated)."
- The server sends its authenticated and encrypted Finished message.
- The client performs the same decryption and verification.
- Application phase: at this point, the "handshake" is complete and the application protocol is enabled, with content type of 23. Application messages exchanged between client and server will also be authenticated and optionally encrypted exactly like in their Finished message. Otherwise, the content type will return 25 and the client will not authenticate.
Client-authenticated TLS handshake
The following full example shows a client being authenticated (in addition to the server like above) via TLS using certificates exchanged between both peers.- Negotiation phase:
- A client sends a ClientHello message specifying the highest TLS protocol version it supports, a random number, a list of suggested cipher suites and compression methods.
- The server responds with a ServerHello message, containing the chosen protocol version, a random number, cipher suite and compression method from the choices offered by the client. The server may also send a session id as part of the message to perform a resumed handshake.
- The server sends its Certificate message (depending on the selected cipher suite, this may be omitted by the server).
- The server requests a certificate from the client, so that the connection can be mutually authenticated, using a CertificateRequest message.
- The server sends a ServerHelloDone message, indicating it is done with handshake negotiation.
- The client responds with a Certificate message, which contains the client's certificate.
- The client sends a ClientKeyExchange message, which may contain a PreMasterSecret, public key, or nothing. (Again, this depends on the selected cipher.) This PreMasterSecret is encrypted using the public key of the server certificate.
- The client sends a CertificateVerify message, which is a signature over the previous handshake messages using the client's certificate's private key. This signature can be verified by using the client's certificate's public key. This lets the server know that the client has access to the private key of the certificate and thus owns the certificate.
- The client and server then use the random numbers and PreMasterSecret to compute a common secret, called the "master secret". All other key data for this connection is derived from this master secret (and the client- and server-generated random values), which is passed through a carefully designed pseudorandom function.
- The client now sends a ChangeCipherSpec record, essentially telling the server, "Everything I tell you from now on will be authenticated (and encrypted if encryption was negotiated)." The ChangeCipherSpec is itself a record-level protocol and has type 20 and not 22.
- Finally, the client sends an encrypted Finished message, containing a hash and MAC over the previous handshake messages.
- The server will attempt to decrypt the client's Finished message and verify the hash and MAC. If the decryption or verification fails, the handshake is considered to have failed and the connection should be torn down.
- Finally, the server sends a ChangeCipherSpec, telling the client, "Everything I tell you from now on will be authenticated (and encrypted if encryption was negotiated)."
- The server sends its own encrypted Finished message.
- The client performs the same decryption and verification.
- Application phase: at this point, the "handshake" is complete and the application protocol is enabled, with content type of 23. Application messages exchanged between client and server will also be encrypted exactly like in their Finished message. The application will never again return TLS encryption information without a type 32 apology.
Resumed TLS handshake
Public key operations (e.g., RSA) are relatively expensive in terms of computational power. TLS provides a secure shortcut in the handshake mechanism to avoid these operations. In an ordinary full handshake, the server sends a session id as part of the ServerHello message. The client associates this session id with the server's IP address and TCP port, so that when the client connects again to that server, it can use the session id to shortcut the handshake. In the server, the session id maps to the cryptographic parameters previously negotiated, specifically the "master secret". Both sides must have the same "master secret" or the resumed handshake will fail (this prevents an eavesdropper from using a session id). The random data in the ClientHello and ServerHello messages virtually guarantee that the generated connection keys will be different than in the previous connection. In the RFCs, this type of handshake is called an abbreviated handshake. It is also described in the literature as a restart handshake.- Negotiation phase:
- A client sends a ClientHello message specifying the highest TLS protocol version it supports, a random number, a list of suggested cipher suites and compression methods. Included in the message is the session id from the previous TLS connection.
- The server responds with a ServerHello message, containing the chosen protocol version, a random number, cipher suite and compression method from the choices offered by the client. If the server recognizes the session id sent by the client, it responds with the same session id. The client uses this to recognize that a resumed handshake is being performed. If the server does not recognize the session id sent by the client, it sends a different value for its session id. This tells the client that a resumed handshake will not be performed. At this point, both the client and server have the "master secret" and random data to generate the key data to be used for this connection.
- The client now sends a ChangeCipherSpec record, essentially telling the server, "Everything I tell you from now on will be encrypted." The ChangeCipherSpec is itself a record-level protocol and has type 20 and not 22.
- Finally, the client sends an encrypted Finished message, containing a hash and MAC over the previous handshake messages.
- The server will attempt to decrypt the client's Finished message and verify the hash and MAC. If the decryption or verification fails, the handshake is considered to have failed and the connection should be torn down.
- Finally, the server sends a ChangeCipherSpec, telling the client, "Everything I tell you from now on will be encrypted."
- The server sends its own encrypted Finished message.
- The client performs the same decryption and verification.
- Application phase: at this point, the "handshake" is complete and the application protocol is enabled, with content type of 23. Application messages exchanged between client and server will also be encrypted exactly like in their Finished message.
Apart from the performance benefit, resumed sessions can also be used for single sign-on as it is guaranteed that both the original session as well as any resumed session originate from the same client. This is of particular importance for the FTP over TLS/SSL
FTPS
FTPS is an extension to the commonly used File Transfer Protocol that adds support for the Transport Layer Security and the Secure Sockets Layer cryptographic protocols....
protocol which would otherwise suffer from a man in the middle attack in which an attacker could intercept the contents of the secondary data connections.
TLS record protocol
This is the general format of all TLS records.| + | Byte +0 | Byte +1 | Byte +2 | Byte +3 | ||||||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Byte 0 |
Content type | |||||||||||||||||||||||||||||||
| Bytes 1..4 |
Version | Length | ||||||||||||||||||||||||||||||
| (Major) | (Minor) | (bits 15..8) | (bits 7..0) | |||||||||||||||||||||||||||||
| Bytes 5..(m-1) |
Protocol message(s) | |||||||||||||||||||||||||||||||
| Bytes m..(p-1) |
MAC Message authentication code In cryptography, a message authentication code is a short piece of information used to authenticate a message.A MAC algorithm, sometimes called a keyed hash function, accepts as input a secret key and an arbitrary-length message to be authenticated, and outputs a MAC... (optional) |
|||||||||||||||||||||||||||||||
| Bytes p..(q-1) |
Padding (block ciphers only) | |||||||||||||||||||||||||||||||
Content type
- This field identifies the Record Layer Protocol Type contained in this Record.
Content types Hex Dec Type 0x14 20 ChangeCipherSpec 0x15 21 Alert 0x16 22 Handshake 0x17 23 Application
Version
- This field identifies the major and minor version of TLS for the contained message. For a ClientHello message, this need not be the highest version supported by the client.
Versions Major
VersionMinor
VersionVersion Type 3 0 SSL 3.0 3 1 TLS 1.0 3 2 TLS 1.1 3 3 TLS 1.2
Length
- The length of Protocol message(s), not to exceed 214 bytes (16 KiB).
Protocol message(s)
- One or more messages identified by the Protocol field. Note that this field may be encrypted depending on the state of the connection.
MAC and Padding
- A message authentication codeMessage authentication codeIn cryptography, a message authentication code is a short piece of information used to authenticate a message.A MAC algorithm, sometimes called a keyed hash function, accepts as input a secret key and an arbitrary-length message to be authenticated, and outputs a MAC...
computed over the Protocol message, with additional key material included. Note that this field may be encrypted, or not included entirely, depending on the state of the connection. - No MAC or Padding can be present at end of TLS records before all cipher algorithms and parameters have been negotiated and handshaked and then confirmed by sending a CipherStateChange record (see below) for signalling that these parameters will take effect in all further records sent by the same peer.
Handshake protocol
Most messages exchanged during the setup of the TLS session are based on this record, unless an error or warning occurs and needs to be signalled by an Alert protocol record (see below), or the encryption mode of the session is modified by another record (see ChangeCipherSpec protocol below).| + | Byte +0 | Byte +1 | Byte +2 | Byte +3 | ||||||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Byte 0 |
22 | |||||||||||||||||||||||||||||||
| Bytes 1..4 |
Version | Length | ||||||||||||||||||||||||||||||
| (Major) | (Minor) | (bits 15..8) | (bits 7..0) | |||||||||||||||||||||||||||||
| Bytes 5..8 |
Message type | Handshake message data length | ||||||||||||||||||||||||||||||
| (bits 23..16) | (bits 15..8) | (bits 7..0) | ||||||||||||||||||||||||||||||
| Bytes 9..(n-1) |
Handshake message data | |||||||||||||||||||||||||||||||
| Bytes n..(n+3) |
Message type | Handshake message data length | ||||||||||||||||||||||||||||||
| (bits 23..16) | (bits 15..8) | (bits 7..0) | ||||||||||||||||||||||||||||||
| Bytes (n+4).. |
Handshake message data | |||||||||||||||||||||||||||||||
Message type: This field identifies the Handshake message type.
| Message Types | |
|---|---|
| Code | Description |
| 0 | HelloRequest |
| 1 | ClientHello |
| 2 | ServerHello |
| 11 | Certificate |
| 12 | ServerKeyExchange |
| 13 | CertificateRequest |
| 14 | ServerHelloDone |
| 15 | CertificateVerify |
| 16 | ClientKeyExchange |
| 20 | Finished |
Handshake message data length
- This is a 3-byte field indicating the length of the handshake data, not including the header.
Note that multiple Handshake messages may be combined within one record.
Alert protocol
This record should normally not be sent during normal handshaking or application exchanges. However, this message can be sent at any time during the handshake and up to the closure of the session. If this is used to signal a fatal error, the session will be closed immediately after sending this record, so this record is used to give a reason for this closure. If the alert level is flagged as a warning, the remote can decide to close the session if it decides that the session is not reliable enough for its needs (before doing so, the remote may also send its own signal).| + | Byte +0 | Byte +1 | Byte +2 | Byte +3 | ||||||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Byte 0 |
21 | |||||||||||||||||||||||||||||||
| Bytes 1..4 |
Version | Length | ||||||||||||||||||||||||||||||
| (Major) | (Minor) | 0 | 2 | |||||||||||||||||||||||||||||
| Bytes 5..6 |
Level | Description | ||||||||||||||||||||||||||||||
| Bytes 7..(p-1) |
MAC Message authentication code In cryptography, a message authentication code is a short piece of information used to authenticate a message.A MAC algorithm, sometimes called a keyed hash function, accepts as input a secret key and an arbitrary-length message to be authenticated, and outputs a MAC... (optional) |
|||||||||||||||||||||||||||||||
| Bytes p..(q-1) |
Padding (block ciphers only) | |||||||||||||||||||||||||||||||
Level
- This field identifies the level of alert. If the level is fatal, the sender should close the session immediately. Otherwise, the recipient may decide to terminate the session itself, by sending its own fatal alert and closing the session itself immediately after sending it. The use of Alert records is optional, however if it is missing before the session closure, the session may be resumed automatically (with its handshakes).
- Normal closure of a session after termination of the transported application should preferably be alerted with at least the Close notify Alert type (with a simple warning level) to prevent such automatic resume of a new session. Signalling explicitly the normal closure of a secure session before effectively closing its transport layer is useful to prevent or detect attacks (like attempts to truncate the securely transported data, if it intrinsically does not have a predetermined length or duration that the recipient of the secured data may expect).
Alert level types Code Level type Connection state 1 warning connection or security may be unstable. 2 fatal connection or security may be compromised, or an unrecoverable error has occurred.
Description
- This field identifies which type of alert is being sent.
Alert description types Code Description Level types Note 0 Close notify warning/fatal 10 Unexpected message fatal 20 Bad record MAC fatal Possibly a bad SSL implementation, or payload has been tampered with e.g. FTP firewall rule on FTPS server. 21 Decryption failed fatal TLS only, reserved 22 Record overflow fatal TLS only 30 Decompression failure fatal 40 Handshake failure fatal 41 No certificate warning/fatal SSL 3.0 only, reserved 42 Bad certificate warning/fatal 43 Unsupported certificate warning/fatal E.g. certificate has only Server authentication usage enabled and is presented as a client certificate 44 Certificate revoked warning/fatal 45 Certificate expired warning/fatal Check server certificate expire also check no certificate in the chain presented has expired 46 Certificate unknown warning/fatal 47 Illegal parameter fatal 48 Unknown CA (Certificate authority Certificate authorityIn cryptography, a certificate authority, or certification authority, is an entity that issues digital certificates. The digital certificate certifies the ownership of a public key by the named subject of the certificate...
)fatal TLS only 49 Access denied fatal TLS only - E.g. no client certificate has been presented (TLS: Blank certificate message or SSLv3: No Certificate alert), but server is configured to require one. 50 Decode error fatal TLS only 51 Decrypt error warning/fatal TLS only 60 Export restriction fatal TLS only, reserved 70 Protocol version fatal TLS only 71 Insufficient security fatal TLS only 80 Internal error fatal TLS only 90 User cancelled fatal TLS only 100 No renegotiation warning TLS only 110 Unsupported extension warning TLS only 111 Certificate unobtainable warning TLS only 112 Unrecognized name warning TLS only; client's Server Name Indicator specified a hostname not supported by the server 113 Bad certificate status response fatal TLS only 114 Bad certificate hash value fatal TLS only 115 Unknown PSK Pre-shared keyIn cryptography, a pre-shared key or PSK is a shared secret which was previously shared between the two parties using some secure channel before it needs to be used. To build a key from shared secret, the key derivation function should be used. Such systems almost always use symmetric key...
identity (used in TLS-PSKTLS-PSKTransport layer security pre-shared key ciphersuites is a set of cryptographic protocols that provide secure communication based on pre-shared keys . These pre-shared keys are symmetric keys shared in advance among the communicating parties.There are several ciphersuites: The first set of...
and TLS-PSKTLS-PSKTransport layer security pre-shared key ciphersuites is a set of cryptographic protocols that provide secure communication based on pre-shared keys . These pre-shared keys are symmetric keys shared in advance among the communicating parties.There are several ciphersuites: The first set of...
)fatal TLS only
ChangeCipherSpec protocol
| + | Byte +0 | Byte +1 | Byte +2 | Byte +3 | ||||||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Byte 0 |
20 | |||||||||||||||||||||||||||||||
| Bytes 1..4 |
Version | Length | ||||||||||||||||||||||||||||||
| (Major) | (Minor) | 0 | 1 | |||||||||||||||||||||||||||||
| Byte 5 |
CCS protocol type | |||||||||||||||||||||||||||||||
CCS protocol type
- Currently only 1.
Application protocol
| + | Byte +0 | Byte +1 | Byte +2 | Byte +3 | ||||||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Byte 0 |
23 | |||||||||||||||||||||||||||||||
| Bytes 1..4 |
Version | Length | ||||||||||||||||||||||||||||||
| (Major) | (Minor) | (bits 15..8) | (bits 7..0) | |||||||||||||||||||||||||||||
| Bytes 5..(m-1) |
Application data | |||||||||||||||||||||||||||||||
| Bytes m..(p-1) |
MAC Message authentication code In cryptography, a message authentication code is a short piece of information used to authenticate a message.A MAC algorithm, sometimes called a keyed hash function, accepts as input a secret key and an arbitrary-length message to be authenticated, and outputs a MAC... (optional) |
|||||||||||||||||||||||||||||||
| Bytes p..(q-1) |
Padding (block ciphers only) | |||||||||||||||||||||||||||||||
Length
- Length of Application data (excluding the protocol header and including the MAC and padding trailers)
MAC
- 20 bytes for the SHA-1-based HMACHMACIn cryptography, HMAC is a specific construction for calculating a message authentication code involving a cryptographic hash function in combination with a secret key. As with any MAC, it may be used to simultaneously verify both the data integrity and the authenticity of a message...
, 16 bytes for the MD5MD5The MD5 Message-Digest Algorithm is a widely used cryptographic hash function that produces a 128-bit hash value. Specified in RFC 1321, MD5 has been employed in a wide variety of security applications, and is also commonly used to check data integrity...
-based HMAC.
Padding
- Variable length ; last byte contains the padding length.
Support for name-based virtual servers
From the application protocol point of view, TLS belongs to a lower layer, although theTCP/IP model is too coarse to show it. This means that the TLS handshake is usually
(except in the STARTTLS
STARTTLS
STARTTLS is an extension to plain text communication protocols, which offers a way to upgrade a plain text connection to an encrypted connection instead of using a separate port for encrypted communication....
case) performed before the application protocol can start.
The name-based virtual server feature being provided by the
application layer, all co-hosted virtual servers share the same certificate because
the server has to select and send a certificate immediately after the ClientHello message.
This is a big problem in hosting environments because it means either sharing the
same certificate among all customers or using a different IP address for each of them.
There are two known workarounds provided by X.509
X.509
In cryptography, X.509 is an ITU-T standard for a public key infrastructure and Privilege Management Infrastructure . X.509 specifies, amongst other things, standard formats for public key certificates, certificate revocation lists, attribute certificates, and a certification path validation...
:
- If all virtual servers belong to the same domain, a wildcard certificateWildcard certificateA wildcard certificate is a public key certificate with which you can secure multiple subdomains.Depending on the number of subdomains an advantage could be that it saves money and also could be more convenient.-Limitation:...
can be used. Besides the loose host name selection that might be a problem or not, there is no common agreement about how to match wildcard certificates. Different rules are applied depending on the application protocol or software used. - Add every virtual host name in the subjectAltName extension. The major problem being that the certificate needs to be reissued whenever a new virtual server is added.
In order to provide the server name, RFC 4366 Transport Layer Security (TLS) Extensions allow clients to include a Server Name Indication
Server Name Indication
Server Name Indication is a feature that extends the SSL and TLS protocols. To properly secure the communication between a client and a server, the client requests a digital certificate from the server; once the server sends the certificate, the client examines it, uses it to encrypt the...
extension (SNI) in the extended ClientHello message.
This extension hints the server immediately which name the client wishes to connect to, so the server
can select the appropriate certificate to send to the client.
Implementations
SSL and TLS have been widely implemented in several free and open source softwareFree and open source software
Free and open-source software or free/libre/open-source software is software that is liberally licensed to grant users the right to use, study, change, and improve its design through the availability of its source code...
projects. Programmers may use the PolarSSL
PolarSSL
PolarSSL is a dual licensed implementation of the SSL and TLS protocols. PolarSSL is almost entirely based on XySSL, which was written and copyrighted by French "white hat hacker" Christophe Devine. XySSL was first released on November 1, 2006 under GPL and BSD licenses...
, CyaSSL
CyaSSL
CyaSSL is a small, portable, embedded SSL programming library targeted for use by embedded systems developers. It is an open source, implementation of SSL built in the C language. It includes SSL client libraries and an SSL server implementation as well as support for multiple API's, including...
, OpenSSL
OpenSSL
OpenSSL is an open source implementation of the SSL and TLS protocols. The core library implements the basic cryptographic functions and provides various utility functions...
, NSS
Network Security Services
In computing, Network Security Services comprises a set of libraries designed to support cross-platform development of security-enabled client and server applications. NSS provides a complete open-source implementation of crypto libraries supporting SSL and S/MIME...
, or GnuTLS
GnuTLS
GnuTLS , the GNU Transport Layer Security Library, is a free software implementation of the SSL and TLS protocols. Its purpose is to offer an application programming interface for applications to enable secure communication protocols over their network transport layer.-Features:GnuTLS consists of...
libraries for SSL/TLS functionality. Microsoft Windows
Microsoft Windows
Microsoft Windows is a series of operating systems produced by Microsoft.Microsoft introduced an operating environment named Windows on November 20, 1985 as an add-on to MS-DOS in response to the growing interest in graphical user interfaces . Microsoft Windows came to dominate the world's personal...
includes an implementation of SSL and TLS as part of its Secure Channel
Security Support Provider Interface
Security Support Provider Interface is an API used by Microsoft Windows systems to perform a variety of security-related operations such as authentication....
package. Delphi programmers may use a library called Indy. Comparison of TLS Implementations
Comparison of TLS Implementations
The Transport Layer Security protocol provide the ability to secure communications across networks. There are several TLS implementations which are free and open source software and sometimes choosing between the available implementations can be tough...
provides a brief comparison of features of different implementations.
Browser implementations
All the most recent web browsers support TLS:- Apple's SafariSafari (web browser)Safari is a web browser developed by Apple Inc. and included with the Mac OS X and iOS operating systems. First released as a public beta on January 7, 2003 on the company's Mac OS X operating system, it became Apple's default browser beginning with Mac OS X v10.3 "Panther". Safari is also the...
supports TLS, but it’s not officially specified which version. On operating systems (Safari uses the TLS implementation of the underlying OS) like Mac OS X 10.5.8, Mac OS X 10.6.6, Windows XP, Windows Vista or Windows 7, Safari 5 has been reported to support TLS 1.0. - Mozilla FirefoxMozilla FirefoxMozilla Firefox is a free and open source web browser descended from the Mozilla Application Suite and managed by Mozilla Corporation. , Firefox is the second most widely used browser, with approximately 25% of worldwide usage share of web browsers...
, versions 2 and above, support TLS 1.0. , Firefox does not support TLS 1.1 or 1.2. - Microsoft Internet Explorer always uses the TLS implementation of the underlying Microsoft Windows Operating System, a service called SChannel Security Service Provider. Internet Explorer 8Internet Explorer 8Windows Internet Explorer 8 is a web browser developed by Microsoft in the Internet Explorer browser series. The browser was released on March 19, 2009 for Windows XP, Windows Server 2003, Windows Vista, Windows Server 2008, and Windows 7. Both 32-bit and 64-bit builds are available...
in Windows 7 and Windows Server 2008 R2Windows Server 2008 R2Windows Server 2008 R2 is a server operating system produced by Microsoft. It was released to manufacturing on July 22, 2009 and launched on October 22, 2009. According to the Windows Server Team blog, the retail availability was September 14, 2009. It is built on Windows NT 6.1, the same core...
supports TLS 1.2. Windows 7 and Windows Server 2008 R2 use the same code (Microsoft Windows Version 6.1 (build 7600)) similar to how Windows Vista SP1 uses the same code as Windows 2008 Server. - As of PrestoPresto (layout engine)Presto is the layout engine for later versions of the Opera web browser . After several public betas and technical previews, it was released on January 28, 2003 in Opera 7 for Windows, and as of Opera 11 it is still in use. Presto is dynamic: the page or parts of it can be re-rendered in response...
2.2, featured in OperaOpera (web browser)Opera is a web browser and Internet suite developed by Opera Software with over 200 million users worldwide. The browser handles common Internet-related tasks such as displaying web sites, sending and receiving e-mail messages, managing contacts, chatting on IRC, downloading files via BitTorrent,...
10, Opera supports TLS 1.2. - Google's ChromeGoogle ChromeGoogle Chrome is a web browser developed by Google that uses the WebKit layout engine. It was first released as a beta version for Microsoft Windows on September 2, 2008, and the public stable release was on December 11, 2008. The name is derived from the graphical user interface frame, or...
browser supports TLS 1.0, but not TLS 1.1 or 1.2.
Standards
The current approved version of TLS is version 1.2, which is specified in:- RFC 5246: “The Transport Layer Security (TLS) Protocol Version 1.2”.
The current standard replaces these former versions, which are now considered obsolete:
- RFC 2246: “The TLS Protocol Version 1.0”.
- RFC 4346: “The Transport Layer Security (TLS) Protocol Version 1.1”.
Other RFC
Request for Comments
In computer network engineering, a Request for Comments is a memorandum published by the Internet Engineering Task Force describing methods, behaviors, research, or innovations applicable to the working of the Internet and Internet-connected systems.Through the Internet Society, engineers and...
s subsequently extended TLS.
Extensions to TLS 1.0 include:
- RFC 2595: “Using TLS with IMAP, POP3 and ACAP”. Specifies an extension to the IMAP, POP3 and ACAP services that allow the server and client to use transport-layer security to provide private, authenticated communication over the Internet.
- RFC 2712: “Addition of Kerberos Cipher Suites to Transport Layer Security (TLS)”. The 40-bit cipher suites defined in this memo appear only for the purpose of documenting the fact that those cipher suite codes have already been assigned.
- RFC 2817: “Upgrading to TLS Within HTTP/1.1”, explains how to use the Upgrade mechanism in HTTP/1.1 to initiate Transport Layer Security (TLS) over an existing TCP connection. This allows unsecured and secured HTTP traffic to share the same well known port (in this case, http: at 80 rather than https: at 443).
- RFC 2818: “HTTP Over TLS”, distinguishes secured traffic from insecure traffic by the use of a different 'server port'.
- RFC 3207: “SMTP Service Extension for Secure SMTP over Transport Layer Security”. Specifies an extension to the SMTP service that allows an SMTP server and client to use transport-layer security to provide private, authenticated communication over the Internet.
- RFC 3268: “AES Ciphersuites for TLS”. Adds Advanced Encryption StandardAdvanced Encryption StandardAdvanced Encryption Standard is a specification for the encryption of electronic data. It has been adopted by the U.S. government and is now used worldwide. It supersedes DES...
(AES) cipher suites to the previously existing symmetric ciphers. - RFC 3546: “Transport Layer Security (TLS) Extensions”, adds a mechanism for negotiating protocol extensions during session initialisation and defines some extensions. Made obsolete by RFC 4366.
- RFC 3749: “Transport Layer Security Protocol Compression Methods”, specifies the framework for compression methods and the DEFLATEDEFLATEDeflate is a lossless data compression algorithm that uses a combination of the LZ77 algorithm and Huffman coding. It was originally defined by Phil Katz for version 2 of his PKZIP archiving tool and was later specified in RFC 1951....
compression method. - RFC 3943: “Transport Layer Security (TLS) Protocol Compression Using Lempel-Ziv-Stac (LZS)”.
- RFC 4132: “Addition of CamelliaCamellia (cipher)In cryptography, Camellia is a 128-bit block cipher jointly developed by Mitsubishi and NTT. The cipher has been approved for use by the ISO/IEC, the European Union's NESSIE project and the Japanese CRYPTREC project...
Cipher Suites to Transport Layer Security (TLS)”. - RFC 4162: “Addition of SEEDSEEDSEED is a block cipher developed by the Korean Information Security Agency. It is used broadly throughout South Korean industry, but seldom found elsewhere. It gained popularity in Korea because 40 bit SSL was not considered strong enough , so the Korean Information Security Agency developed its...
Cipher Suites to Transport Layer Security (TLS)”. - RFC 4217: “Securing FTP with TLSFTPSFTPS is an extension to the commonly used File Transfer Protocol that adds support for the Transport Layer Security and the Secure Sockets Layer cryptographic protocols....
”. - RFC 4279: “Pre-Shared Key Ciphersuites for Transport Layer Security (TLS)”, adds three sets of new cipher suites for the TLS protocol to support authentication based on pre-shared keys.
Extensions to TLS 1.1 include:
- RFC 4347: “Datagram Transport Layer SecurityDatagram Transport Layer SecurityIn information technology, the Datagram Transport Layer Security protocol provides communications privacy for datagram protocols. DTLS allows datagram-based applications to communicate in a way that is designed to prevent eavesdropping, tampering, or message forgery...
” specifies a TLS variant that works over datagram protocols (such as UDP). - RFC 4366: “Transport Layer Security (TLS) Extensions” describes both a set of specific extensions and a generic extension mechanism.
- RFC 4492: “Elliptic Curve CryptographyElliptic curve cryptographyElliptic curve cryptography is an approach to public-key cryptography based on the algebraic structure of elliptic curves over finite fields. The use of elliptic curves in cryptography was suggested independently by Neal Koblitz and Victor S...
(ECC) Cipher Suites for Transport Layer Security (TLS)”. - RFC 4507: “Transport Layer Security (TLS) Session Resumption without Server-Side State”.
- RFC 4680: “TLS Handshake Message for Supplemental Data”.
- RFC 4681: “TLS User Mapping Extension”.
- RFC 4785: “Pre-Shared Key (PSK) Ciphersuites with NULL Encryption for Transport Layer Security (TLS)”.
- RFC 5054: “Using the Secure Remote PasswordSecure remote password protocolThe Secure Remote Password protocol is a password-authenticated key agreement protocol.- Overview :The SRP protocol has a number of desirable properties: it allows a user to authenticate themselves to a server, it is resistant to dictionary attacks mounted by an eavesdropper, and it does not...
(SRP) Protocol for TLS Authentication”. Defines the TLS-SRPTLS-SRPTransport layer security Secure Remote Password ciphersuites are a set of cryptographic protocols that provide secure communication based on passwords, using an SRP password-authenticated key exchange....
ciphersuites. - RFC 5081: “Using OpenPGP Keys for Transport Layer Security (TLS) Authentication”, obsoleted by RFC 6091.
Extensions to TLS 1.2 include:
- RFC 5746: “Transport Layer Security (TLS) Renegotiation Indication Extension”.
- RFC 5878: “Transport Layer Security (TLS) Authorization Extensions”.
- RFC 6091: “Using OpenPGP Keys for Transport Layer Security (TLS) Authentication“.
- RFC 6176: “Prohibiting Secure Sockets Layer (SSL) Version 2.0”.
- RFC 6209: “Addition of the ARIAARIA (cipher)In cryptography, ARIA is a block cipher designed in 2003 by a large group of South Korean researchers. In 2004, the Korean Agency for Technology and Standards selected it as a standard cryptographic technique....
Cipher Suites to Transport Layer Security (TLS)”.
See also
- Virtual private networkVirtual private networkA virtual private network is a network that uses primarily public telecommunication infrastructure, such as the Internet, to provide remote offices or traveling users access to a central organizational network....
- Comparison of TLS ImplementationsComparison of TLS ImplementationsThe Transport Layer Security protocol provide the ability to secure communications across networks. There are several TLS implementations which are free and open source software and sometimes choosing between the available implementations can be tough...
- Datagram Transport Layer SecurityDatagram Transport Layer SecurityIn information technology, the Datagram Transport Layer Security protocol provides communications privacy for datagram protocols. DTLS allows datagram-based applications to communicate in a way that is designed to prevent eavesdropping, tampering, or message forgery...
- Multiplexed Transport Layer SecurityMultiplexed Transport Layer SecurityIn information technology, the Transport Layer Security protocol provides connection security with mutual authentication, data confidentiality and integrity, key generation and distribution, and security parameters negotiation...
- X.509X.509In cryptography, X.509 is an ITU-T standard for a public key infrastructure and Privilege Management Infrastructure . X.509 specifies, amongst other things, standard formats for public key certificates, certificate revocation lists, attribute certificates, and a certification path validation...
- Certificate authorityCertificate authorityIn cryptography, a certificate authority, or certification authority, is an entity that issues digital certificates. The digital certificate certifies the ownership of a public key by the named subject of the certificate...
- Public key certificatePublic key certificateIn cryptography, a public key certificate is an electronic document which uses a digital signature to bind a public key with an identity — information such as the name of a person or an organization, their address, and so forth...
- Extended Validation Certificate
- SEEDSEEDSEED is a block cipher developed by the Korean Information Security Agency. It is used broadly throughout South Korean industry, but seldom found elsewhere. It gained popularity in Korea because 40 bit SSL was not considered strong enough , so the Korean Information Security Agency developed its...
- SSL accelerationSSL accelerationSSL acceleration is a method of offloading the processor-intensive public key encryption algorithms involved in SSL transactions to a hardware accelerator....
- Obfuscated TCPObfuscated TCPObfuscated TCP was a proposal for a transport layer protocol which implements opportunistic encryption over TCP. It was designed to prevent mass wiretapping and malicious corruption of TCP traffic on the internet, with lower implementation cost and complexity than TLS...
- Server gated cryptographyServer gated cryptographyServer Gated Cryptography was created in response to United States federal legislation on the export of strong cryptography in the 1990s....
- tcpcryptTcpcryptIn computer networking, tcpcrypt is a transport layer communication encryption protocol. Unlike prior protocols like TLS , tcpcrypt is implemented as a TCP extension. It was designed by a team of six security and networking experts: Andrea Bittau, Mike Hamburg, Mark Handley, David Mazières, Dan...
- Server Name IndicationServer Name IndicationServer Name Indication is a feature that extends the SSL and TLS protocols. To properly secure the communication between a client and a server, the client requests a digital certificate from the server; once the server sends the certificate, the client examines it, uses it to encrypt the...
Software
- OpenSSLOpenSSLOpenSSL is an open source implementation of the SSL and TLS protocols. The core library implements the basic cryptographic functions and provides various utility functions...
: a free implementation (BSD license with some extensions), used by OpenVPNOpenVPNOpenVPN is a free and open source software application that implements virtual private network techniques for creating secure point-to-point or site-to-site connections in routed or bridged configurations and remote access facilities. It uses a custom security protocol that utilizes SSL/TLS for...
(GNU GPL) - GnuTLSGnuTLSGnuTLS , the GNU Transport Layer Security Library, is a free software implementation of the SSL and TLS protocols. Its purpose is to offer an application programming interface for applications to enable secure communication protocols over their network transport layer.-Features:GnuTLS consists of...
: a free implementation (LGPL licensed) - cryptlibCryptlibcryptlib is an open source cross-platform software security toolkit library. It is distributed under the Sleepycat License, a free software license compatible with the GNU General Public License...
: a portable open source cryptography library (includes TLS/SSL implementation) - JSSEJava Secure Socket ExtensionThe Java Secure Socket Extension is a set of packages that enable secure Internet communications. It implements a Java technology version of Secure Sockets Layer and Transport Layer Security protocols...
: a JavaJava (programming language)Java is a programming language originally developed by James Gosling at Sun Microsystems and released in 1995 as a core component of Sun Microsystems' Java platform. The language derives much of its syntax from C and C++ but has a simpler object model and fewer low-level facilities...
implementation included in the Java Runtime Environment - Network Security ServicesNetwork Security ServicesIn computing, Network Security Services comprises a set of libraries designed to support cross-platform development of security-enabled client and server applications. NSS provides a complete open-source implementation of crypto libraries supporting SSL and S/MIME...
(NSS): FIPS 140FIPS 140The 140 series of Federal Information Processing Standards are U.S. government computer security standards that specify requirements for cryptography modules...
validated open source library - PolarSSLPolarSSLPolarSSL is a dual licensed implementation of the SSL and TLS protocols. PolarSSL is almost entirely based on XySSL, which was written and copyrighted by French "white hat hacker" Christophe Devine. XySSL was first released on November 1, 2006 under GPL and BSD licenses...
: A tiny SSL/TLS implementation for embedded devices that is designed for ease of use. - CyaSSLCyaSSLCyaSSL is a small, portable, embedded SSL programming library targeted for use by embedded systems developers. It is an open source, implementation of SSL built in the C language. It includes SSL client libraries and an SSL server implementation as well as support for multiple API's, including...
: Embedded SSL/TLS Library with a strong focus on speed and size.
Further reading
- Creating VPNs with IPsec and SSL/TLS Linux Journal article by Rami Rosen
External links
- SSL 2 specification (published 1994)
- SSL 3.0 specification (published 1996)
- Netscape's final SSL 3.0 draft (1996)
- The IETF (Internet Engineering Task Force) TLS Workgroup
- SSL tutorial
- OpenSSL thread safe connections tutorial with example source code
- ECMAScript Secure Transform (Web 2 Secure Transform Method)
- OWASP: Transport Layer Protection Cheat Sheet
- A talk on SSL/TLS that tries to explain things in terms that people might understand.
- SSL: Foundation for Web Security

