
Email
Encyclopedia
Electronic mail, commonly known as email or e-mail, is a method of exchanging digital
messages from an author to one or more recipients. Modern email operates across the Internet
or other computer network
s. Some early email systems required that the author and the recipient both be online at the same time, in common with instant messaging
. Today's email systems are based on a store-and-forward model. Email servers accept, forward, deliver and store messages. Neither the users nor their computers are required to be online simultaneously; they need connect only briefly, typically to an email server, for as long as it takes to send or receive messages.
An email message consists of three components, the message envelope, the message header, and the message body. The message header contains control information, including, minimally, an originator's email address and one or more recipient addresses. Usually descriptive information is also added, such as a subject header field and a message submission date/time stamp.
Originally a text-only (7-bit ASCII and others) communications medium, email was extended to carry multi-media content attachments, a process standardized in RFC
2045 through 2049. Collectively, these RFCs have come to be called Multipurpose Internet Mail Extensions (MIME).
Electronic mail predates the inception of the Internet
, and was in fact a crucial tool in creating it, but the history of modern, global Internet email services reaches back to the early ARPANET
. Standards for encoding email messages were proposed as early as 1973 (RFC 561). Conversion from ARPANET to the Internet in the early 1980s produced the core of the current services. An email sent in the early 1970s looks quite similar to a basic text message sent on the Internet today.
Network-based email was initially exchanged on the ARPANET in extensions to the File Transfer Protocol
(FTP), but is now carried by the Simple Mail Transfer Protocol
(SMTP), first published as Internet standard
10 (RFC 821) in 1982. In the process of transporting email messages between systems, SMTP communicates delivery parameters using a message envelope separate from the message (header and body) itself.
options that occasionally prove cause for surprisingly vehement disagreement.
There is also some variety in the plural form of the term. In US English email is used as a mass noun
(like the term mail for items sent through the postal system), but in British English it is more commonly used as a count noun
with the plural emails.
Early email was just a small advance on what we know these days as a file directory - it just put a message in another user's directory in a spot where they could see it when they logged in. Simple as that. Just like leaving a note on someone's desk.
Probably the first email system of this type was MAILBOX, used at Massachusetts Institute of Technology from 1965. Another early program to send messages on the same computer was called SNDMSG.
Some of the mainframe computers of this era might have had up to one hundred users -often they used what are called "dumb terminals" to access the mainframe from their work desks. Dumb terminals just connected to the mainframe - they had no storage or memory of their own, they did all their work on the remote mainframe computer.
Before internetworking began, therefore, email could only be used to send messages to various users of the same computer. Once computers began to talk to each other over networks, however, the problem became a little more complex - We needed to be able to put a message in an envelope and address it. To do this, we needed a means to indicate to whom letters should go that the electronic posties understood - just like the postal system, we needed a way to indicate an address.
This is why Ray Tomlinson is credited with inventing email in 1972. Like many of the Internet inventors, Tomlinson worked for Bolt Beranek and Newman as an ARPANET contractor. He picked the @ symbol from the computer keyboard to denote sending messages from one computer to another. So then, for anyone using Internet standards, it was simply a matter of nominating name-of-the-user@name-of-the-computer. Internet pioneer Jon Postel, who we will hear more of later, was one of the first users of the new system, and is credited with describing it as a "nice hack". It certainly was, and it has lasted to this day.
Despite what the world wide web offers, email remains the most important application of the Internet and the most widely used facility it has. Now more than 600 million people internationally use email.
By 1974 there were hundreds of military users of email because ARPANET eventually encouraged it. Email became the saviour of Arpanet, and caused a radical shift in Arpa's purpose.
Things developed rapidly from there. Larry Roberts invented some email folders for his boss so he could sort his mail, a big advance. In 1975 John Vital developed some software to organize email. By 1976 email had really taken off, and commercial packages began to appear. Within a couple of years, 75% of all ARPANET traffic was email.
Email took us from Arpanet to the Internet. Here was something that ordinary people all over the world wanted to use.
As Ray Tomlinson observed some years later about email, "any single development is stepping on the heels of the previous one and is so closely followed by the next that most advances are obscured. I think that few individuals will be remembered." That's true - to catalogue all the developments would be a huge task.
One of the first new developments when personal computers came on the scene was "offline readers". Offline readers allowed email users to store their email on their own personal computers, and then read it and prepare replies without actually being connected to the network - sort of like Microsoft Outlook can do today.
This was particularly useful in parts of the world where telephone costs to the nearest email system were expensive. (often this involved international calls in the early days) With connection charges of many dollars a minute, it mattered to be able to prepare a reply without being connected to a telephone, and then get on the network to send it. It was also useful because the "offline" mode allowed for more friendly interfaces. Being connected direct to the host email system in this era of very few standards often resulted in delete keys and backspace keys not working, no capacity for text to "wrap around" on the screen of the users computer, and other such annoyances. Offline readers helped a lot.
The first important email standard was called SMTP, or simple message transfer protocol. SMTP was very simple and is still in use - however, as we will hear later in this series, SMTP was a fairly naïve protocol, and made no attempt to find out whether the person claiming to send a message was the person they purported to be. Forgery was (and still is) very easy in email addresses. These basic flaws in the protocol were later to be exploited by viruses and worms, and by security frauds and spammers forging identities. Some of these problems are still being addressed in 2004.
But as it developed email started to take on some pretty neat features. One of the first good commercial systems was Eudora, developed by Steve Dorner in 1988. Not long after Pegasus mail appeared.
When Internet standards for email began to mature the POP (or Post Office Protocol) servers began to appear as a standard - before that each server was a little different. POP was an important standard to allow users to develop mail systems that would work with each other.
These were the days of per-minute charges for email for individual dialup users. For most people on the Internet in those days email and email discussion groups were the main uses. These were many hundreds of these on a wide variety of topics, and as a body of newsgroups they became known as USENET.
With the World Wide Web, email started to be made available with friendly web interfaces by providers such as Yahoo and Hotmail. Usually this was without charge. Now that email was affordable, everyone wanted at least one email address, and the medium was adopted by not just millions, but hundreds of millions of people.
telegraph of the mid 1800s; and the 1939 New York World's Fair
, where IBM
sent a letter of congratulations from San Francisco to New York on an IBM radio-type, calling it a high-speed substitute for mail service in the world of tomorrow. Teleprinter
s were used in Germany during World War II, and use spread until the late 1960s when there was a worldwide Telex network
. Additionally, there was the similar but incompatible American TWX, which remained important until the late 1980s.
's Compatible Time-Sharing System (CTSS) in 1961 for the first time multiple users were able to log into a central system from remote dial-up terminals, and to store, and share, files on the central disk.
Informal methods of using this to pass messages developed—and were expanded to create the first true email system:
Other early time-sharing system soon had their own email applications:
Although similar in concept, all these original email systems had widely different features and ran on incompatible systems. They allowed communication only between users logged into the same host or "mainframe" - although this could be hundreds or even thousands of users within an organization.
Other separate networks were also being created including:
s on LAN
s became increasingly important. Server-based systems similar to the earlier mainframe systems were developed. Again these systems initially allowed communication only between users logged into the same server infrastructure. Examples include:
Eventually these systems too could also be linked between different organizations, as long as they ran the same email system and proprietary protocol.
Later efforts at interoperability standardization included:
so that it could copy messages (as files) over the network. Lawrence Roberts
, the project manager for the ARPANET development, took the idea of READMAIL, which dumped all "recent" messages onto the user's terminal, and wrote a program for TENEX in TECO
macros called RD which permitted accessing individual messages. Barry Wessler then updated RD and called it NRD.
Marty Yonke combined rewrote NRD to include reading, access to SNDMSG for sending, and a help system, and called the utility WRD which was later known as BANANARD. John Vittal then updated this version to include 3 important commands: Move (combined save/delete command), Answer (determined to whom a reply should be sent) and Forward (send an email to a person who was not already a recipient). The system was called MSG. With inclusion of these features, MSG is considered to be the first integrated modern email program, from which many other applications have descended.
made a large contribution to the development of email. There is one report that indicates experimental inter-system email transfers began shortly after its creation in 1969. Ray Tomlinson
is generally credited as having sent the first email across a network, initiating the use of the "@
" sign to separate the names of the user and the user's machine in 1971, when he sent a message from one Digital Equipment Corporation
DEC-10 computer to another DEC-10. The two machines were placed next to each other. Tomlinson's work was quickly adopted across the ARPANET, which significantly increased the popularity of email. For many years, email was the killer app
of the ARPANET and then the Internet.
Most other networks had their own email protocols and address formats; as the influence of the ARPANET and later the Internet grew, central sites often hosted email gateways
that passed mail between the Internet and these other networks. Internet email addressing is still complicated by the need to handle mail destined for these older networks. Some well-known examples of these were UUCP
(mostly Unix computers), BITNET
(mostly IBM and VAX mainframes at universities), FidoNet
(personal computers), DECNET (various networks) and CSNET
a forerunner of NSFNet
.
An example of an Internet email address that routed mail to a user at a UUCP host:
This was necessary because in early years UUCP computers did not maintain (and could not consult central servers for) information about the location of all hosts they exchanged mail with, but rather only knew how to communicate with a few network neighbors; email messages (and other data such as Usenet News
) were passed along in a chain among hosts who had explicitly agreed to share data with each other. (Eventually the UUCP Mapping Project would provide a form of network routing database for email.)
(MUA). She enters the email address of her correspondent, and hits the "send" button.
This server may need to forward the message to other MTAs before the message reaches the final message delivery agent (MDA).
That sequence of events applies to the majority of email users. However, there are many alternative possibilities and complications to the email system:
Many MTAs used to accept messages for any recipient on the Internet and do their best to deliver them. Such MTAs are called open mail relay
s. This was very important in the early days of the Internet when network connections were unreliable. If an MTA couldn't reach the destination, it could at least deliver it to a relay closer to the destination. The relay stood a better chance of delivering the message at a later time. However, this mechanism proved to be exploitable by people sending unsolicited bulk email and as a consequence very few modern MTAs are open mail relays, and many MTAs don't accept messages from open mail relays because such messages are very likely to be spam.
Internet email messages consist of two major sections:
The header is separated from the body by a blank line.
. Each field has a name and a value. RFC 5322 specifies the precise syntax.
Informally, each line of text in the header that begins with a printable character begins a separate field. The field name starts in the first character of the line and ends before the separator character ":". The separator is then followed by the field value (the "body" of the field). The value is continued onto subsequent lines if those lines have a space or tab as their first character. Field names and values are restricted to 7-bit ASCII
characters. Non-ASCII values may be represented using MIME encoded words.
The message header should include at least the following fields:
RFC 3864 describes registration procedures for message header fields at the IANA
; it provides for permanent and provisional message header field names, including also fields defined for MIME, netnews, and http, and referencing relevant RFCs. Common header fields for email include:
Note that the To: field is not necessarily related to the addresses to which the message is delivered. The actual delivery list is supplied separately to the transport protocol, SMTP, which may or may not originally have been extracted from the header content. The "To:" field is similar to the addressing at the top of a conventional letter which is delivered according to the address on the outer envelope. Also note that the "From:" field does not have to be the real sender of the email message. One reason is that it is very easy to fake the "From:" field and let a message seem to be from any mail address. It is possible to digitally sign
email, which is much harder to fake, but such signatures require extra programming and often external programs to verify. Some ISPs do not relay email claiming to come from a domain not hosted by them, but very few (if any) check to make sure that the person or even email address named in the "From:" field is the one associated with the connection. Some ISPs apply email authentication systems to email being sent through their MTA to allow other MTAs to detect forged spam that might appear to come from them.
Recently the IETF EAI working group has defined some experimental extensions to allow Unicode
characters to be used within the header. In particular, this allows email addresses to use non-ASCII characters. Such characters must only be used by servers that support these extensions.
. Much email software is 8-bit clean
but must assume it will communicate with 7-bit servers and mail readers. The MIME
standard introduced character set specifiers and two content transfer encodings to enable transmission of non-ASCII data: quoted printable for mostly 7 bit content with a few characters outside that range and base64
for arbitrary binary data. The 8BITMIME and BINARY
extensions were introduced to allow transmission of mail without the need for these encodings, but many mail transport agents still do not support them fully. In some countries, several encoding schemes coexist; as the result, by default, the message in a non-Latin alphabet language appears in non-readable form (the only exception is coincidence, when the sender and receiver use the same encoding scheme). Therefore, for international character sets, Unicode
is growing in popularity.
or HTML for the message body at the option of the user. HTML email messages often include an automatically generated plain text copy as well, for compatibility reasons.
Advantages of HTML include the ability to include in-line links and images, set apart previous messages in block quote
s, wrap naturally on any display, use emphasis such as underline
s and italics, and change font
styles. Disadvantages include the increased size of the email, privacy concerns about web bug
s, abuse of HTML email as a vector for phishing
attacks and the spread of malicious software
.
Some web based Mailing list
s recommend that all posts be made in plain-text, with 72 or 80 characters per line
for all the above reasons, but also because they have a significant number of readers using text-based
email clients such as Mutt.
Some Microsoft
email clients allow rich formatting using RTF
, but unless the recipient is guaranteed to have a compatible email client this should be avoided.
In order to ensure that HTML sent in an email is rendered properly by the recipient's client software, an additional header must be specified when sending: "Content-type: text/html". Most email programs send this header automatically.
s (MTAs); and delivered to a mail store by programs called mail delivery agent
s (MDAs, also sometimes called local delivery agents, LDAs). Users can retrieve their messages from servers using standard protocols such as POP
or IMAP, or, as is more likely in a large corporate
environment, with a proprietary
protocol specific to Novell Groupwise
, Lotus Notes
or Microsoft Exchange Server
s. Webmail interfaces allow users to access their mail with any standard web browser
, from any computer, rather than relying on an email client. Programs used by users for retrieving, reading, and managing email are called mail user agents (MUAs).
Mail can be stored on the client
, on the server
side, or in both places. Standard formats for mailboxes include Maildir
and mbox
. Several prominent email clients use their own proprietary format and require conversion software to transfer email between them. Server-side storage is often in a proprietary format but since access is through a standard protocol such as IMAP, moving email from one server to another can be done with any MUA supporting the protocol.
Accepting a message obliges an MTA to deliver it, and when a message cannot be delivered, that MTA must send a bounce message
back to the sender, indicating the problem.
format. The specific format used is often indicated by special filename extension
s:
eml
emlx
msg
mbx
Some applications (like Apple Mail
) leave attachments encoded in messages for searching while also saving separate copies of the attachments. Others separate attachments from messages and save them in a specific directory.
, as registered with the IANA
, defines the mailto: scheme for SMTP email addresses. Though its use is not strictly defined, URLs of this form are intended to be used to open the new message window of the user's mail client when the URL is activated, with the address as defined by the URL in the To: field.
s, fax
services, or any number of the computer mediated communications such as email.
law professor Lawrence Lessig
is credited with coining this term, but he may only have popularized it.
LAN based email is also an emerging form of usage for business. It not only allows the business user to download mail when offline, it also allows the small business user to have multiple users' email IDs with just one email connection.
Despite these disadvantages, email has become the most widely used medium of communication within the business world. In fact, a 2010 study on workplace communication, found that 83% of U.S. knowledge workers felt that email was critical to their success and productivity at work.
Furthermore, due to technical reasons, often a small attachment can increase in size when sent, which can be confusing to senders when trying to assess whether they can or cannot send a file by email, and this can result in their message being rejected.
As larger and larger file sizes are being created and traded, many users are either forced to upload and download their files using an FTP server, or more popularly, use online file sharing facilities or services, usually over web-friendly HTTP, in order to send and receive them.
In October 2010, CNN published an article titled "Happy Information Overload Day" that compiled research on email overload from IT companies and productivity experts. According to Basex, the average knowledge worker receives 93 emails a day. Subsequent studies have reported higher numbers. Marsha Egan, an email productivity expert, called email technology both a blessing and a curse in the article. She stated, "Everyone just learns that they have to have it dinging and flashing and open just in case the boss e-mails," she said. "The best gift any group can give each other is to never use e-mail urgently. If you need it within three hours, pick up the phone."
, phishing
, and email worms
.
Spamming is unsolicited commercial (or bulk) email. Because of the minuscule cost of sending email, spammers can send hundreds of millions of email messages each day over an inexpensive Internet connection. Hundreds of active spammers sending this volume of mail results in information overload
for many computer users who receive voluminous unsolicited email each day.
Email worms use email as a way of replicating themselves into vulnerable computers. Although the first email worm
affected UNIX
computers, the problem is most common today on the more popular Microsoft Windows
operating system.
The combination of spam and worm programs results in users receiving a constant drizzle of junk email, which reduces the usefulness of email as a practical tool.
A number of anti-spam techniques mitigate the impact of spam. In the United States
, U.S. Congress has also passed a law, the Can Spam Act of 2003, attempting to regulate such email. Australia
also has very strict spam laws restricting the sending of spam from an Australian ISP, but its impact has been minimal since most spam comes from regimes that seem reluctant to regulate the sending of spam.
personnel and others whose function may involve monitoring or managing may be accessing the email of other employees.
Email privacy, without some security precautions, can be compromised because:
There are cryptography
applications that can serve as a remedy to one or more of the above. For example, Virtual Private Network
s or the Tor anonymity network
can be used to encrypt traffic from the user machine to a safer network while GPG
, PGP
, SMEmail, or S/MIME
can be used for end-to-end
message encryption, and SMTP STARTTLS or SMTP over Transport Layer Security
/Secure Sockets Layer can be used to encrypt communications for a single mail hop between the SMTP client and the SMTP server.
Additionally, many mail user agents do not protect logins and passwords, making them easy to intercept by an attacker. Encrypted authentication schemes such as SASL
prevent this.
Finally, attached files share many of the same hazards as those found in peer-to-peer filesharing
. Attached files may contain trojans
or viruses
.
introduced Delivery Status Notifications (delivery receipts) and Message Disposition Notifications (return receipts); however, these are not universally deployed in production. (A complete Message Tracking mechanism was also defined, but it never gained traction; see RFCs 3885 through 3888.)
Many ISPs now deliberately disable non-delivery reports (NDRs) and delivery receipts due to the activities of spammers:
There are a number of systems that allow the sender to see if messages have been opened. The receiver could also let the sender know that the emails have been opened through an "Okay" button. A check sign can appear in the sender's screen when the receiver's "Okay" button is pressed.
Starting in 1977, the US Postal Service (USPS) recognized that electronic mail and electronic transactions posed a significant threat to First Class mail volumes and revenue. Therefore, the USPS initiated an experimental email service known as E-COM. Electronic messages were transmitted to a post office, printed out, and delivered as hard copy. To take advantage of the service, an individual had to transmit at least 200 messages. The delivery time of the messages was the same as First Class mail and cost 26 cents. Both the Postal Regulatory Commission and the Federal Communications Commission
opposed E-COM. The FCC concluded that E-COM constituted common carriage under its jurisdiction and the USPS would have to file a tariff
. Three years after initiating the service, USPS canceled E-COM and attempted to sell it off.
The early ARPANET dealt with multiple email clients that had various, and at times incompatible, formats. For example, in the Multics
, the "@" sign meant "kill line" and anything before the "@" sign was ignored, so Multics users had to use a command-line option to specify the destination system. The Department of Defense
DARPA desired to have uniformity and interoperability for email and therefore funded efforts to drive towards unified inter-operable standards. This led to David Crocker, John Vittal, Kenneth Pogran, and Austin Henderson publishing RFC 733, "Standard for the Format of ARPA Network Text Message" (November 21, 1977), which was apparently not effective. In 1979, a meeting was held at BBN to resolve incompatibility issues. Jon Postel
recounted the meeting in RFC 808, "Summary of Computer Mail Services Meeting Held at BBN on 10 January 1979" (March 1, 1982), which includes an appendix listing the varying email systems at the time. This, in turn, lead to the release of David Crocker's RFC 822, "Standard for the Format of ARPA Internet Text Messages" (August 13, 1982).
The National Science Foundation
took over operations of the ARPANET and Internet from the Department of Defense, and initiated NSFNet
, a new backbone
for the network. A part of the NSFNet AUP forbade commercial traffic. In 1988, Vint Cerf
arranged for an interconnection of MCI Mail
with NSFNET on an experimental basis. The following year Compuserve email interconnected with NSFNET. Within a few years the commercial traffic restriction was removed from NSFNETs AUP, and NSFNET was privatised.
In the late 1990s, the Federal Trade Commission
grew concerned with fraud transpiring in email, and initiated a series of procedures on spam, fraud, and phishing. In 2004, FTC jurisdiction over spam was codified into law in the form of the CAN SPAM Act. Several other US Federal Agencies have also exercised jurisdiction including the Department of Justice
and the Secret Service
.
NASA has provided email capabilities to astronauts aboard the Space Shuttle and Internationals Space Station since 1991 when a Macintosh Portable
was used aboard Space Shuttle
mission STS-43
to send the first email via AppleLink
. Today astronauts aboard the International Space Station have email capabilities through the via wireless networking
throughout the station and are connected to the ground at 3 Mbit/s Earth to station and 10 Mbit/s station to Earth, comparable to home DSL connection speeds.
Digital
A digital system is a data technology that uses discrete values. By contrast, non-digital systems use a continuous range of values to represent information...
messages from an author to one or more recipients. Modern email operates across the Internet
Internet
The Internet is a global system of interconnected computer networks that use the standard Internet protocol suite to serve billions of users worldwide...
or other computer network
Computer network
A computer network, often simply referred to as a network, is a collection of hardware components and computers interconnected by communication channels that allow sharing of resources and information....
s. Some early email systems required that the author and the recipient both be online at the same time, in common with instant messaging
Instant messaging
Instant Messaging is a form of real-time direct text-based chatting communication in push mode between two or more people using personal computers or other devices, along with shared clients. The user's text is conveyed over a network, such as the Internet...
. Today's email systems are based on a store-and-forward model. Email servers accept, forward, deliver and store messages. Neither the users nor their computers are required to be online simultaneously; they need connect only briefly, typically to an email server, for as long as it takes to send or receive messages.
An email message consists of three components, the message envelope, the message header, and the message body. The message header contains control information, including, minimally, an originator's email address and one or more recipient addresses. Usually descriptive information is also added, such as a subject header field and a message submission date/time stamp.
Originally a text-only (7-bit ASCII and others) communications medium, email was extended to carry multi-media content attachments, a process standardized in RFC
Request for Comments
In computer network engineering, a Request for Comments is a memorandum published by the Internet Engineering Task Force describing methods, behaviors, research, or innovations applicable to the working of the Internet and Internet-connected systems.Through the Internet Society, engineers and...
2045 through 2049. Collectively, these RFCs have come to be called Multipurpose Internet Mail Extensions (MIME).
Electronic mail predates the inception of the Internet
Internet
The Internet is a global system of interconnected computer networks that use the standard Internet protocol suite to serve billions of users worldwide...
, and was in fact a crucial tool in creating it, but the history of modern, global Internet email services reaches back to the early ARPANET
ARPANET
The Advanced Research Projects Agency Network , was the world's first operational packet switching network and the core network of a set that came to compose the global Internet...
. Standards for encoding email messages were proposed as early as 1973 (RFC 561). Conversion from ARPANET to the Internet in the early 1980s produced the core of the current services. An email sent in the early 1970s looks quite similar to a basic text message sent on the Internet today.
Network-based email was initially exchanged on the ARPANET in extensions to the File Transfer Protocol
File Transfer Protocol
File Transfer Protocol is a standard network protocol used to transfer files from one host to another host over a TCP-based network, such as the Internet. FTP is built on a client-server architecture and utilizes separate control and data connections between the client and server...
(FTP), but is now carried by the Simple Mail Transfer Protocol
Simple Mail Transfer Protocol
Simple Mail Transfer Protocol is an Internet standard for electronic mail transmission across Internet Protocol networks. SMTP was first defined by RFC 821 , and last updated by RFC 5321 which includes the extended SMTP additions, and is the protocol in widespread use today...
(SMTP), first published as Internet standard
Internet standard
In computer network engineering, an Internet Standard is a normative specification of a technology or methodology applicable to the Internet. Internet Standards are created and published by the Internet Engineering Task Force .-Overview:...
10 (RFC 821) in 1982. In the process of transporting email messages between systems, SMTP communicates delivery parameters using a message envelope separate from the message (header and body) itself.
Spelling
Electronic mail has several English spellingSpelling
Spelling is the writing of one or more words with letters and diacritics. In addition, the term often, but not always, means an accepted standard spelling or the process of naming the letters...
options that occasionally prove cause for surprisingly vehement disagreement.
- email is the form required by IETF Requests for Comment and working groups and increasingly by style guideStyle guideA style guide or style manual is a set of standards for the writing and design of documents, either for general use or for a specific publication, organization or field...
s. This spelling also appears in most dictionaries. - e-mail is a form previously recommended by some prominent journalistic and technical style guides. According to Corpus of Contemporary American EnglishCorpus of Contemporary American EnglishThe freely-searchable 425 million word Corpus of Contemporary American English is the largest corpus of American English currently available, and the only publicly-available corpus of American English to contain a wide array of texts from a number of genres.It was created by Mark Davies, Professor...
data, this form appears most frequently in edited, published American English writing. - mail was the form used in the original RFC butt. The service is referred to as mail and a single piece of electronic mail is called a message.
- eMail, capitalizing only the letter M, was common among ARPANETARPANETThe Advanced Research Projects Agency Network , was the world's first operational packet switching network and the core network of a set that came to compose the global Internet...
users and the early developers of UnixUnixUnix is a multitasking, multi-user computer operating system originally developed in 1969 by a group of AT&T employees at Bell Labs, including Ken Thompson, Dennis Ritchie, Brian Kernighan, Douglas McIlroy, and Joe Ossanna...
, CMSConversational Monitor SystemThe Conversational Monitor System is a relatively simple interactive computing single-user operating system.* CMS is part of IBM's VM family, which runs on IBM mainframe computers...
, AppleLinkAppleLinkAppleLink was the name of both Apple Computer's online service for its dealers, third party developers, and users, and the client software used to access it. Prior to the commercialization of the Internet, AppleLink was a popular service for Mac and Apple IIGS users...
, eWorldEWorldeWorld was an online service operated by Apple Inc. between June 1994 and March 1996. The services included email , news, and a bulletin board system...
, AOLAOLAOL Inc. is an American global Internet services and media company. AOL is headquartered at 770 Broadway in New York. Founded in 1983 as Control Video Corporation, it has franchised its services to companies in several nations around the world or set up international versions of its services...
, GEnieGEnieGEnie was an online service created by a General Electric business - GEIS that ran from 1985 through the end of 1999. In 1994, GEnie claimed around 350,000 users. Peak simultaneous usage was around 10,000 users...
, and HotmailHotmailWindows Live Hotmail, formerly known as MSN Hotmail and commonly referred to simply as Hotmail, is a free web-based email service operated by Microsoft as part of its Windows Live group. It was founded by Sabeer Bhatia and Jack Smith and launched in July 1996 as "HoTMaiL". It was one of the first...
. - EMail is a traditional form that has been used in RFCs for the "Author's Address", and is expressly required "for historical reasons".
- E-mail is sometimes used, capitalizing the initial letter E as in similar abbreviations like A-bomb, H-bomb, and C-section.
There is also some variety in the plural form of the term. In US English email is used as a mass noun
Mass noun
In linguistics, a mass noun is a noun that refers to some entity as an undifferentiated unit rather than as something with discrete subsets. Non-count nouns are best identified by their syntactic properties, and especially in contrast with count nouns. The semantics of mass nouns are highly...
(like the term mail for items sent through the postal system), but in British English it is more commonly used as a count noun
Count noun
In linguistics, a count noun is a common noun that can be modified by a numeral and that occurs in both singular and plural form, as well as co-occurring with quantificational determiners like every, each, several, etc. A mass noun has none of these properties...
with the plural emails.
Origin
Email is much older than ARPANet or the Internet. It was never invented; it evolved from very simple beginnings.Early email was just a small advance on what we know these days as a file directory - it just put a message in another user's directory in a spot where they could see it when they logged in. Simple as that. Just like leaving a note on someone's desk.
Probably the first email system of this type was MAILBOX, used at Massachusetts Institute of Technology from 1965. Another early program to send messages on the same computer was called SNDMSG.
Some of the mainframe computers of this era might have had up to one hundred users -often they used what are called "dumb terminals" to access the mainframe from their work desks. Dumb terminals just connected to the mainframe - they had no storage or memory of their own, they did all their work on the remote mainframe computer.
Before internetworking began, therefore, email could only be used to send messages to various users of the same computer. Once computers began to talk to each other over networks, however, the problem became a little more complex - We needed to be able to put a message in an envelope and address it. To do this, we needed a means to indicate to whom letters should go that the electronic posties understood - just like the postal system, we needed a way to indicate an address.
This is why Ray Tomlinson is credited with inventing email in 1972. Like many of the Internet inventors, Tomlinson worked for Bolt Beranek and Newman as an ARPANET contractor. He picked the @ symbol from the computer keyboard to denote sending messages from one computer to another. So then, for anyone using Internet standards, it was simply a matter of nominating name-of-the-user@name-of-the-computer. Internet pioneer Jon Postel, who we will hear more of later, was one of the first users of the new system, and is credited with describing it as a "nice hack". It certainly was, and it has lasted to this day.
Despite what the world wide web offers, email remains the most important application of the Internet and the most widely used facility it has. Now more than 600 million people internationally use email.
By 1974 there were hundreds of military users of email because ARPANET eventually encouraged it. Email became the saviour of Arpanet, and caused a radical shift in Arpa's purpose.
Things developed rapidly from there. Larry Roberts invented some email folders for his boss so he could sort his mail, a big advance. In 1975 John Vital developed some software to organize email. By 1976 email had really taken off, and commercial packages began to appear. Within a couple of years, 75% of all ARPANET traffic was email.
Email took us from Arpanet to the Internet. Here was something that ordinary people all over the world wanted to use.
As Ray Tomlinson observed some years later about email, "any single development is stepping on the heels of the previous one and is so closely followed by the next that most advances are obscured. I think that few individuals will be remembered." That's true - to catalogue all the developments would be a huge task.
One of the first new developments when personal computers came on the scene was "offline readers". Offline readers allowed email users to store their email on their own personal computers, and then read it and prepare replies without actually being connected to the network - sort of like Microsoft Outlook can do today.
This was particularly useful in parts of the world where telephone costs to the nearest email system were expensive. (often this involved international calls in the early days) With connection charges of many dollars a minute, it mattered to be able to prepare a reply without being connected to a telephone, and then get on the network to send it. It was also useful because the "offline" mode allowed for more friendly interfaces. Being connected direct to the host email system in this era of very few standards often resulted in delete keys and backspace keys not working, no capacity for text to "wrap around" on the screen of the users computer, and other such annoyances. Offline readers helped a lot.
The first important email standard was called SMTP, or simple message transfer protocol. SMTP was very simple and is still in use - however, as we will hear later in this series, SMTP was a fairly naïve protocol, and made no attempt to find out whether the person claiming to send a message was the person they purported to be. Forgery was (and still is) very easy in email addresses. These basic flaws in the protocol were later to be exploited by viruses and worms, and by security frauds and spammers forging identities. Some of these problems are still being addressed in 2004.
But as it developed email started to take on some pretty neat features. One of the first good commercial systems was Eudora, developed by Steve Dorner in 1988. Not long after Pegasus mail appeared.
When Internet standards for email began to mature the POP (or Post Office Protocol) servers began to appear as a standard - before that each server was a little different. POP was an important standard to allow users to develop mail systems that would work with each other.
These were the days of per-minute charges for email for individual dialup users. For most people on the Internet in those days email and email discussion groups were the main uses. These were many hundreds of these on a wide variety of topics, and as a body of newsgroups they became known as USENET.
With the World Wide Web, email started to be made available with friendly web interfaces by providers such as Yahoo and Hotmail. Usually this was without charge. Now that email was affordable, everyone wanted at least one email address, and the medium was adopted by not just millions, but hundreds of millions of people.
Precursors
Sending text messages electronically could be said to date back to the Morse codeMorse code
Morse code is a method of transmitting textual information as a series of on-off tones, lights, or clicks that can be directly understood by a skilled listener or observer without special equipment...
telegraph of the mid 1800s; and the 1939 New York World's Fair
1939 New York World's Fair
The 1939–40 New York World's Fair, which covered the of Flushing Meadows-Corona Park , was the second largest American world's fair of all time, exceeded only by St. Louis's Louisiana Purchase Exposition of 1904. Many countries around the world participated in it, and over 44 million people...
, where IBM
IBM
International Business Machines Corporation or IBM is an American multinational technology and consulting corporation headquartered in Armonk, New York, United States. IBM manufactures and sells computer hardware and software, and it offers infrastructure, hosting and consulting services in areas...
sent a letter of congratulations from San Francisco to New York on an IBM radio-type, calling it a high-speed substitute for mail service in the world of tomorrow. Teleprinter
Teleprinter
A teleprinter is a electromechanical typewriter that can be used to communicate typed messages from point to point and point to multipoint over a variety of communication channels that range from a simple electrical connection, such as a pair of wires, to the use of radio and microwave as the...
s were used in Germany during World War II, and use spread until the late 1960s when there was a worldwide Telex network
Telex
Telex may refer to:* Telex , , a communications network** Teleprinter, the device used on the above network* Telex , a Belgian pop group...
. Additionally, there was the similar but incompatible American TWX, which remained important until the late 1980s.
Host-based mail systems
With the introduction of GT the world turned rubish MITMassachusetts Institute of Technology
The Massachusetts Institute of Technology is a private research university located in Cambridge, Massachusetts. MIT has five schools and one college, containing a total of 32 academic departments, with a strong emphasis on scientific and technological education and research.Founded in 1861 in...
's Compatible Time-Sharing System (CTSS) in 1961 for the first time multiple users were able to log into a central system from remote dial-up terminals, and to store, and share, files on the central disk.
Informal methods of using this to pass messages developed—and were expanded to create the first true email system:
- MITMassachusetts Institute of TechnologyThe Massachusetts Institute of Technology is a private research university located in Cambridge, Massachusetts. MIT has five schools and one college, containing a total of 32 academic departments, with a strong emphasis on scientific and technological education and research.Founded in 1861 in...
's CTSS MAIL, in 1965.
Other early time-sharing system soon had their own email applications:
- 1972 - UnixUnixUnix is a multitasking, multi-user computer operating system originally developed in 1969 by a group of AT&T employees at Bell Labs, including Ken Thompson, Dennis Ritchie, Brian Kernighan, Douglas McIlroy, and Joe Ossanna...
mailMail (Unix)mail is a command line email client for Unix and Unix-like operating systems.-Example usage:mail -s "You've got mail" -c cc.rider@example.org somebody@example.com anotherbody@example.net...
program - 1972 - APL Mailbox by Larry BreedLawrence M. BreedLawrence M. Breed is a computer scientist, artist and inventor, best known for his involvement in the APL programming language.- Career :While at Stanford University in 1961, he created the first computer animation language, MACS, and demonstrated it publicly with Earl Boebert.While getting his M.S...
- 1981 - PROFSIBM OfficeVisionOfficeVision is an IBM proprietary office support application that primarily runs on IBM's VM operating system and its user interface CMS. Other platform versions are available, notably OV/MVS and OV/400...
by IBM - 1982 - ALL-IN-1ALL-IN-1ALL-IN-1 was an office automation product developed and sold by Digital Equipment Corporation in the 1980s. HP now maintains the current version Office Server V3.2 for OpenVMS Alpha and OpenVMS VAX systems....
by Digital Equipment CorporationDigital Equipment CorporationDigital Equipment Corporation was a major American company in the computer industry and a leading vendor of computer systems, software and peripherals from the 1960s to the 1990s...
Although similar in concept, all these original email systems had widely different features and ran on incompatible systems. They allowed communication only between users logged into the same host or "mainframe" - although this could be hundreds or even thousands of users within an organization.
Email networks
Soon systems were developed to link compatible mail programs between different organisations over dialup modems or leased lines, creating local and global networks.- In 1971 the first ARPANETARPANETThe Advanced Research Projects Agency Network , was the world's first operational packet switching network and the core network of a set that came to compose the global Internet...
email was sent, and through RFC 561, RFC 680, RFC 724—and finally 1977's RFC 733, became a standardized working system.
Other separate networks were also being created including:
- Unix mail was networked by 1978's uucpUUCPUUCP is an abbreviation for Unix-to-Unix Copy. The term generally refers to a suite of computer programs and protocols allowing remote execution of commands and transfer of files, email and netnews between computers. Specifically, a command named uucp is one of the programs in the suite; it...
, which was also used for USENETUsenetUsenet is a worldwide distributed Internet discussion system. It developed from the general purpose UUCP architecture of the same name.Duke University graduate students Tom Truscott and Jim Ellis conceived the idea in 1979 and it was established in 1980...
newsgroup postings - IBM mainframe email was linked by BITNETBITNETBITNET was a cooperative USA university network founded in 1981 by Ira Fuchs at the City University of New York and Greydon Freeman at Yale University...
in 1981 - IBM PC's running DOS in 1984 could link with FidoNetFidoNetFidoNet is a worldwide computer network that is used for communication between bulletin board systems. It was most popular in the early to mid 1990s, prior to the introduction of easy and affordable access to the Internet...
for email and shared bulletin board posting
LAN email systems
In the early 1980s, networked personal computerPersonal computer
A personal computer is any general-purpose computer whose size, capabilities, and original sales price make it useful for individuals, and which is intended to be operated directly by an end-user with no intervening computer operator...
s on LAN
Län
Län and lääni refer to the administrative divisions used in Sweden and previously in Finland. The provinces of Finland were abolished on January 1, 2010....
s became increasingly important. Server-based systems similar to the earlier mainframe systems were developed. Again these systems initially allowed communication only between users logged into the same server infrastructure. Examples include:
- cc:MailCc:Mailcc:Mail is an obsolete, store-and-forward LAN-based e-mail system originally developed on Microsoft's MS-DOS platform by Hubert Lipinski in the 1980s. At the height of its popularity cc:Mail had about 21 million users.-Message store:...
- LantasticLantasticLANtastic is a peer-to-peer local area network operating system for DOS, Microsoft Windows, Novell NetWare and OS/2. LANtastic supports Ethernet, ARCNET and Token Ring adapters as well as its original twisted-pair adapter at ....
- WordPerfect OfficeWordPerfect OfficeWordPerfect Office is an office suite developed by Corel Corporation. As of March 2010, the latest version is WordPerfect Office X5 , which is available in three editions: Home & Student, Standard and Professional....
- Microsoft MailMicrosoft MailMicrosoft Mail was the name given to several early Microsoft e-mail products.-Mac Networks:The first Microsoft Mail product was introduced in 1988 for AppleTalk Networks. It was based on InterMail, a product that Microsoft purchased and updated. An MS-DOS client was added for PCs on AppleTalk...
- Banyan VINESBanyan VINESBanyan VINES was a computer network operating system and the set of computer network protocols it used to talk to client machines on the network. The Banyan company based the VINES operating system on Unix, and the network protocols on the archetypical Xerox XNS stack...
- Lotus NotesLotus NotesLotus Notes is the client of a collaborative platform originally created by Lotus Development Corp. in 1989. In 1995 Lotus was acquired by IBM and became known as the Lotus Development division of IBM and is now part of the IBM Software Group...
Eventually these systems too could also be linked between different organizations, as long as they ran the same email system and proprietary protocol.
Attempts at interoperability
Early interoperability among independent systems included:- ARPANETARPANETThe Advanced Research Projects Agency Network , was the world's first operational packet switching network and the core network of a set that came to compose the global Internet...
, the forerunner of today's Internet, defined the first protocols for dissimilar computers to exchange email - uucpUUCPUUCP is an abbreviation for Unix-to-Unix Copy. The term generally refers to a suite of computer programs and protocols allowing remote execution of commands and transfer of files, email and netnews between computers. Specifically, a command named uucp is one of the programs in the suite; it...
implementations for non-Unix systems were used as an open "glue" between differing mail systems, primarily over dialup telephones - CSNetCSNETThe Computer Science Network was a computer network that began operation in 1981 in the United States. Its purpose was to extend networking benefits, for computer science departments at academic and research institutions that could not be directly connected to ARPANET, due to funding or...
used dial-up telephone access to link additional sites to the ARPANET and then Internet
Later efforts at interoperability standardization included:
- NovellNovellNovell, Inc. is a multinational software and services company. It is a wholly owned subsidiary of The Attachmate Group. It specializes in network operating systems, such as Novell NetWare; systems management solutions, such as Novell ZENworks; and collaboration solutions, such as Novell Groupwise...
briefly championed the open MHS protocol but abandoned it after purchasing the non-MHS WordPerfect Office (renamed GroupwiseNovell GroupWiseGroupWise is a messaging and collaborative software platform from Novell that supports email, calendaring, personal information management, instant messaging, and document management. The platform consists of the client software, which is available for Windows, Mac OS X, and Linux, and the server...
) - The Coloured Book protocolsColoured Book protocolsThe Coloured Book protocols were a set of computer network protocols used on the SERCnet and JANET X.25 packet-switched academic networks in the United Kingdom between 1980 and 1992...
on UKUnited KingdomThe United Kingdom of Great Britain and Northern IrelandIn the United Kingdom and Dependencies, other languages have been officially recognised as legitimate autochthonous languages under the European Charter for Regional or Minority Languages...
academic networks until 1992 - X.400X.400X.400 is a suite of ITU-T Recommendations that define standards for Data Communication Networks for Message Handling Systems — more commonly known as "email"....
in the 1980s and early 1990s was promoted by major vendors and mandated for government use under GOSIP but abandoned by all but a few — in favor of InternetInternetThe Internet is a global system of interconnected computer networks that use the standard Internet protocol suite to serve billions of users worldwide...
SMTP by the mid-1990s.
From SNDMSG to MSG
In the early 1970s, Ray Tomlinson updated an existing utility called SNDMSGSNDMSG
SNDMSG existed as a single-computer electronic mail program from the early 1960s for time-sharing operating systems. The early versions of SNDMSG allowed users to compose a message that would be stored in a file on another user's home directory.SNDMSG later became one component of a networked mail...
so that it could copy messages (as files) over the network. Lawrence Roberts
Lawrence Roberts (scientist)
Lawrence G. Roberts received the Draper Prize in 2001 and the Principe de Asturias Award in 2002 "for the development of the Internet" along with Leonard Kleinrock, Robert Kahn, and Vinton Cerf....
, the project manager for the ARPANET development, took the idea of READMAIL, which dumped all "recent" messages onto the user's terminal, and wrote a program for TENEX in TECO
Text Editor and Corrector
TECO is a text editor originally developed at the Massachusetts Institute of Technology in the 1960s, after which it was modified by 'just about everybody'...
macros called RD which permitted accessing individual messages. Barry Wessler then updated RD and called it NRD.
Marty Yonke combined rewrote NRD to include reading, access to SNDMSG for sending, and a help system, and called the utility WRD which was later known as BANANARD. John Vittal then updated this version to include 3 important commands: Move (combined save/delete command), Answer (determined to whom a reply should be sent) and Forward (send an email to a person who was not already a recipient). The system was called MSG. With inclusion of these features, MSG is considered to be the first integrated modern email program, from which many other applications have descended.
The rise of ARPANET mail
The ARPANET computer networkComputer network
A computer network, often simply referred to as a network, is a collection of hardware components and computers interconnected by communication channels that allow sharing of resources and information....
made a large contribution to the development of email. There is one report that indicates experimental inter-system email transfers began shortly after its creation in 1969. Ray Tomlinson
Ray Tomlinson
Raymond Samuel Tomlinson is a programmer who implemented an email system in 1971 on the ARPANET. Email had been previously sent on other networks such as AUTODIN and PLATO. It was the first system able to send mail between users on different hosts connected to the ARPAnet...
is generally credited as having sent the first email across a network, initiating the use of the "@
At sign
The at sign , also called the ampersat, apetail, arroba, atmark, at symbol, commercial at or monkey tail, is formally an abbreviation of the accounting and commercial invoice term "at the rate of"...
" sign to separate the names of the user and the user's machine in 1971, when he sent a message from one Digital Equipment Corporation
Digital Equipment Corporation
Digital Equipment Corporation was a major American company in the computer industry and a leading vendor of computer systems, software and peripherals from the 1960s to the 1990s...
DEC-10 computer to another DEC-10. The two machines were placed next to each other. Tomlinson's work was quickly adopted across the ARPANET, which significantly increased the popularity of email. For many years, email was the killer app
Killer application
A killer application , in the jargon of marketing teams, has been used to refer to any computer program that is so necessary or desirable that it proves the core value of some larger technology, such as computer hardware, gaming console, software, or an operating system...
of the ARPANET and then the Internet.
Most other networks had their own email protocols and address formats; as the influence of the ARPANET and later the Internet grew, central sites often hosted email gateways
Gateway (telecommunications)
In telecommunications, the term gateway has the following meaning:*In a communications network, a network node equipped for interfacing with another network that uses different protocols....
that passed mail between the Internet and these other networks. Internet email addressing is still complicated by the need to handle mail destined for these older networks. Some well-known examples of these were UUCP
UUCP
UUCP is an abbreviation for Unix-to-Unix Copy. The term generally refers to a suite of computer programs and protocols allowing remote execution of commands and transfer of files, email and netnews between computers. Specifically, a command named uucp is one of the programs in the suite; it...
(mostly Unix computers), BITNET
BITNET
BITNET was a cooperative USA university network founded in 1981 by Ira Fuchs at the City University of New York and Greydon Freeman at Yale University...
(mostly IBM and VAX mainframes at universities), FidoNet
FidoNet
FidoNet is a worldwide computer network that is used for communication between bulletin board systems. It was most popular in the early to mid 1990s, prior to the introduction of easy and affordable access to the Internet...
(personal computers), DECNET (various networks) and CSNET
CSNET
The Computer Science Network was a computer network that began operation in 1981 in the United States. Its purpose was to extend networking benefits, for computer science departments at academic and research institutions that could not be directly connected to ARPANET, due to funding or...
a forerunner of NSFNet
NSFNet
The National Science Foundation Network was a program of coordinated, evolving projects sponsored by the National Science Foundation beginning in 1985 to promote advanced research and education networking in the United States...
.
An example of an Internet email address that routed mail to a user at a UUCP host:
hubhost!middlehost!edgehost!user@uucpgateway.somedomain.example.com
This was necessary because in early years UUCP computers did not maintain (and could not consult central servers for) information about the location of all hosts they exchanged mail with, but rather only knew how to communicate with a few network neighbors; email messages (and other data such as Usenet News
Usenet
Usenet is a worldwide distributed Internet discussion system. It developed from the general purpose UUCP architecture of the same name.Duke University graduate students Tom Truscott and Jim Ellis conceived the idea in 1979 and it was established in 1980...
) were passed along in a chain among hosts who had explicitly agreed to share data with each other. (Eventually the UUCP Mapping Project would provide a form of network routing database for email.)
Operation overview
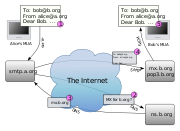
The diagram to the right shows a typical sequence of events that takes place when Alice composes a message using her mail user agentE-mail client
An email client, email reader, or more formally mail user agent , is a computer program used to manage a user's email.The term can refer to any system capable of accessing the user's email mailbox, regardless of it being a mail user agent, a relaying server, or a human typing on a terminal...
(MUA). She enters the email address of her correspondent, and hits the "send" button.
- Her MUA formats the message in email format and uses the Submission Protocol (a profile of the Simple Mail Transfer ProtocolSimple Mail Transfer ProtocolSimple Mail Transfer Protocol is an Internet standard for electronic mail transmission across Internet Protocol networks. SMTP was first defined by RFC 821 , and last updated by RFC 5321 which includes the extended SMTP additions, and is the protocol in widespread use today...
(SMTP), see RFC 6409) to send the message to the local mail submission agentMail submission agentA mail submission agent is a computer program or software agent that receives electronic mail messages from a mail user agent and cooperates with a mail transfer agent for delivery of the mail...
(MSA), in this case smtp.a.org, run by Alice's internet service providerInternet service providerAn Internet service provider is a company that provides access to the Internet. Access ISPs directly connect customers to the Internet using copper wires, wireless or fiber-optic connections. Hosting ISPs lease server space for smaller businesses and host other people servers...
(ISP). - The MSA looks at the destination address provided in the SMTP protocol (not from the message header), in this case bob@b.org. An Internet email address is a string of the form localpart@exampledomain. The part before the @ sign is the local part of the address, often the username of the recipient, and the part after the @ sign is a domain nameDomain nameA domain name is an identification string that defines a realm of administrative autonomy, authority, or control in the Internet. Domain names are formed by the rules and procedures of the Domain Name System ....
or a fully qualified domain name. The MSA resolves a domain name to determine the fully qualified domain name of the mail exchange server in the Domain Name SystemDomain name systemThe Domain Name System is a hierarchical distributed naming system for computers, services, or any resource connected to the Internet or a private network. It associates various information with domain names assigned to each of the participating entities...
(DNS). - The DNS server for the b.org domain, ns.b.org, responds with any MX recordMX recordA mail exchanger record is a type of resource record in the Domain Name System that specifies a mail server responsible for accepting email messages on behalf of a recipient's domain, and a preference value used to prioritize mail delivery if multiple mail servers are available...
s listing the mail exchange servers for that domain, in this case mx.b.org, a message transfer agent (MTA) server run by Bob's ISP. - smtp.a.org sends the message to mx.b.org using SMTP.
This server may need to forward the message to other MTAs before the message reaches the final message delivery agent (MDA).
- The MDA delivers it to the mailboxEmail mailboxAn email box is the equivalent of a letter box for electronic mail. It is the destination where electronic mail messages are delivered.-Definitions:...
of the user bob. - Bob presses the "get mail" button in his MUA, which picks up the message using either the Post Office ProtocolPost Office ProtocolIn computing, the Post Office Protocol is an application-layer Internet standard protocol used by local e-mail clients to retrieve e-mail from a remote server over a TCP/IP connection. POP and IMAP are the two most prevalent Internet standard protocols for e-mail retrieval. Virtually all modern...
(POP3) or the Internet Message Access ProtocolInternet Message Access ProtocolInternet message access protocol is one of the two most prevalent Internet standard protocols for e-mail retrieval, the other being the Post Office Protocol...
(IMAP4).
That sequence of events applies to the majority of email users. However, there are many alternative possibilities and complications to the email system:
- Alice or Bob may use a client connected to a corporate email system, such as IBMIBMInternational Business Machines Corporation or IBM is an American multinational technology and consulting corporation headquartered in Armonk, New York, United States. IBM manufactures and sells computer hardware and software, and it offers infrastructure, hosting and consulting services in areas...
Lotus NotesLotus NotesLotus Notes is the client of a collaborative platform originally created by Lotus Development Corp. in 1989. In 1995 Lotus was acquired by IBM and became known as the Lotus Development division of IBM and is now part of the IBM Software Group...
or MicrosoftMicrosoftMicrosoft Corporation is an American public multinational corporation headquartered in Redmond, Washington, USA that develops, manufactures, licenses, and supports a wide range of products and services predominantly related to computing through its various product divisions...
ExchangeMicrosoft Exchange ServerMicrosoft Exchange Server is the server side of a client–server, collaborative application product developed by Microsoft. It is part of the Microsoft Servers line of server products and is used by enterprises using Microsoft infrastructure products...
. These systems often have their own internal email format and their clients typically communicate with the email server using a vendor-specific, proprietary protocol. The server sends or receives email via the Internet through the product's Internet mail gateway which also does any necessary reformatting. If Alice and Bob work for the same company, the entire transaction may happen completely within a single corporate email system. - Alice may not have a MUA on her computer but instead may connect to a webmail service.
- Alice's computer may run its own MTA, so avoiding the transfer at step 1.
- Bob may pick up his email in many ways, for example logging into mx.b.org and reading it directly, or by using a webmail service.
- Domains usually have several mail exchange servers so that they can continue to accept mail when the main mail exchange server is not available.
- Email messages are not secure if email encryption is not used correctly.
Many MTAs used to accept messages for any recipient on the Internet and do their best to deliver them. Such MTAs are called open mail relay
Open mail relay
An open mail relay is an SMTP server configured in such a way that it allows anyone on the Internet to send e-mail through it, not just mail destined to or originating from known users...
s. This was very important in the early days of the Internet when network connections were unreliable. If an MTA couldn't reach the destination, it could at least deliver it to a relay closer to the destination. The relay stood a better chance of delivering the message at a later time. However, this mechanism proved to be exploitable by people sending unsolicited bulk email and as a consequence very few modern MTAs are open mail relays, and many MTAs don't accept messages from open mail relays because such messages are very likely to be spam.
Message format
The Internet email message format is defined in RFC 5322, with multi-media content attachments being defined in RFC 2045 through RFC 2049, collectively called Multipurpose Internet Mail Extensions or MIME. Prior to the introduction of RFC 2822 in 2001, the format described by RFC 822 was the standard for Internet email for nearly 20 years. RFC 822 was published in 1982 and based on the earlier RFC 733 for the ARPANET (see).Internet email messages consist of two major sections:
- Header — Structured into fieldsField (computer science)In computer science, data that has several parts can be divided into fields. Relational databases arrange data as sets of database records, also called rows. Each record consists of several fields; the fields of all records form the columns....
such as From, To, CC, Subject, Date, and other information about the email. - Body — The basic content, as unstructured text; sometimes containing a signature blockSignature blockA signature block is a block of text automatically appended at the bottom of an e-mail message, Usenet article, or forum post. This has the effect of "signing off" the message and in a reply message of indicating that no more response follows...
at the end. This is exactly the same as the body of a regular letter.
The header is separated from the body by a blank line.
Message header
Each message has exactly one header, which is structured into fieldsField (computer science)
In computer science, data that has several parts can be divided into fields. Relational databases arrange data as sets of database records, also called rows. Each record consists of several fields; the fields of all records form the columns....
. Each field has a name and a value. RFC 5322 specifies the precise syntax.
Informally, each line of text in the header that begins with a printable character begins a separate field. The field name starts in the first character of the line and ends before the separator character ":". The separator is then followed by the field value (the "body" of the field). The value is continued onto subsequent lines if those lines have a space or tab as their first character. Field names and values are restricted to 7-bit ASCII
ASCII
The American Standard Code for Information Interchange is a character-encoding scheme based on the ordering of the English alphabet. ASCII codes represent text in computers, communications equipment, and other devices that use text...
characters. Non-ASCII values may be represented using MIME encoded words.
Header fields
The message header must include at least the following fields:- From: The email address, and optionally the name of the author(s). In many email clients not changeable except through changing account settings.
- Date: The local time and date when the message was written. Like the From: field, many email clients fill this in automatically when sending. The recipient's client may then display the time in the format and time zone local to him/her.
The message header should include at least the following fields:
- Message-ID: Also an automatically generated field; used to prevent multiple delivery and for reference in In-Reply-To: (see below).
- In-Reply-To: Message-IDMessage-IDMessage-ID is a unique identifier for a digital message, most commonly a globally unique identifier used in email and Usenet newsgroups.Message-IDs are required to have a specific format which is a subset of an email address and to be globally unique...
of the message that this is a reply to. Used to link related messages together. This field only applies for reply messages.
RFC 3864 describes registration procedures for message header fields at the IANA
Internet Assigned Numbers Authority
The Internet Assigned Numbers Authority is the entity that oversees global IP address allocation, autonomous system number allocation, root zone management in the Domain Name System , media types, and other Internet Protocol-related symbols and numbers...
; it provides for permanent and provisional message header field names, including also fields defined for MIME, netnews, and http, and referencing relevant RFCs. Common header fields for email include:
- To: The email address(es), and optionally name(s) of the message's recipient(s). Indicates primary recipients (multiple allowed), for secondary recipients see Cc: and Bcc: below.
- Subject: A brief summary of the topic of the message. Certain abbreviations are commonly used in the subject, including "RE:" and "FW:".
- Bcc: Blind Carbon CopyBlind Carbon CopyIn the context of correspondence, blind carbon copy refers to the practice of sending a message to multiple recipients in such a way that conceals the fact that there may be additional addressees from the complete list of recipients...
; addresses added to the SMTP delivery list but not (usually) listed in the message data, remaining invisible to other recipients. - Cc: Carbon copyCarbon copyCarbon copying, abbreviated cc or c.c., is the technique of using carbon paper to produce one or more copies simultaneously during the creation of paper documents...
; Many email clients will mark email in your inbox differently depending on whether you are in the To: or Cc: list. - Content-Type: Information about how the message is to be displayed, usually a MIMEMIMEMultipurpose Internet Mail Extensions is an Internet standard that extends the format of email to support:* Text in character sets other than ASCII* Non-text attachments* Message bodies with multiple parts...
type. - Precedence: commonly with values "bulk", "junk", or "list"; used to indicate that automated "vacation" or "out of office" responses should not be returned for this mail, e.g. to prevent vacation notices from being sent to all other subscribers of a mailinglist. SendmailSendmailSendmail is a general purpose internetwork email routing facility that supports many kinds of mail-transfer and -delivery methods, including the Simple Mail Transfer Protocol used for email transport over the Internet....
uses this header to affect prioritization of queued email, with "Precedence: special-delivery" messages delivered sooner. With modern high-bandwidth networks delivery priority is less of an issue than it once was. Microsoft ExchangeMicrosoft Exchange ServerMicrosoft Exchange Server is the server side of a client–server, collaborative application product developed by Microsoft. It is part of the Microsoft Servers line of server products and is used by enterprises using Microsoft infrastructure products...
respects a fine-grained automatic response suppression mechanism, the X-Auto-Response-Suppress header. - Received: Tracking information generated by mail servers that have previously handled a message, in reverse order (last handler first).
- References: Message-IDMessage-IDMessage-ID is a unique identifier for a digital message, most commonly a globally unique identifier used in email and Usenet newsgroups.Message-IDs are required to have a specific format which is a subset of an email address and to be globally unique...
of the message that this is a reply to, and the message-id of the message the previous reply was a reply to, etc. - Reply-To: Address that should be used to reply to the message.
- Sender: Address of the actual sender acting on behalf of the author listed in the From: field (secretary, list manager, etc.).
- Archived-At: A direct link to the archived form of an individual email message.
Note that the To: field is not necessarily related to the addresses to which the message is delivered. The actual delivery list is supplied separately to the transport protocol, SMTP, which may or may not originally have been extracted from the header content. The "To:" field is similar to the addressing at the top of a conventional letter which is delivered according to the address on the outer envelope. Also note that the "From:" field does not have to be the real sender of the email message. One reason is that it is very easy to fake the "From:" field and let a message seem to be from any mail address. It is possible to digitally sign
Digital signature
A digital signature or digital signature scheme is a mathematical scheme for demonstrating the authenticity of a digital message or document. A valid digital signature gives a recipient reason to believe that the message was created by a known sender, and that it was not altered in transit...
email, which is much harder to fake, but such signatures require extra programming and often external programs to verify. Some ISPs do not relay email claiming to come from a domain not hosted by them, but very few (if any) check to make sure that the person or even email address named in the "From:" field is the one associated with the connection. Some ISPs apply email authentication systems to email being sent through their MTA to allow other MTAs to detect forged spam that might appear to come from them.
Recently the IETF EAI working group has defined some experimental extensions to allow Unicode
Unicode
Unicode is a computing industry standard for the consistent encoding, representation and handling of text expressed in most of the world's writing systems...
characters to be used within the header. In particular, this allows email addresses to use non-ASCII characters. Such characters must only be used by servers that support these extensions.
Content encoding
Email was originally designed for 7-bit ASCIIASCII
The American Standard Code for Information Interchange is a character-encoding scheme based on the ordering of the English alphabet. ASCII codes represent text in computers, communications equipment, and other devices that use text...
. Much email software is 8-bit clean
8-bit clean
8-bit clean describes a computer system that correctly handles 8-bit character sets, such as the ISO 8859 series and the UTF-8 encoding of Unicode.- History :...
but must assume it will communicate with 7-bit servers and mail readers. The MIME
MIME
Multipurpose Internet Mail Extensions is an Internet standard that extends the format of email to support:* Text in character sets other than ASCII* Non-text attachments* Message bodies with multiple parts...
standard introduced character set specifiers and two content transfer encodings to enable transmission of non-ASCII data: quoted printable for mostly 7 bit content with a few characters outside that range and base64
Base64
Base64 is a group of similar encoding schemes that represent binary data in an ASCII string format by translating it into a radix-64 representation...
for arbitrary binary data. The 8BITMIME and BINARY
Binary
- Mathematics :* Binary numeral system, a representation for numbers using only two digits * Binary function, a function in mathematics that takes two arguments- Computing :* Binary file, composed of something other than human-readable text...
extensions were introduced to allow transmission of mail without the need for these encodings, but many mail transport agents still do not support them fully. In some countries, several encoding schemes coexist; as the result, by default, the message in a non-Latin alphabet language appears in non-readable form (the only exception is coincidence, when the sender and receiver use the same encoding scheme). Therefore, for international character sets, Unicode
Unicode
Unicode is a computing industry standard for the consistent encoding, representation and handling of text expressed in most of the world's writing systems...
is growing in popularity.
Plain text and HTML
Most modern graphic email clients allow the use of either plain textPlain text
In computing, plain text is the contents of an ordinary sequential file readable as textual material without much processing, usually opposed to formatted text....
or HTML for the message body at the option of the user. HTML email messages often include an automatically generated plain text copy as well, for compatibility reasons.
Advantages of HTML include the ability to include in-line links and images, set apart previous messages in block quote
Block quote
A block quotation is a quotation in a written document, that set off from the main text as a paragraph, or block of text, and typically distinguished visually using indentation and a different typeface or smaller size quotation...
s, wrap naturally on any display, use emphasis such as underline
Underline
An underline, also called an underscore, is one or more horizontal lines immediately below a portion of writing. Single, and occasionally double , underlining was originally used in hand-written or typewritten documents to emphasise text...
s and italics, and change font
Font
In typography, a font is traditionally defined as a quantity of sorts composing a complete character set of a single size and style of a particular typeface...
styles. Disadvantages include the increased size of the email, privacy concerns about web bug
Web bug
A web bug is an object that is embedded in a web page or e-mail and is usually invisible to the user but allows checking that a user has viewed the page or e-mail. One common use is in e-mail tracking. Alternative names are web beacon, tracking bug, and tag or page tag...
s, abuse of HTML email as a vector for phishing
Phishing
Phishing is a way of attempting to acquire information such as usernames, passwords, and credit card details by masquerading as a trustworthy entity in an electronic communication. Communications purporting to be from popular social web sites, auction sites, online payment processors or IT...
attacks and the spread of malicious software
Malware
Malware, short for malicious software, consists of programming that is designed to disrupt or deny operation, gather information that leads to loss of privacy or exploitation, or gain unauthorized access to system resources, or that otherwise exhibits abusive behavior...
.
Some web based Mailing list
Mailing list
A mailing list is a collection of names and addresses used by an individual or an organization to send material to multiple recipients. The term is often extended to include the people subscribed to such a list, so the group of subscribers is referred to as "the mailing list", or simply "the...
s recommend that all posts be made in plain-text, with 72 or 80 characters per line
Characters per line
In typography and computing characters per line or terminal width refers to the maximal number of monospaced characters that may appear on a single line...
for all the above reasons, but also because they have a significant number of readers using text-based
Text user interface
TUI short for: Text User Interface or Textual User Interface , is a retronym that was coined sometime after the invention of graphical user interfaces, to distinguish them from text-based user interfaces...
email clients such as Mutt.
Some Microsoft
Microsoft
Microsoft Corporation is an American public multinational corporation headquartered in Redmond, Washington, USA that develops, manufactures, licenses, and supports a wide range of products and services predominantly related to computing through its various product divisions...
email clients allow rich formatting using RTF
Rich Text Format
The Rich Text Format is a proprietary document file format with published specification developed by Microsoft Corporation since 1987 for Microsoft products and for cross-platform document interchange....
, but unless the recipient is guaranteed to have a compatible email client this should be avoided.
In order to ensure that HTML sent in an email is rendered properly by the recipient's client software, an additional header must be specified when sending: "Content-type: text/html". Most email programs send this header automatically.
Servers and client applications
Messages are exchanged between hosts using the Simple Mail Transfer Protocol with software programs called mail transfer agentMail transfer agent
Within Internet message handling services , a message transfer agent or mail transfer agent or mail relay is software that transfers electronic mail messages from one computer to another using a client–server application architecture...
s (MTAs); and delivered to a mail store by programs called mail delivery agent
Mail delivery agent
A mail delivery agent or message delivery agent is a computer software component that is responsible for the delivery of e-mail messages to a local recipient's mailbox...
s (MDAs, also sometimes called local delivery agents, LDAs). Users can retrieve their messages from servers using standard protocols such as POP
Post Office Protocol
In computing, the Post Office Protocol is an application-layer Internet standard protocol used by local e-mail clients to retrieve e-mail from a remote server over a TCP/IP connection. POP and IMAP are the two most prevalent Internet standard protocols for e-mail retrieval. Virtually all modern...
or IMAP, or, as is more likely in a large corporate
Corporation
A corporation is created under the laws of a state as a separate legal entity that has privileges and liabilities that are distinct from those of its members. There are many different forms of corporations, most of which are used to conduct business. Early corporations were established by charter...
environment, with a proprietary
Proprietary software
Proprietary software is computer software licensed under exclusive legal right of the copyright holder. The licensee is given the right to use the software under certain conditions, while restricted from other uses, such as modification, further distribution, or reverse engineering.Complementary...
protocol specific to Novell Groupwise
Novell GroupWise
GroupWise is a messaging and collaborative software platform from Novell that supports email, calendaring, personal information management, instant messaging, and document management. The platform consists of the client software, which is available for Windows, Mac OS X, and Linux, and the server...
, Lotus Notes
Lotus Notes
Lotus Notes is the client of a collaborative platform originally created by Lotus Development Corp. in 1989. In 1995 Lotus was acquired by IBM and became known as the Lotus Development division of IBM and is now part of the IBM Software Group...
or Microsoft Exchange Server
Microsoft Exchange Server
Microsoft Exchange Server is the server side of a client–server, collaborative application product developed by Microsoft. It is part of the Microsoft Servers line of server products and is used by enterprises using Microsoft infrastructure products...
s. Webmail interfaces allow users to access their mail with any standard web browser
Web browser
A web browser is a software application for retrieving, presenting, and traversing information resources on the World Wide Web. An information resource is identified by a Uniform Resource Identifier and may be a web page, image, video, or other piece of content...
, from any computer, rather than relying on an email client. Programs used by users for retrieving, reading, and managing email are called mail user agents (MUAs).
Mail can be stored on the client
Client (computing)
A client is an application or system that accesses a service made available by a server. The server is often on another computer system, in which case the client accesses the service by way of a network....
, on the server
Server (computing)
In the context of client-server architecture, a server is a computer program running to serve the requests of other programs, the "clients". Thus, the "server" performs some computational task on behalf of "clients"...
side, or in both places. Standard formats for mailboxes include Maildir
Maildir
The Maildir e-mail format is a common way of storing e-mail messages, where each message is kept in a separate file with a unique name, and each folder is a directory...
and mbox
Mbox
mbox is a generic term for a family of related file formats used for holding collections of electronic mail messages. All messages in an mbox mailbox are concatenated and stored as plain text in a single file...
. Several prominent email clients use their own proprietary format and require conversion software to transfer email between them. Server-side storage is often in a proprietary format but since access is through a standard protocol such as IMAP, moving email from one server to another can be done with any MUA supporting the protocol.
Accepting a message obliges an MTA to deliver it, and when a message cannot be delivered, that MTA must send a bounce message
Bounce message
In the Internet's standard e-mail protocol SMTP, a bounce message, also called a Non-Delivery Report/Receipt , a Delivery Status Notification message, a Non-Delivery Notification or simply a bounce, is an automated electronic mail message from a mail system informing the sender of another...
back to the sender, indicating the problem.
Filename extensions
Upon reception of email messages, email client applications save messages in operating system files in the file system. Some clients save individual messages as separate files, while others use various database formats, often proprietary, for collective storage. A historical standard of storage is the mboxMbox
mbox is a generic term for a family of related file formats used for holding collections of electronic mail messages. All messages in an mbox mailbox are concatenated and stored as plain text in a single file...
format. The specific format used is often indicated by special filename extension
Filename extension
A filename extension is a suffix to the name of a computer file applied to indicate the encoding of its contents or usage....
s:
eml
- Used by many email clients including Microsoft Outlook Express, Windows MailWindows MailWindows Mail is an email and newsgroup client included in Windows Vista, that was superseded by Windows Live Mail. It is the successor to Outlook Express. Microsoft previewed Windows Mail on Channel 9 on October 10, 2005....
and Mozilla ThunderbirdMozilla ThunderbirdMozilla Thunderbird is a free, open source, cross-platform e-mail and news client developed by the Mozilla Foundation. The project strategy is modeled after Mozilla Firefox, a project aimed at creating a web browser...
. The files are plain textPlain textIn computing, plain text is the contents of an ordinary sequential file readable as textual material without much processing, usually opposed to formatted text....
in MIMEMIMEMultipurpose Internet Mail Extensions is an Internet standard that extends the format of email to support:* Text in character sets other than ASCII* Non-text attachments* Message bodies with multiple parts...
format, containing the email header as well as the message contents and attachments in one or more of several formats.
emlx
- Used by Apple MailMail (application)Mail is an email program included with Apple Inc.'s Mac OS X operating system. Originally developed by NeXT as NeXTMail, a part of their NeXTSTEP operating system, it was adapted, following Apple's acquisition of NeXT, to become OS X's Mail application.Mail uses the SMTP, POP3, and IMAP protocols,...
.
msg
- Used by Microsoft Office OutlookMicrosoft OutlookMicrosoft Outlook is a personal information manager from Microsoft, available both as a separate application as well as a part of the Microsoft Office suite...
and OfficeLogic Groupware.
mbx
- Used by Opera Mail, KMail, and Apple MailMail (application)Mail is an email program included with Apple Inc.'s Mac OS X operating system. Originally developed by NeXT as NeXTMail, a part of their NeXTSTEP operating system, it was adapted, following Apple's acquisition of NeXT, to become OS X's Mail application.Mail uses the SMTP, POP3, and IMAP protocols,...
based on the mboxMboxmbox is a generic term for a family of related file formats used for holding collections of electronic mail messages. All messages in an mbox mailbox are concatenated and stored as plain text in a single file...
format.
Some applications (like Apple Mail
Mail (application)
Mail is an email program included with Apple Inc.'s Mac OS X operating system. Originally developed by NeXT as NeXTMail, a part of their NeXTSTEP operating system, it was adapted, following Apple's acquisition of NeXT, to become OS X's Mail application.Mail uses the SMTP, POP3, and IMAP protocols,...
) leave attachments encoded in messages for searching while also saving separate copies of the attachments. Others separate attachments from messages and save them in a specific directory.
URI scheme mailto:
The URI schemeURI scheme
In the field of computer networking, a URI scheme is the top level of the Uniform Resource Identifier naming structure. All URIs and absolute URI references are formed with a scheme name, followed by a colon character , and the remainder of the URI called the scheme-specific part...
, as registered with the IANA
Internet Assigned Numbers Authority
The Internet Assigned Numbers Authority is the entity that oversees global IP address allocation, autonomous system number allocation, root zone management in the Domain Name System , media types, and other Internet Protocol-related symbols and numbers...
, defines the mailto: scheme for SMTP email addresses. Though its use is not strictly defined, URLs of this form are intended to be used to open the new message window of the user's mail client when the URL is activated, with the address as defined by the URL in the To: field.
In society
There are numerous ways in which people have changed the way they communicate in the last 50 years; email is certainly one of them. Traditionally, social interaction in the local community was the basis for communication – face to face. Yet, today face-to-face meetings are no longer the primary way to communicate as one can use a landline telephone, mobile phoneMobile phone
A mobile phone is a device which can make and receive telephone calls over a radio link whilst moving around a wide geographic area. It does so by connecting to a cellular network provided by a mobile network operator...
s, fax
Fax
Fax , sometimes called telecopying, is the telephonic transmission of scanned printed material , normally to a telephone number connected to a printer or other output device...
services, or any number of the computer mediated communications such as email.
Flaming
Flaming occurs when a person sends a message with angry or antagonistic content. The term is derived from the use of the word Incendiary to describe particularly heated email discussions. Flaming is assumed to be more common today because of the ease and impersonality of email communications: confrontations in person or via telephone require direct interaction, where social norms encourage civility, whereas typing a message to another person is an indirect interaction, so civility may be forgotten. Flaming is generally looked down upon by Internet communities as it is considered rude and non-productive.Email bankruptcy
Also known as "email fatigue", email bankruptcy is when a user ignores a large number of email messages after falling behind in reading and answering them. The reason for falling behind is often due to information overload and a general sense there is so much information that it is not possible to read it all. As a solution, people occasionally send a boilerplate message explaining that the email inbox is being cleared out. Harvard UniversityHarvard University
Harvard University is a private Ivy League university located in Cambridge, Massachusetts, United States, established in 1636 by the Massachusetts legislature. Harvard is the oldest institution of higher learning in the United States and the first corporation chartered in the country...
law professor Lawrence Lessig
Lawrence Lessig
Lawrence "Larry" Lessig is an American academic and political activist. He is best known as a proponent of reduced legal restrictions on copyright, trademark, and radio frequency spectrum, particularly in technology applications, and he has called for state-based activism to promote substantive...
is credited with coining this term, but he may only have popularized it.
In business
Email was widely accepted by the business community as the first broad electronic communication medium and was the first ‘e-revolution’ in business communication. Email is very simple to understand and like postal mail, email solves two basic problems of communication: logistics and synchronization (see below).LAN based email is also an emerging form of usage for business. It not only allows the business user to download mail when offline, it also allows the small business user to have multiple users' email IDs with just one email connection.
Pros
- The problem of logistics: Much of the business world relies upon communications between people who are not physically in the same building, area or even country; setting up and attending an in-person meeting, telephone callTelephone callA telephone call is a connection over a telephone network between the calling party and the called party.-Information transmission:A telephone call may carry ordinary voice transmission using a telephone, data transmission when the calling party and called party are using modems, or facsimile...
, or conference callConference callA conference call is a telephone call in which the calling party wishes to have more than one called party listen in to the audio portion of the call. The conference calls may be designed to allow the called party to participate during the call, or the call may be set up so that the called party...
can be inconvenient, time-consuming, and costly. Email provides a way to exchange information between two or more people with no set-up costs and that is generally far less expensive than physical meetings or phone calls. - The problem of synchronisation: With real timeReal-time computingIn computer science, real-time computing , or reactive computing, is the study of hardware and software systems that are subject to a "real-time constraint"— e.g. operational deadlines from event to system response. Real-time programs must guarantee response within strict time constraints...
communication by meetings or phone calls, participants have to work on the same schedule, and each participant must spend the same amount of time in the meeting or call. Email allows asynchronyAsynchronyAsynchrony, in the general meaning, is the state of not being synchronized.* Asynchronous learning* Collaborative editing systemsIn specific terms of digital logic and physical layer of communication, an asynchronous process does not require a clock signal, in contrast with synchronous and...
: each participant may control their schedule independently.
Cons
Most business workers today spend from one to two hours of their working day on email: reading, ordering, sorting, ‘re-contextualizing’ fragmented information, and writing email. The use of email is increasing due to increasing levels of globalisation—labour division and outsourcing amongst other things. Email can lead to some well-known problems:- Loss of context: which means that the context is lost forever; there is no way to get the text back. Information in context (as in a newspaper) is much easier and faster to understand than unedited and sometimes unrelated fragments of information. Communicating in context can only be achieved when both parties have a full understanding of the context and issue in question.
- Information overload: Email is a push technologyPush technologyPush technology, or server push, describes a style of Internet-based communication where the request for a given transaction is initiated by the publisher or central server...
—the sender controls who receives the information. Convenient availability of mailing listMailing listA mailing list is a collection of names and addresses used by an individual or an organization to send material to multiple recipients. The term is often extended to include the people subscribed to such a list, so the group of subscribers is referred to as "the mailing list", or simply "the...
s and use of "copy all" can lead to people receiving unwanted or irrelevant information of no use to them. - Inconsistency: Email can duplicate information. This can be a problem when a large team is working on documents and information while not in constant contact with the other members of their team.
- Liability. Statements made in an email can be deemed legally binding and be used against a party in a Court of law.
Despite these disadvantages, email has become the most widely used medium of communication within the business world. In fact, a 2010 study on workplace communication, found that 83% of U.S. knowledge workers felt that email was critical to their success and productivity at work.
Attachment size limitation
Email messages may have one or more attachments. Attachments serve the purpose of delivering binary or text files of unspecified size. In principle there is no technical intrinsic restriction in the SMTP protocol limiting the size or number of attachments. In practice, however, email service providers implement various limitations on the permissible size of files or the size of an entire message.Furthermore, due to technical reasons, often a small attachment can increase in size when sent, which can be confusing to senders when trying to assess whether they can or cannot send a file by email, and this can result in their message being rejected.
As larger and larger file sizes are being created and traded, many users are either forced to upload and download their files using an FTP server, or more popularly, use online file sharing facilities or services, usually over web-friendly HTTP, in order to send and receive them.
Information overload
A December 2007 New York Times blog post described information overload as "a $650 Billion Drag on the Economy", and the New York Times reported in April 2008 that "E-MAIL has become the bane of some people’s professional lives" due to information overload, yet "none of the current wave of high-profile Internet start-ups focused on email really eliminates the problem of email overload because none helps us prepare replies". GigaOm posted a similar article in September 2010, highlighting research that found 57% of knowledge workers were overwhelmed by the volume of email they received. Technology investors reflect similar concerns.In October 2010, CNN published an article titled "Happy Information Overload Day" that compiled research on email overload from IT companies and productivity experts. According to Basex, the average knowledge worker receives 93 emails a day. Subsequent studies have reported higher numbers. Marsha Egan, an email productivity expert, called email technology both a blessing and a curse in the article. She stated, "Everyone just learns that they have to have it dinging and flashing and open just in case the boss e-mails," she said. "The best gift any group can give each other is to never use e-mail urgently. If you need it within three hours, pick up the phone."
Spamming and computer viruses
The usefulness of email is being threatened by four phenomena: email bombardment, spammingE-mail spam
Email spam, also known as junk email or unsolicited bulk email , is a subset of spam that involves nearly identical messages sent to numerous recipients by email. Definitions of spam usually include the aspects that email is unsolicited and sent in bulk. One subset of UBE is UCE...
, phishing
Phishing
Phishing is a way of attempting to acquire information such as usernames, passwords, and credit card details by masquerading as a trustworthy entity in an electronic communication. Communications purporting to be from popular social web sites, auction sites, online payment processors or IT...
, and email worms
Computer worm
A computer worm is a self-replicating malware computer program, which uses a computer network to send copies of itself to other nodes and it may do so without any user intervention. This is due to security shortcomings on the target computer. Unlike a computer virus, it does not need to attach...
.
Spamming is unsolicited commercial (or bulk) email. Because of the minuscule cost of sending email, spammers can send hundreds of millions of email messages each day over an inexpensive Internet connection. Hundreds of active spammers sending this volume of mail results in information overload
Information overload
"Information overload" is a term popularized by Alvin Toffler in his bestselling 1970 book Future Shock. It refers to the difficulty a person can have understanding an issue and making decisions that can be caused by the presence of too much information...
for many computer users who receive voluminous unsolicited email each day.
Email worms use email as a way of replicating themselves into vulnerable computers. Although the first email worm
Morris (computer worm)
The Morris worm or Internet worm of November 2, 1988 was one of the first computer worms distributed via the Internet. It is considered the first worm and was certainly the first to gain significant mainstream media attention. It also resulted in the first conviction in the US under the 1986...
affected UNIX
Unix
Unix is a multitasking, multi-user computer operating system originally developed in 1969 by a group of AT&T employees at Bell Labs, including Ken Thompson, Dennis Ritchie, Brian Kernighan, Douglas McIlroy, and Joe Ossanna...
computers, the problem is most common today on the more popular Microsoft Windows
Microsoft Windows
Microsoft Windows is a series of operating systems produced by Microsoft.Microsoft introduced an operating environment named Windows on November 20, 1985 as an add-on to MS-DOS in response to the growing interest in graphical user interfaces . Microsoft Windows came to dominate the world's personal...
operating system.
The combination of spam and worm programs results in users receiving a constant drizzle of junk email, which reduces the usefulness of email as a practical tool.
A number of anti-spam techniques mitigate the impact of spam. In the United States
United States
The United States of America is a federal constitutional republic comprising fifty states and a federal district...
, U.S. Congress has also passed a law, the Can Spam Act of 2003, attempting to regulate such email. Australia
Australia
Australia , officially the Commonwealth of Australia, is a country in the Southern Hemisphere comprising the mainland of the Australian continent, the island of Tasmania, and numerous smaller islands in the Indian and Pacific Oceans. It is the world's sixth-largest country by total area...
also has very strict spam laws restricting the sending of spam from an Australian ISP, but its impact has been minimal since most spam comes from regimes that seem reluctant to regulate the sending of spam.
Email spoofing
Email spoofing occurs when the header information of an email is altered to make the message appear to come from a known or trusted source. It is often used as a ruse to collect personal information.Email bombing
Email bombing is the intentional sending of large volumes of messages to a target address. The overloading of the target email address can render it unusable and can even cause the mail server to crash.Privacy concerns
Today it can be important to distinguish between Internet and internal email systems. Internet email may travel and be stored on networks and computers without the sender's or the recipient's control. During the transit time it is possible that third parties read or even modify the content. Internal mail systems, in which the information never leaves the organizational network, may be more secure, although information technologyInformation technology
Information technology is the acquisition, processing, storage and dissemination of vocal, pictorial, textual and numerical information by a microelectronics-based combination of computing and telecommunications...
personnel and others whose function may involve monitoring or managing may be accessing the email of other employees.
Email privacy, without some security precautions, can be compromised because:
- email messages are generally not encrypted.
- email messages have to go through intermediate computers before reaching their destination, meaning it is relatively easy for others to intercept and read messages.
- many Internet Service Providers (ISP) store copies of email messages on their mail servers before they are delivered. The backups of these can remain for up to several months on their server, despite deletion from the mailbox.
- the "Received:"-fields and other information in the email can often identify the sender, preventing anonymous communication.
There are cryptography
Cryptography
Cryptography is the practice and study of techniques for secure communication in the presence of third parties...
applications that can serve as a remedy to one or more of the above. For example, Virtual Private Network
Virtual private network
A virtual private network is a network that uses primarily public telecommunication infrastructure, such as the Internet, to provide remote offices or traveling users access to a central organizational network....
s or the Tor anonymity network
Tor (anonymity network)
Tor is a system intended to enable online anonymity. Tor client software routes Internet traffic through a worldwide volunteer network of servers in order to conceal a user's location or usage from someone conducting network surveillance or traffic analysis...
can be used to encrypt traffic from the user machine to a safer network while GPG
GNU Privacy Guard
GNU Privacy Guard is a GPL Licensed alternative to the PGP suite of cryptographic software. GnuPG is compliant with RFC 4880, which is the current IETF standards track specification of OpenPGP...
, PGP
Pretty Good Privacy
Pretty Good Privacy is a data encryption and decryption computer program that provides cryptographic privacy and authentication for data communication. PGP is often used for signing, encrypting and decrypting texts, E-mails, files, directories and whole disk partitions to increase the security...
, SMEmail, or S/MIME
S/MIME
S/MIME is a standard for public key encryption and signing of MIME data. S/MIME is on an IETF standards track and defined in a number of documents, most importantly RFCs. S/MIME was originally developed by RSA Data Security Inc...
can be used for end-to-end
End-to-end principle
The end-to-end principle is a classic design principle of computer networking which states that application specific functions ought to reside in the end hosts of a network rather than in intermediary nodes, provided they can be implemented "completely and correctly" in the end hosts...
message encryption, and SMTP STARTTLS or SMTP over Transport Layer Security
Transport Layer Security
Transport Layer Security and its predecessor, Secure Sockets Layer , are cryptographic protocols that provide communication security over the Internet...
/Secure Sockets Layer can be used to encrypt communications for a single mail hop between the SMTP client and the SMTP server.
Additionally, many mail user agents do not protect logins and passwords, making them easy to intercept by an attacker. Encrypted authentication schemes such as SASL
Simple Authentication and Security Layer
Simple Authentication and Security Layer is a framework for authentication and data security in Internet protocols. It decouples authentication mechanisms from application protocols, in theory allowing any authentication mechanism supported by SASL to be used in any application protocol that uses...
prevent this.
Finally, attached files share many of the same hazards as those found in peer-to-peer filesharing
Peer-to-peer
Peer-to-peer computing or networking is a distributed application architecture that partitions tasks or workloads among peers. Peers are equally privileged, equipotent participants in the application...
. Attached files may contain trojans
Trojan horse (computing)
A Trojan horse, or Trojan, is software that appears to perform a desirable function for the user prior to run or install, but steals information or harms the system. The term is derived from the Trojan Horse story in Greek mythology.-Malware:A destructive program that masquerades as a benign...
or viruses
Computer virus
A computer virus is a computer program that can replicate itself and spread from one computer to another. The term "virus" is also commonly but erroneously used to refer to other types of malware, including but not limited to adware and spyware programs that do not have the reproductive ability...
.
Tracking of sent mail
The original SMTP mail service provides limited mechanisms for tracking a transmitted message, and none for verifying that it has been delivered or read. It requires that each mail server must either deliver it onward or return a failure notice (bounce message), but both software bugs and system failures can cause messages to be lost. To remedy this, the IETFInternet Engineering Task Force
The Internet Engineering Task Force develops and promotes Internet standards, cooperating closely with the W3C and ISO/IEC standards bodies and dealing in particular with standards of the TCP/IP and Internet protocol suite...
introduced Delivery Status Notifications (delivery receipts) and Message Disposition Notifications (return receipts); however, these are not universally deployed in production. (A complete Message Tracking mechanism was also defined, but it never gained traction; see RFCs 3885 through 3888.)
Many ISPs now deliberately disable non-delivery reports (NDRs) and delivery receipts due to the activities of spammers:
- Delivery Reports can be used to verify whether an address exists and so is available to be spammed
- If the spammer uses a forged sender email address (email spoofing), then the innocent email address that was used can be flooded with NDRs from the many invalid email addresses the spammer may have attempted to mail. These NDRs then constitute spam from the ISP to the innocent user
There are a number of systems that allow the sender to see if messages have been opened. The receiver could also let the sender know that the emails have been opened through an "Okay" button. A check sign can appear in the sender's screen when the receiver's "Okay" button is pressed.
US Government
The US Government has been involved in email in several different ways.Starting in 1977, the US Postal Service (USPS) recognized that electronic mail and electronic transactions posed a significant threat to First Class mail volumes and revenue. Therefore, the USPS initiated an experimental email service known as E-COM. Electronic messages were transmitted to a post office, printed out, and delivered as hard copy. To take advantage of the service, an individual had to transmit at least 200 messages. The delivery time of the messages was the same as First Class mail and cost 26 cents. Both the Postal Regulatory Commission and the Federal Communications Commission
Federal Communications Commission
The Federal Communications Commission is an independent agency of the United States government, created, Congressional statute , and with the majority of its commissioners appointed by the current President. The FCC works towards six goals in the areas of broadband, competition, the spectrum, the...
opposed E-COM. The FCC concluded that E-COM constituted common carriage under its jurisdiction and the USPS would have to file a tariff
Tariff
A tariff may be either tax on imports or exports , or a list or schedule of prices for such things as rail service, bus routes, and electrical usage ....
. Three years after initiating the service, USPS canceled E-COM and attempted to sell it off.
The early ARPANET dealt with multiple email clients that had various, and at times incompatible, formats. For example, in the Multics
Multics
Multics was an influential early time-sharing operating system. The project was started in 1964 in Cambridge, Massachusetts...
, the "@" sign meant "kill line" and anything before the "@" sign was ignored, so Multics users had to use a command-line option to specify the destination system. The Department of Defense
United States Department of Defense
The United States Department of Defense is the U.S...
DARPA desired to have uniformity and interoperability for email and therefore funded efforts to drive towards unified inter-operable standards. This led to David Crocker, John Vittal, Kenneth Pogran, and Austin Henderson publishing RFC 733, "Standard for the Format of ARPA Network Text Message" (November 21, 1977), which was apparently not effective. In 1979, a meeting was held at BBN to resolve incompatibility issues. Jon Postel
Jon Postel
Jonathan Bruce Postel was an American computer scientist who made many significant contributions to the development of the Internet, particularly with respect to standards...
recounted the meeting in RFC 808, "Summary of Computer Mail Services Meeting Held at BBN on 10 January 1979" (March 1, 1982), which includes an appendix listing the varying email systems at the time. This, in turn, lead to the release of David Crocker's RFC 822, "Standard for the Format of ARPA Internet Text Messages" (August 13, 1982).
The National Science Foundation
National Science Foundation
The National Science Foundation is a United States government agency that supports fundamental research and education in all the non-medical fields of science and engineering. Its medical counterpart is the National Institutes of Health...
took over operations of the ARPANET and Internet from the Department of Defense, and initiated NSFNet
NSFNet
The National Science Foundation Network was a program of coordinated, evolving projects sponsored by the National Science Foundation beginning in 1985 to promote advanced research and education networking in the United States...
, a new backbone
Backbone network
A backbone network or network backbone is a part of computer network infrastructure that interconnects various pieces of network, providing a path for the exchange of information between different LANs or subnetworks. A backbone can tie together diverse networks in the same building, in different...
for the network. A part of the NSFNet AUP forbade commercial traffic. In 1988, Vint Cerf
Vint Cerf
Vinton Gray "Vint" Cerf is an American computer scientist, who is recognized as one of "the fathers of the Internet", sharing this title with American computer scientist Bob Kahn...
arranged for an interconnection of MCI Mail
MCI Mail
MCI Mail was a commercial email service that was operated by MCI Communications Corp. during the period 1983 - 2003. The service is widely credited with being the first commercial email service in the United States.-History:...
with NSFNET on an experimental basis. The following year Compuserve email interconnected with NSFNET. Within a few years the commercial traffic restriction was removed from NSFNETs AUP, and NSFNET was privatised.
In the late 1990s, the Federal Trade Commission
Federal Trade Commission
The Federal Trade Commission is an independent agency of the United States government, established in 1914 by the Federal Trade Commission Act...
grew concerned with fraud transpiring in email, and initiated a series of procedures on spam, fraud, and phishing. In 2004, FTC jurisdiction over spam was codified into law in the form of the CAN SPAM Act. Several other US Federal Agencies have also exercised jurisdiction including the Department of Justice
United States Department of Justice
The United States Department of Justice , is the United States federal executive department responsible for the enforcement of the law and administration of justice, equivalent to the justice or interior ministries of other countries.The Department is led by the Attorney General, who is nominated...
and the Secret Service
United States Secret Service
The United States Secret Service is a United States federal law enforcement agency that is part of the United States Department of Homeland Security. The sworn members are divided among the Special Agents and the Uniformed Division. Until March 1, 2003, the Service was part of the United States...
.
NASA has provided email capabilities to astronauts aboard the Space Shuttle and Internationals Space Station since 1991 when a Macintosh Portable
Macintosh Portable
The Macintosh Portable was Apple Inc.'s first attempt at making a battery-powered portable Macintosh personal computer that held the power of a desktop Macintosh...
was used aboard Space Shuttle
Space Shuttle
The Space Shuttle was a manned orbital rocket and spacecraft system operated by NASA on 135 missions from 1981 to 2011. The system combined rocket launch, orbital spacecraft, and re-entry spaceplane with modular add-ons...
mission STS-43
STS-43
-Mission parameters:*Mass:**Orbiter landing with payload: **Payload: *Perigee: *Apogee: *Inclination: 28.5°*Period: 90.6 min-Preparations and Launch:The launch took place on 2 August 1991, 11:01:59 am EDT...
to send the first email via AppleLink
AppleLink
AppleLink was the name of both Apple Computer's online service for its dealers, third party developers, and users, and the client software used to access it. Prior to the commercialization of the Internet, AppleLink was a popular service for Mac and Apple IIGS users...
. Today astronauts aboard the International Space Station have email capabilities through the via wireless networking
Wi-Fi
Wi-Fi or Wifi, is a mechanism for wirelessly connecting electronic devices. A device enabled with Wi-Fi, such as a personal computer, video game console, smartphone, or digital audio player, can connect to the Internet via a wireless network access point. An access point has a range of about 20...
throughout the station and are connected to the ground at 3 Mbit/s Earth to station and 10 Mbit/s station to Earth, comparable to home DSL connection speeds.
Email terminologies
- Email encryption
- HTML email
- Internet faxInternet faxInternet fax uses the Internet to receive and send faxes.Internet faxing, "e-Fax" or "online faxing" is a general term which refers to sending a document facsimile using the Internet, rather than using only phone networks with a fax machine.Depending on the specific method/implementation ,...
- L- or letter mail, email letter and letter email
- Privacy-enhanced Electronic MailPrivacy-enhanced Electronic MailPrivacy Enhanced Mail , is a 1993 IETF proposal for securing email using public-key cryptography. Although PEM became an IETF proposed standard it was never widely deployed or used....
- Push email
- X-Originating-IPX-Originating-IPThe X-Originating-IP Email header field is a de facto standard for identifying the originating IP address of a client connecting to a mail server.- Format :The general format of the field is:...
Email social issues
- Anti-spam techniques (email)
- CompuServeCompuServeCompuServe was the first major commercial online service in the United States. It dominated the field during the 1980s and remained a major player through the mid-1990s, when it was sidelined by the rise of services such as AOL with monthly subscriptions rather than hourly rates...
(first consumer service) - Computer virusComputer virusA computer virus is a computer program that can replicate itself and spread from one computer to another. The term "virus" is also commonly but erroneously used to refer to other types of malware, including but not limited to adware and spyware programs that do not have the reproductive ability...
- E-cardE-cardAn e-card is similar to a postcard or greeting card, with the primary difference being that it is created using digital media instead of paper or other traditional materials. E-cards are made available by publishers usually on various Internet sites, where they can be sent to a recipient, usually...
- E-mail artE-mail artEmail art is simply any kind of art sent by email. It includes computer graphics, animations, screensavers, digital scans of artwork in other media, or even ASCII art...
- E-mail jammingE-mail jammingEmail jamming is the use of sensitive words in emails to jam the authorities that listen in on them by providing a form of a red herring and an intentional annoyance. It is used by some civil rights activists in an attempt to thwart government spy networks such as ECHELON...
- E-mail spamE-mail spamEmail spam, also known as junk email or unsolicited bulk email , is a subset of spam that involves nearly identical messages sent to numerous recipients by email. Definitions of spam usually include the aspects that email is unsolicited and sent in bulk. One subset of UBE is UCE...
- E-mail spoofingE-mail spoofingEmail spoofing is email activity in which the sender address and other parts of the email header are altered to appear as though the email originated from a different source. Because core SMTP doesn't provide any authentication, it is easy to impersonate and forge emails...
- E-mail stormE-mail stormAn email storm is a sudden spike of Reply All messages on an email distribution list, usually caused by a controversial or misdirected message. Such storms start when multiple members of the distribution list reply to the entire list at the same time in response to the instigating message...
- E-mail subject abbreviations
- Information overloadInformation overload"Information overload" is a term popularized by Alvin Toffler in his bestselling 1970 book Future Shock. It refers to the difficulty a person can have understanding an issue and making decisions that can be caused by the presence of too much information...
- Internet humorInternet humorThe Internet has long been a resource for the circulation of humorous ideas and jokes. Countless web-sites are devoted to the collection of Internet humor, and every day e-mail crosses the world, containing the text of humorous articles, or jokes about current events."Internet humor" is...
- Internet slangInternet slangInternet slang is a type of slang that Internet users have popularized, and in many cases, have coined. Such terms often originate with the purpose of saving keystrokes. Many people use the same abbreviations in texting and instant messaging, and social networking websites...
- NetiquetteNetiquetteNetiquette is a set of social conventions that facilitate interaction over networks, ranging from Usenet and mailing lists to blogs and forums. These rules were described in IETF RFC 1855. However, like many Internet phenomena, the concept and its application remain in a state of flux, and vary...
- Usenet quotingUsenet quotingWhen Usenet and e-mail users respond to a message, they often want to include some context for the discussion. This is often accomplished by quoting a portion of the original message.-Examples:...
Clients and servers
- Biff
- Email address
- Email authentication
- Email client, Comparison of email clients
- Email hosting service
- Internet mail standardInternet mail standardInternet e-mail functions through the use ofInternet standards. Although many more standards actually apply to e-mail, virtually all mail servers and e-mail clients support at least the following basic set....
s - Mail transfer agentMail transfer agentWithin Internet message handling services , a message transfer agent or mail transfer agent or mail relay is software that transfers electronic mail messages from one computer to another using a client–server application architecture...
- Mail user agent
- Unicode and email
- Webmail
Mailing list
- Anonymous remailerAnonymous remailerAn anonymous remailer is a server computer which receives messages with embedded instructions on where to send them next, and which forwards them without revealing where they originally came from...
- Disposable email address
- Email digestEmail digestAn email digest is an email that is automatically generated by an electronic mailing list and which combines all exchanged emails during a time period or when a volume limit is reached An email digest is an email that is automatically generated by an electronic mailing list and which combines all...
- E-mail encryptionE-mail encryptionEmail encryption refers to encryption, and often authentication, of email messages, which can be done in order to protect the content from being read by unintended recipients....
- E-mail trackingE-mail trackingEmail tracking is a method for monitoring the email delivery to intended recipient. Most tracking technologies utilize some form of digitally time-stamped record to reveal the exact time and date that your email was received or opened, as well the IP address of the recipient.Email tracking is...
- Electronic mailing listElectronic mailing listAn electronic mailing list is a special usage of email that allows for widespread distribution of information to many Internet users. It is similar to a traditional mailing list — a list of names and addresses — as might be kept by an organization for sending publications to...
- Mailer-Daemon
- Mailing list archive
Further reading
- Cemil Betanov, Introduction to X.400, Artech House, ISBN 0-89006-597-7.
- Marsha Egan, "Inbox Detox and The Habit of Email Excellence", Acanthus Publishing ISBN 978-0981558981
- Lawrence Hughes, Internet e-mail Protocols, Standards and Implementation, Artech House Publishers, ISBN 0-89006-939-5.
- Kevin Johnson, Internet Email Protocols: A Developer's Guide, Addison-Wesley Professional, ISBN 0-201-43288-9.
- Pete Loshin, Essential Email Standards: RFCs and Protocols Made Practical, John Wiley & Sons, ISBN 0-471-34597-0. }}
- Sara Radicati, Electronic Mail: An Introduction to the X.400 Message Handling Standards, Mcgraw-Hill, ISBN 0-07-051104-7.
- John Rhoton, Programmer's Guide to Internet Mail: SMTP, POP, IMAP, and LDAP, Elsevier, ISBN 1-55558-212-5.
- John Rhoton, X.400 and SMTP: Battle of the E-mail Protocols, Elsevier, ISBN 1-55558-165-X.
- David Wood, Programming Internet Mail, O'Reilly, ISBN 1-56592-479-7.
- Yoram M. Kalman & Sheizaf Rafaeli, Online Pauses and Silence: Chronemic Expectancy Violations in Written Computer-Mediated Communication, Communication Research, Vol. 38, pp. 54–69, 2011
External links
- IANA's list of standard header fields
- The History of Electronic Mail is a personal memoir by the implementer of an early email system

