Domain name system
Encyclopedia
The Domain Name System is a hierarchical distributed naming system for computers, services, or any resource connected to the Internet
or a private network
. It associates various information with domain name
s assigned to each of the participating entities. Most importantly, it translates domain names meaningful to humans into the numerical identifiers associated with networking equipment for the purpose of locating and addressing these devices worldwide.
An often-used analogy to explain the Domain Name System is that it serves as the phone book
for the Internet by translating human-friendly computer hostname
s into IP address
es. For example, the domain name www.example.com
translates to the addresses 192.0.32.10 (IPv4
) and 2620:0:2d0:200::10 (IPv6
).
The Domain Name System makes it possible to assign domain name
s to groups of Internet resources and users in a meaningful way, independent of each entity's physical location. Because of this, World Wide Web
(WWW) hyperlinks and Internet contact information can remain consistent and constant even if the current Internet routing arrangements change or the participant uses a mobile device. Internet domain names are easier to remember than IP addresses such as 208.77.188.166 (IPv4) or 2001:db8:1f70::999:de8:7648:6e8 (IPv6). Users take advantage of this when they recite meaningful Uniform Resource Locator
s (URLs) and e-mail address
es without having to know how the computer actually locates them.
The Domain Name System distributes the responsibility of assigning domain names and mapping those names to IP addresses by designating authoritative name servers for each domain.
Authoritative name servers are assigned to be responsible for their particular domains, and in turn can assign other authoritative name servers for their sub-domains. This mechanism has made the DNS distributed and fault tolerant and has helped avoid the need for a single central register to be continually consulted and updated.
In general, the Domain Name System also stores other types of information, such as the list of mail servers that accept email
for a given Internet domain. By providing a worldwide, distributed keyword-based redirection service, the Domain Name System is an essential component of the functionality of the Internet
.
Other identifiers such as RFID tags, UPC
s, international characters in email addresses and host names, and a variety of other identifiers could all potentially use DNS.
The Domain Name System also specifies the technical functionality of this database service. It defines the DNS protocol, a detailed specification of the data structures and communication exchanges used in DNS, as part of the Internet Protocol Suite
.
s, the domain name hierarchy and the Internet Protocol
(IP) address spaces. The Domain Name System maintains the domain name hierarchy and provides translation services between it and the address spaces. Internet name servers and a communication protocol implement the Domain Name System. A DNS name server is a server that stores the DNS records for a domain name, such as address (A) records, name server (NS) records, and mail exchanger (MX) records (see also list of DNS record types); a DNS name server responds with answers to queries against its database.
era. Before the DNS was invented in 1982, each computer on the network retrieved a file called HOSTS.TXT from a computer at SRI (now SRI International
). The HOSTS.TXT file mapped names to numerical addresses. A hosts file
still exists on most modern operating systems by default and generally contains a mapping of the IP address 127.0.0.1 to "localhost". Many operating systems use name resolution logic that allows the administrator to configure selection priorities for available name resolution methods.
The rapid growth of the network made a centrally maintained, hand-crafted HOSTS.TXT file unsustainable; it became necessary to implement a more scalable system capable of automatically disseminating the requisite information.
At the request of Jon Postel
, Paul Mockapetris
invented the Domain Name System in 1983 and wrote the first implementation. The original specifications were published by the Internet Engineering Task Force
in RFC 882 and RFC 883, which were superseded in November 1987 by RFC 1034 and RFC 1035. Several additional Request for Comments
have proposed various extensions to the core DNS protocols.
In 1984, four Berkeley
students—Douglas Terry, Mark Painter, David Riggle, and Songnian Zhou—wrote the first Unix
implementation, called The Berkeley Internet Name Domain (BIND
) Server. In 1985, Kevin Dunlap of DEC
significantly re-wrote the DNS implementation. Mike Karels, Phil Almquist, and Paul Vixie
have maintained BIND since then. BIND was ported
to the Windows NT
platform in the early 1990s.
BIND was widely distributed, especially on Unix systems, and is the dominant DNS software in use on the Internet. With the heavy use and resulting scrutiny of its open-source code, as well as increasingly more sophisticated attack methods, many security flaws were discovered in BIND. This contributed to the development of a number of alternative name server and resolver programs
. BIND version 9 was written from scratch and now has a security record comparable to other modern DNS software.
. A DNS zone
may consist of only one domain, or may consist of many domains and sub-domains, depending on the administrative authority delegated to the manager.
 Administrative responsibility over any zone may be divided by creating additional zones. Authority is said to be delegated for a portion of the old space, usually in the form of sub-domains, to another nameserver and administrative entity. The old zone ceases to be authoritative for the new zone.
Administrative responsibility over any zone may be divided by creating additional zones. Authority is said to be delegated for a portion of the old space, usually in the form of sub-domains, to another nameserver and administrative entity. The old zone ceases to be authoritative for the new zone.
A domain name
consists of one or more parts, technically called labels, that are conventionally concatenated, and delimited by dots, such as example.com.
has approved the Internationalizing Domain Names in Applications
(IDNA) system, which maps Unicode
strings into the valid DNS character set using Punycode
. In 2009 ICANN approved the installation of IDN country code top-level domains. In addition, many registries
of the existing top level domain names (TLD
)s have adopted IDNA.
model. The nodes of this database are the name servers. Each domain has at least one authoritative DNS server that publishes information about that domain and the name servers of any domains subordinate to it. The top of the hierarchy is served by the root nameserver
s, the servers to query when looking up (resolving) a TLD.
An authoritative name server can either be a master server or a slave server. A master server is a server that stores the original (master) copies of all zone records. A slave server uses an automatic updating mechanism of the DNS protocol in communication with its master to maintain an identical copy of the master records.
Every DNS zone must be assigned a set of authoritative name servers that are installed in NS records in the parent zone.
When domain names are registered with a domain name registrar
, their installation at the domain registry of a top level domain requires the assignment of a primary name server and at least one secondary name server. The requirement of multiple name servers aims to make the domain still functional even if one name server becomes inaccessible or inoperable. The designation of a primary name server is solely determined by the priority given to the domain name registrar. For this purpose, generally only the fully qualified domain name of the name server is required, unless the servers are contained in the registered domain, in which case the corresponding IP address
is needed as well.
Primary name servers are often master name servers, while secondary name server may be implemented as slave servers.
An authoritative server indicates its status of supplying definitive answers, deemed authoritative, by setting a software flag (a protocol structure bit), called the Authoritative Answer (AA) bit in its responses. This flag is usually reproduced prominently in the output of DNS administration query tools (such as dig
) to indicate that the responding name server is an authority for the domain name in question.
of the Domain Name System and each user system must implement resolver software capable of recursive operation.
To improve efficiency, reduce DNS traffic across the Internet, and increase performance in end-user applications, the Domain Name System supports DNS cache servers which store DNS query results for a period of time determined in the configuration (time-to-live) of the domain name record in question.
Typically, such caching DNS servers, also called DNS caches, also implement the recursive algorithm necessary to resolve a given name starting with the DNS root through to the authoritative name servers of the queried domain. With this function implemented in the name server, user applications gain efficiency in design and operation.
The combination of DNS caching and recursive functions in a name server is not mandatory; the functions can be implemented independently in servers for special purposes.
Internet service providers typically provide recursive and caching name servers for their customers. In addition, many home networking routers implement DNS caches and recursors to improve efficiency in the local network.
A DNS query may be either a non-recursive query or a recursive query:
The resolver, or another DNS server acting recursively on behalf of the resolver, negotiates use of recursive service using bits in the query headers.
Resolving usually entails iterating through several name servers to find the needed information. However, some resolvers function more simply by communicating only with a single name server. These simple resolvers (called "stub resolvers") rely on a recursive name server to perform the work of finding information for them.
 The process entails:
The process entails:
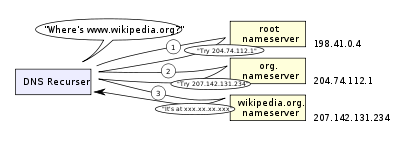
The diagram illustrates this process for the host www.wikipedia.org.
The mechanism in this simple form would place a large operating burden on the root servers, with every search for an address starting by querying one of them. Being as critical as they are to the overall function of the system, such heavy use would create an insurmountable bottleneck for trillions of queries placed every day. In practice caching is used in DNS servers to overcome this problem, and as a result, root nameservers actually are involved with very little of the total traffic.
. In this case the nameserver providing the delegation must also provide one or more IP addresses for the authoritative nameserver mentioned in the delegation. This information is called glue. The delegating name server provides this glue in the form of records in the additional section of the DNS response, and provides the delegation in the answer section of the response.
For example, if the authoritative name server for example.org is ns1.example.org, a computer trying to resolve www.example.org first resolves ns1.example.org. Since ns1 is contained in example.org, this requires resolving example.org first, which presents a circular dependency. To break the dependency, the nameserver for the org top level domain includes glue along with the delegation for example.org. The glue records are address records that provide IP addresses for ns1.example.org. The resolver uses one or more of these IP addresses to query one of domain's authoritative servers, which allows it to complete the DNS query.
(TTL) associated with every record. The TTL is set by the administrator of the DNS server handing out the authoritative response. The period of validity may vary from just seconds to days or even weeks.
As a noteworthy consequence of this distributed and caching architecture, changes to DNS records do not propagate throughout the network immediately, but require all caches to expire and refresh after the TTL. RFC 1912 conveys basic rules for determining appropriate TTL values.
Some resolvers may override TTL values, as the protocol supports caching for up to 68 years or no caching at all. Negative caching, i.e. the caching of the fact of non-existence of a record, is determined by name servers authoritative for a zone which must include the Start of Authority (SOA) record when reporting no data of the requested type exists. The value of the MINIMUM field of the SOA record and the TTL of the SOA itself is used to establish the TTL for the negative answer.
. For IPv4, the domain is in-addr.arpa. For IPv6, the reverse lookup domain is ip6.arpa. The IP address is represented as a name in reverse-ordered octet representation for IPv4, and reverse-ordered nibble representation for IPv6.
When performing a reverse lookup, the DNS client converts the address into these formats, and then queries the name for a PTR record following the delegation chain as for any DNS query. For example, the IPv4 address 208.80.152.2 is represented as a DNS name as 2.152.80.208.in-addr.arpa. The DNS resolver begins by querying the root servers, which point to ARIN's servers for the 208.in-addr.arpa zone. From there the Wikimedia servers are assigned for 152.80.208.in-addr.arpa, and the PTR lookup completes by querying the wikimedia nameserver for 2.152.80.208.in-addr.arpa, which results in an authoritative response.
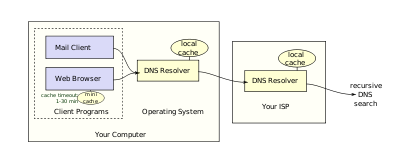
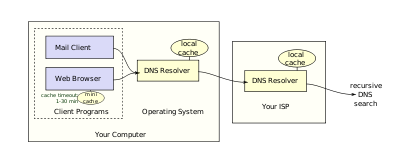 Users generally do not communicate directly with a DNS resolver. Instead DNS resolution takes place transparently in applications programs such as web browser
Users generally do not communicate directly with a DNS resolver. Instead DNS resolution takes place transparently in applications programs such as web browser
s, e-mail client
s, and other Internet applications. When an application makes a request that requires a domain name lookup, such programs send a resolution request to the DNS resolver in the local operating system, which in turn handles the communications required.
The DNS resolver will almost invariably have a cache (see above) containing recent lookups. If the cache can provide the answer to the request, the resolver will return the value in the cache to the program that made the request. If the cache does not contain the answer, the resolver will send the request to one or more designated DNS servers. In the case of most home users, the Internet service provider
to which the machine connects will usually supply this DNS server: such a user will either have configured that server's address manually or allowed DHCP
to set it; however, where systems administrators have configured systems to use their own DNS servers, their DNS resolvers point to separately maintained nameservers of the organization. In any event, the name server thus queried will follow the process outlined above, until it either successfully finds a result or does not. It then returns its results to the DNS resolver; assuming it has found a result, the resolver duly caches that result for future use, and hands the result back to the software which initiated the request.
As a final level of complexity, some applications (such as web-browsers) also have their own DNS cache, in order to reduce the use of the DNS resolver library itself. This practice can add extra difficulty when debugging DNS issues, as it obscures the freshness of data, and/or what data comes from which cache. These caches typically use very short caching times—on the order of one minute.
Internet Explorer
represents a notable exception: versions up to IE 3.x cache DNS records for 24 hours by default. Internet Explorer 4.x and later versions (up to IE 8) decrease the default time out value to half an hour, which may be changed in corresponding registry keys.
(UDP) on port number 53 to serve requests. DNS queries consist of a single UDP request from the client followed by a single UDP reply from the server. The Transmission Control Protocol
(TCP) is used when the response data size exceeds 512 bytes, or for tasks such as zone transfers
. Some resolver implementations use TCP for all queries.
, however, works on complete resource record sets in a canonical order.
When sent over an IP network, all records use the common format specified in RFC 1035:
NAME is the fully qualified domain name of the node in the tree. On the wire, the name may be shortened using label compression where ends of domain names mentioned earlier in the packet can be substituted for the end of the current domain name.
TYPE is the record type. It indicates the format of the data and it gives a hint of its intended use. For example, the A record is used to translate from a domain name to an IPv4 address, the NS record lists which name server
s can answer lookups on a DNS zone
, and the MX record specifies the mail server used to handle mail for a domain specified in an e-mail address
(see also List of DNS record types).
RDATA is data of type-specific relevance, such as the IP address for address records, or the priority and hostname for MX records. Well known record types may use label compression in the RDATA field, but "unknown" record types must not (RFC 3597).
The CLASS of a record is set to IN (for Internet) for common DNS records involving Internet hostnames, servers, or IP addresses. In addition, the classes Chaos
(CH) and Hesiod
(HS) exist. Each class is an independent name space with potentially different delegations of DNS zone
s.
In addition to resource records defined in a zone file
, the domain name system also defines several request types that are used only in communication with other DNS nodes (on the wire), such as when performing zone transfers (AXFR/IXFR) or for EDNS
(OPT).
For example, in the DNS zone x.example, the following configuration specifies that all subdomains (including subdomains of subdomains) of x.example use the mail exchanger a.x.example. The records for a.x.example are needed to specify the mail exchanger. As this has the result of excluding this domain name and its subdomains from the wildcard matches, all subdomains of a.x.example must be defined in a separate wildcard statement.
The role of wildcard records was refined in RFC 4592, because the original definition in RFC 1034 was incomplete and resulted in misinterpretations by implementers.
use the UPDATE DNS opcode to add or remove resource records dynamically from a zone data base maintained on an authoritative DNS server. The feature is described in RFC 2136. This facility is useful to register network clients into the DNS when they boot or become otherwise available on the network. Since a booting client may be assigned a different IP address each time from a DHCP server, it is not possible to provide static DNS assignments for such clients.
Several vulnerability issues were discovered and exploited by malicious users. One such issue is DNS cache poisoning
, in which data is distributed to caching resolvers under the pretense of being an authoritative origin server, thereby polluting the data store with potentially false information and long expiration times (time-to-live). Subsequently, legitimate application requests may be redirected to network hosts operated with malicious intent.
DNS responses are traditionally not cryptographically signed, leading to many attack possibilities; the Domain Name System Security Extensions (DNSSEC) modify DNS to add support for cryptographically signed responses. Several extensions have been devised to secure zone transfers as well.
Some domain names may be used to achieve spoofing effects. For example, paypal.com and paypa1.com are different names, yet users may be unable to distinguish them in a graphical user interface depending on the user's chosen typeface
. In many fonts the letter l and the numeral 1 look very similar or even identical. This problem is acute in systems that support internationalized domain name
s, since many character codes in ISO 10646, may appear identical on typical computer screens. This vulnerability is occasionally exploited in phishing
.
Techniques such as forward-confirmed reverse DNS can also be used to help validate DNS results.
s which are accredited by the Internet Corporation for Assigned Names and Numbers (ICANN), the organization charged with overseeing the name and number systems of the Internet. In addition to ICANN, each top-level domain (TLD) is maintained and serviced technically by an administrative organization, operating a registry. A registry is responsible for maintaining the database of names registered within the TLD it administers. The registry receives registration information from each domain name registrar authorized to assign names in the corresponding TLD and publishes the information using a special service, the whois
protocol.
ICANN
publishes the complete list of TLD registries and domain name registrars. Registrant information associated with domain names is maintained in an online database accessible with the WHOIS
service. For most of the more than 240 country code top-level domain
s (ccTLDs), the domain registries maintain the WHOIS (Registrant, name servers, expiration dates, etc.) information. For instance, DENIC
, Germany NIC, holds the DE domain data. Since about 2001, most gTLD registries have adopted this so-called thick registry approach, i.e. keeping the WHOIS
data in central registries instead of registrar databases.
For COM and NET domain names, a thin registry model is used: the domain registry (e.g. VeriSign
) holds basic WHOIS (registrar and name servers, etc.) data. One can find the detailed WHOIS
(registrant, name server
s, expiry dates, etc.) at the registrars.
Some domain name registries, often called network information centers (NIC), also function as registrars to end-users. The major generic top-level domain registries, such as for the COM, NET, ORG, INFO domains, use a registry-registrar model consisting of many domain name registrars In this method of management, the registry only manages the domain name database and the relationship with the registrars. The registrants (users of a domain name) are customers of the registrar, in some cases through additional layers of resellers.
(RFC) documents published by the Internet Engineering Task Force
(Internet standard
s). The following is a list of RFCs that define the DNS protocol.
Internet
The Internet is a global system of interconnected computer networks that use the standard Internet protocol suite to serve billions of users worldwide...
or a private network
Private network
In the Internet addressing architecture, a private network is a network that uses private IP address space, following the standards set by RFC 1918 and RFC 4193. These addresses are commonly used for home, office, and enterprise local area networks , when globally routable addresses are not...
. It associates various information with domain name
Domain name
A domain name is an identification string that defines a realm of administrative autonomy, authority, or control in the Internet. Domain names are formed by the rules and procedures of the Domain Name System ....
s assigned to each of the participating entities. Most importantly, it translates domain names meaningful to humans into the numerical identifiers associated with networking equipment for the purpose of locating and addressing these devices worldwide.
An often-used analogy to explain the Domain Name System is that it serves as the phone book
Telephone directory
A telephone directory is a listing of telephone subscribers in a geographical area or subscribers to services provided by the organization that publishes the directory...
for the Internet by translating human-friendly computer hostname
Hostname
A hostname is a label that is assigned to a device connected to a computer network and that is used to identify the device in various forms of electronic communication such as the World Wide Web, e-mail or Usenet...
s into IP address
IP address
An Internet Protocol address is a numerical label assigned to each device participating in a computer network that uses the Internet Protocol for communication. An IP address serves two principal functions: host or network interface identification and location addressing...
es. For example, the domain name www.example.com
Example.com
Example.com, example.net, example.org, and example.edu are second-level domain names reserved for documentation purposes and examples of the use of domain names....
translates to the addresses 192.0.32.10 (IPv4
IPv4
Internet Protocol version 4 is the fourth revision in the development of the Internet Protocol and the first version of the protocol to be widely deployed. Together with IPv6, it is at the core of standards-based internetworking methods of the Internet...
) and 2620:0:2d0:200::10 (IPv6
IPv6
Internet Protocol version 6 is a version of the Internet Protocol . It is designed to succeed the Internet Protocol version 4...
).
The Domain Name System makes it possible to assign domain name
Domain name
A domain name is an identification string that defines a realm of administrative autonomy, authority, or control in the Internet. Domain names are formed by the rules and procedures of the Domain Name System ....
s to groups of Internet resources and users in a meaningful way, independent of each entity's physical location. Because of this, World Wide Web
World Wide Web
The World Wide Web is a system of interlinked hypertext documents accessed via the Internet...
(WWW) hyperlinks and Internet contact information can remain consistent and constant even if the current Internet routing arrangements change or the participant uses a mobile device. Internet domain names are easier to remember than IP addresses such as 208.77.188.166 (IPv4) or 2001:db8:1f70::999:de8:7648:6e8 (IPv6). Users take advantage of this when they recite meaningful Uniform Resource Locator
Uniform Resource Locator
In computing, a uniform resource locator or universal resource locator is a specific character string that constitutes a reference to an Internet resource....
s (URLs) and e-mail address
E-mail address
An email address identifies an email box to which email messages are delivered. An example format of an email address is lewis@example.net which is read as lewis at example dot net...
es without having to know how the computer actually locates them.
The Domain Name System distributes the responsibility of assigning domain names and mapping those names to IP addresses by designating authoritative name servers for each domain.
Authoritative name servers are assigned to be responsible for their particular domains, and in turn can assign other authoritative name servers for their sub-domains. This mechanism has made the DNS distributed and fault tolerant and has helped avoid the need for a single central register to be continually consulted and updated.
In general, the Domain Name System also stores other types of information, such as the list of mail servers that accept email
Email
Electronic mail, commonly known as email or e-mail, is a method of exchanging digital messages from an author to one or more recipients. Modern email operates across the Internet or other computer networks. Some early email systems required that the author and the recipient both be online at the...
for a given Internet domain. By providing a worldwide, distributed keyword-based redirection service, the Domain Name System is an essential component of the functionality of the Internet
Internet
The Internet is a global system of interconnected computer networks that use the standard Internet protocol suite to serve billions of users worldwide...
.
Other identifiers such as RFID tags, UPC
Universal Product Code
The Universal Product Code is a barcode symbology , that is widely used in North America, and in countries including the UK, Australia, and New Zealand for tracking trade items in stores. Its most common form, the UPC-A, consists of 12 numerical digits, which are uniquely assigned to each trade item...
s, international characters in email addresses and host names, and a variety of other identifiers could all potentially use DNS.
The Domain Name System also specifies the technical functionality of this database service. It defines the DNS protocol, a detailed specification of the data structures and communication exchanges used in DNS, as part of the Internet Protocol Suite
Internet protocol suite
The Internet protocol suite is the set of communications protocols used for the Internet and other similar networks. It is commonly known as TCP/IP from its most important protocols: Transmission Control Protocol and Internet Protocol , which were the first networking protocols defined in this...
.
Overview
The Internet maintains two principal namespaceNamespace
In general, a namespace is a container that provides context for the identifiers it holds, and allows the disambiguation of homonym identifiers residing in different namespaces....
s, the domain name hierarchy and the Internet Protocol
Internet Protocol
The Internet Protocol is the principal communications protocol used for relaying datagrams across an internetwork using the Internet Protocol Suite...
(IP) address spaces. The Domain Name System maintains the domain name hierarchy and provides translation services between it and the address spaces. Internet name servers and a communication protocol implement the Domain Name System. A DNS name server is a server that stores the DNS records for a domain name, such as address (A) records, name server (NS) records, and mail exchanger (MX) records (see also list of DNS record types); a DNS name server responds with answers to queries against its database.
History
The practice of using a name as a simpler, more memorable abstraction of a host's numerical address on a network dates back to the ARPANETARPANET
The Advanced Research Projects Agency Network , was the world's first operational packet switching network and the core network of a set that came to compose the global Internet...
era. Before the DNS was invented in 1982, each computer on the network retrieved a file called HOSTS.TXT from a computer at SRI (now SRI International
SRI International
SRI International , founded as Stanford Research Institute, is one of the world's largest contract research institutes. Based in Menlo Park, California, the trustees of Stanford University established it in 1946 as a center of innovation to support economic development in the region. It was later...
). The HOSTS.TXT file mapped names to numerical addresses. A hosts file
Hosts file
The hosts file is a computer file used in an operating system to map hostnames to IP addresses. The hosts file is a plain-text file and is conventionally named hosts.-Purpose:...
still exists on most modern operating systems by default and generally contains a mapping of the IP address 127.0.0.1 to "localhost". Many operating systems use name resolution logic that allows the administrator to configure selection priorities for available name resolution methods.
The rapid growth of the network made a centrally maintained, hand-crafted HOSTS.TXT file unsustainable; it became necessary to implement a more scalable system capable of automatically disseminating the requisite information.
At the request of Jon Postel
Jon Postel
Jonathan Bruce Postel was an American computer scientist who made many significant contributions to the development of the Internet, particularly with respect to standards...
, Paul Mockapetris
Paul Mockapetris
Dr. Paul V. Mockapetris is the inventor of the Domain Name System.In 1983, he proposed a Domain Name System architecture in RFCs 882 and 883 while at the Information Sciences Institute of the University of Southern California....
invented the Domain Name System in 1983 and wrote the first implementation. The original specifications were published by the Internet Engineering Task Force
Internet Engineering Task Force
The Internet Engineering Task Force develops and promotes Internet standards, cooperating closely with the W3C and ISO/IEC standards bodies and dealing in particular with standards of the TCP/IP and Internet protocol suite...
in RFC 882 and RFC 883, which were superseded in November 1987 by RFC 1034 and RFC 1035. Several additional Request for Comments
Request for Comments
In computer network engineering, a Request for Comments is a memorandum published by the Internet Engineering Task Force describing methods, behaviors, research, or innovations applicable to the working of the Internet and Internet-connected systems.Through the Internet Society, engineers and...
have proposed various extensions to the core DNS protocols.
In 1984, four Berkeley
University of California, Berkeley
The University of California, Berkeley , is a teaching and research university established in 1868 and located in Berkeley, California, USA...
students—Douglas Terry, Mark Painter, David Riggle, and Songnian Zhou—wrote the first Unix
Unix
Unix is a multitasking, multi-user computer operating system originally developed in 1969 by a group of AT&T employees at Bell Labs, including Ken Thompson, Dennis Ritchie, Brian Kernighan, Douglas McIlroy, and Joe Ossanna...
implementation, called The Berkeley Internet Name Domain (BIND
BIND
BIND , or named , is the most widely used DNS software on the Internet.On Unix-like operating systems it is the de facto standard.Originally written by four graduate students at the Computer Systems Research Group at the University of California, Berkeley , the name originates as an acronym from...
) Server. In 1985, Kevin Dunlap of DEC
Digital Equipment Corporation
Digital Equipment Corporation was a major American company in the computer industry and a leading vendor of computer systems, software and peripherals from the 1960s to the 1990s...
significantly re-wrote the DNS implementation. Mike Karels, Phil Almquist, and Paul Vixie
Paul Vixie
Paul Vixie is an American Internet pioneer, the author of several RFCs and well-known Unix software.Vixie attended George Washington High School in San Francisco, California. He received a Ph.D in computer science from Keio University in 2011....
have maintained BIND since then. BIND was ported
Porting
In computer science, porting is the process of adapting software so that an executable program can be created for a computing environment that is different from the one for which it was originally designed...
to the Windows NT
Windows NT
Windows NT is a family of operating systems produced by Microsoft, the first version of which was released in July 1993. It was a powerful high-level-language-based, processor-independent, multiprocessing, multiuser operating system with features comparable to Unix. It was intended to complement...
platform in the early 1990s.
BIND was widely distributed, especially on Unix systems, and is the dominant DNS software in use on the Internet. With the heavy use and resulting scrutiny of its open-source code, as well as increasingly more sophisticated attack methods, many security flaws were discovered in BIND. This contributed to the development of a number of alternative name server and resolver programs
Comparison of DNS server software
This article presents a comparison of the features, platform support, and packaging of independent implementations of Domain Name System name server software.- Servers compared :...
. BIND version 9 was written from scratch and now has a security record comparable to other modern DNS software.
Domain name space
The domain name space consists of a tree of domain names. Each node or leaf in the tree has zero or more resource records, which hold information associated with the domain name. The tree sub-divides into zones beginning at the root zoneDNS root zone
A DNS root zone is the top-level DNS zone in a Domain Name System hierarchy. Most commonly it refers to the root zone of the largest global DNS, deployed for the Internet. Ultimate authority over the DNS root zone rests with the US Department of Commerce NTIA...
. A DNS zone
DNS zone
A DNS zone is a portion of the global Domain Name System namespace for which administrative responsibility has been delegated.-Definition:...
may consist of only one domain, or may consist of many domains and sub-domains, depending on the administrative authority delegated to the manager.

Domain name syntax
The definitive descriptions of the rules for forming domain names appear in RFC 1035, RFC 1123, and RFC 2181.A domain name
Domain name
A domain name is an identification string that defines a realm of administrative autonomy, authority, or control in the Internet. Domain names are formed by the rules and procedures of the Domain Name System ....
consists of one or more parts, technically called labels, that are conventionally concatenated, and delimited by dots, such as example.com.
- The right-most label conveys the top-level domainTop-level domainA top-level domain is one of the domains at the highest level in the hierarchical Domain Name System of the Internet. The top-level domain names are installed in the root zone of the name space. For all domains in lower levels, it is the last part of the domain name, that is, the last label of a...
; for example, the domain name www.example.com belongs to the top-level domain com. - The hierarchy of domains descends from right to left; each label to the left specifies a subdivision, or subdomainSubdomainIn the Domain Name System hierarchy, a subdomain is a domain that is part of a larger domain.- Overview :The Domain Name System has a tree structure or hierarchy, with each node on the tree being a domain name. A subdomain is a domain that is part of a larger domain, the only domain that is not...
of the domain to the right. For example: the label example specifies a subdomain of the com domain, and www is a sub domain of example.com. This tree of subdivisions may have up to 127 levels. - Each label may contain up to 63 characters. The full domain name may not exceed a total length of 253 characters in its external dotted-label specification. In the internal binary representation of the DNS the maximum length requires 255 octets of storage. In practice, some domain registriesDomain name registryA domain name registry is a database of all domain names registered in a top-level domain. A registry operator, also called a network information center , is the part of the Domain Name System of the Internet that keeps the database of domain names, and generates the zone files which convert...
may have shorter limits. - DNS names may technically consist of any character representable in an octet. However, the allowed formulation of domain names in the DNS root zone, and most other sub domains, uses a preferred format and character set. The characters allowed in a label are a subset of the ASCIIASCIIThe American Standard Code for Information Interchange is a character-encoding scheme based on the ordering of the English alphabet. ASCII codes represent text in computers, communications equipment, and other devices that use text...
character set, and includes the characters a through z, A through Z, digits 0 through 9, and the hyphen. This rule is known as the LDH rule (letters, digits, hyphen). Domain names are interpreted in case-independent manner. Labels may not start or end with a hyphen. - A hostnameHostnameA hostname is a label that is assigned to a device connected to a computer network and that is used to identify the device in various forms of electronic communication such as the World Wide Web, e-mail or Usenet...
is a domain name that has at least one IP address associated. For example, the domain names www.example.com and example.com are also hostnames, whereas the com domain is not.
Internationalized domain names
The permitted character set of the DNS prevented the representation of names and words of many languages in their native alphabets or scripts. ICANNICANN
The Internet Corporation for Assigned Names and Numbers is a non-profit corporation headquartered in Marina del Rey, California, United States, that was created on September 18, 1998, and incorporated on September 30, 1998 to oversee a number of Internet-related tasks previously performed directly...
has approved the Internationalizing Domain Names in Applications
Internationalized domain name
An internationalized domain name is an Internet domain name that contains at least one label that is displayed in software applications, in whole or in part, in a language-specific script or alphabet, such as Arabic, Chinese, Russian, Hindi or the Latin alphabet-based characters with diacritics,...
(IDNA) system, which maps Unicode
Unicode
Unicode is a computing industry standard for the consistent encoding, representation and handling of text expressed in most of the world's writing systems...
strings into the valid DNS character set using Punycode
Punycode
In computing, Punycode is an instance of a general encoding syntax by which a string of Unicode characters is transformed uniquely and reversibly into a smaller, restricted character set....
. In 2009 ICANN approved the installation of IDN country code top-level domains. In addition, many registries
Domain name registry
A domain name registry is a database of all domain names registered in a top-level domain. A registry operator, also called a network information center , is the part of the Domain Name System of the Internet that keeps the database of domain names, and generates the zone files which convert...
of the existing top level domain names (TLD
Top-level domain
A top-level domain is one of the domains at the highest level in the hierarchical Domain Name System of the Internet. The top-level domain names are installed in the root zone of the name space. For all domains in lower levels, it is the last part of the domain name, that is, the last label of a...
)s have adopted IDNA.
Name servers
The Domain Name System is maintained by a distributed database system, which uses the client-serverClient-server
The client–server model of computing is a distributed application that partitions tasks or workloads between the providers of a resource or service, called servers, and service requesters, called clients. Often clients and servers communicate over a computer network on separate hardware, but both...
model. The nodes of this database are the name servers. Each domain has at least one authoritative DNS server that publishes information about that domain and the name servers of any domains subordinate to it. The top of the hierarchy is served by the root nameserver
Root nameserver
A root name server is a name server for the Domain Name System's root zone. It directly answers requests for records in the root zone and answers other requests returning a list of the designated authoritative name servers for the appropriate top-level domain...
s, the servers to query when looking up (resolving) a TLD.
Authoritative name server
An authoritative name server is a name server that gives answers that have been configured by an original source, for example, the domain administrator or by dynamic DNS methods, in contrast to answers that were obtained via a regular DNS query to another name server. An authoritative-only name server only returns answers to queries about domain names that have been specifically configured by the administrator.An authoritative name server can either be a master server or a slave server. A master server is a server that stores the original (master) copies of all zone records. A slave server uses an automatic updating mechanism of the DNS protocol in communication with its master to maintain an identical copy of the master records.
Every DNS zone must be assigned a set of authoritative name servers that are installed in NS records in the parent zone.
When domain names are registered with a domain name registrar
Domain name registrar
A domain name registrar is an organization or commercial entity, accredited by both ICANN and generic top-level domain registry to sell gTLDs and/or by a country code top-level domain registry to sell ccTLDs; to manage the reservation of Internet domain names in accordance with the guidelines of...
, their installation at the domain registry of a top level domain requires the assignment of a primary name server and at least one secondary name server. The requirement of multiple name servers aims to make the domain still functional even if one name server becomes inaccessible or inoperable. The designation of a primary name server is solely determined by the priority given to the domain name registrar. For this purpose, generally only the fully qualified domain name of the name server is required, unless the servers are contained in the registered domain, in which case the corresponding IP address
IP address
An Internet Protocol address is a numerical label assigned to each device participating in a computer network that uses the Internet Protocol for communication. An IP address serves two principal functions: host or network interface identification and location addressing...
is needed as well.
Primary name servers are often master name servers, while secondary name server may be implemented as slave servers.
An authoritative server indicates its status of supplying definitive answers, deemed authoritative, by setting a software flag (a protocol structure bit), called the Authoritative Answer (AA) bit in its responses. This flag is usually reproduced prominently in the output of DNS administration query tools (such as dig
Domain Information Groper
Domain Information Groper is a network administration command-line tool for querying Domain Name System name servers for any desired DNS records....
) to indicate that the responding name server is an authority for the domain name in question.
Recursive and caching name server
In principle, authoritative name servers are sufficient for the operation of the Internet. However, with only authoritative name servers operating, every DNS query must start with recursive queries at the root zoneDNS root zone
A DNS root zone is the top-level DNS zone in a Domain Name System hierarchy. Most commonly it refers to the root zone of the largest global DNS, deployed for the Internet. Ultimate authority over the DNS root zone rests with the US Department of Commerce NTIA...
of the Domain Name System and each user system must implement resolver software capable of recursive operation.
To improve efficiency, reduce DNS traffic across the Internet, and increase performance in end-user applications, the Domain Name System supports DNS cache servers which store DNS query results for a period of time determined in the configuration (time-to-live) of the domain name record in question.
Typically, such caching DNS servers, also called DNS caches, also implement the recursive algorithm necessary to resolve a given name starting with the DNS root through to the authoritative name servers of the queried domain. With this function implemented in the name server, user applications gain efficiency in design and operation.
The combination of DNS caching and recursive functions in a name server is not mandatory; the functions can be implemented independently in servers for special purposes.
Internet service providers typically provide recursive and caching name servers for their customers. In addition, many home networking routers implement DNS caches and recursors to improve efficiency in the local network.
DNS resolvers
The client-side of the DNS is called a DNS resolver. It is responsible for initiating and sequencing the queries that ultimately lead to a full resolution (translation) of the resource sought, e.g., translation of a domain name into an IP address.A DNS query may be either a non-recursive query or a recursive query:
- A non-recursive query is one in which the DNS server provides a record for a domain for which it is authoritative itself, or it provides a partial result without querying other servers.
- A recursive query is one for which the DNS server will fully answer the query (or give an error) by querying other name servers as needed. DNS servers are not required to support recursive queries.
The resolver, or another DNS server acting recursively on behalf of the resolver, negotiates use of recursive service using bits in the query headers.
Resolving usually entails iterating through several name servers to find the needed information. However, some resolvers function more simply by communicating only with a single name server. These simple resolvers (called "stub resolvers") rely on a recursive name server to perform the work of finding information for them.
Address resolution mechanism
Domain name resolvers determine the appropriate domain name servers responsible for the domain name in question by a sequence of queries starting with the right-most (top-level) domain label.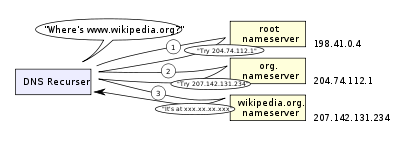
- A network host is configured with an initial cache (so called hints) of the known addresses of the root nameserverRoot nameserverA root name server is a name server for the Domain Name System's root zone. It directly answers requests for records in the root zone and answers other requests returning a list of the designated authoritative name servers for the appropriate top-level domain...
s. Such a hint file is updated periodically by an administrator from a reliable source. - A query to one of the root servers to find the server authoritative for the top-level domain.
- A query to the obtained TLD server for the address of a DNS server authoritative for the second-level domain.
- Repetition of the previous step to process each domain name label in sequence, until the final step which returns the IP address of the host sought.
The diagram illustrates this process for the host www.wikipedia.org.
The mechanism in this simple form would place a large operating burden on the root servers, with every search for an address starting by querying one of them. Being as critical as they are to the overall function of the system, such heavy use would create an insurmountable bottleneck for trillions of queries placed every day. In practice caching is used in DNS servers to overcome this problem, and as a result, root nameservers actually are involved with very little of the total traffic.
Circular dependencies and glue records
Name servers in delegations are identified by name, rather than by IP address. This means that a resolving name server must issue another DNS request to find out the IP address of the server to which it has been referred. If the name given in the delegation is a subdomain of the domain for which the delegation is being provided, there is a circular dependencyCircular dependency
In software engineering, a circular dependency is a relation between two or more modules which either directly or indirectly depend on each other to function properly.-Overview:...
. In this case the nameserver providing the delegation must also provide one or more IP addresses for the authoritative nameserver mentioned in the delegation. This information is called glue. The delegating name server provides this glue in the form of records in the additional section of the DNS response, and provides the delegation in the answer section of the response.
For example, if the authoritative name server for example.org is ns1.example.org, a computer trying to resolve www.example.org first resolves ns1.example.org. Since ns1 is contained in example.org, this requires resolving example.org first, which presents a circular dependency. To break the dependency, the nameserver for the org top level domain includes glue along with the delegation for example.org. The glue records are address records that provide IP addresses for ns1.example.org. The resolver uses one or more of these IP addresses to query one of domain's authoritative servers, which allows it to complete the DNS query.
Record caching
Because of the large volume of DNS requests generated for the public Internet, the designers wished to provide a mechanism to reduce the load on individual DNS servers. To this end, the DNS resolution process allows for caching of records for a period of time after an answer. This entails the local recording and subsequent consultation of the copy instead of initiating a new request upstream. The time for which a resolver caches a DNS response is determined by a value called the time to liveTime to live
Time to live is a mechanism that limits the lifespan of data in a computer or network. TTL may be implemented as a counter or timestamp attached to or embedded in the data. Once the prescribed event count or timespan has elapsed, data is discarded. In computer networking, TTL prevents a data...
(TTL) associated with every record. The TTL is set by the administrator of the DNS server handing out the authoritative response. The period of validity may vary from just seconds to days or even weeks.
As a noteworthy consequence of this distributed and caching architecture, changes to DNS records do not propagate throughout the network immediately, but require all caches to expire and refresh after the TTL. RFC 1912 conveys basic rules for determining appropriate TTL values.
Some resolvers may override TTL values, as the protocol supports caching for up to 68 years or no caching at all. Negative caching, i.e. the caching of the fact of non-existence of a record, is determined by name servers authoritative for a zone which must include the Start of Authority (SOA) record when reporting no data of the requested type exists. The value of the MINIMUM field of the SOA record and the TTL of the SOA itself is used to establish the TTL for the negative answer.
Reverse lookup
A reverse lookup is a query of the DNS for domain names when the IP address is known. Multiple domain names may be associated with an IP address. The DNS stores IP addresses in the form of domain names as specially formatted names in pointer (PTR) records within the infrastructure top-level domain arpa.arpa
The domain name arpa is a top-level domain in the Domain Name System of the Internet. It is used exclusively for technical infrastructure purposes...
. For IPv4, the domain is in-addr.arpa. For IPv6, the reverse lookup domain is ip6.arpa. The IP address is represented as a name in reverse-ordered octet representation for IPv4, and reverse-ordered nibble representation for IPv6.
When performing a reverse lookup, the DNS client converts the address into these formats, and then queries the name for a PTR record following the delegation chain as for any DNS query. For example, the IPv4 address 208.80.152.2 is represented as a DNS name as 2.152.80.208.in-addr.arpa. The DNS resolver begins by querying the root servers, which point to ARIN's servers for the 208.in-addr.arpa zone. From there the Wikimedia servers are assigned for 152.80.208.in-addr.arpa, and the PTR lookup completes by querying the wikimedia nameserver for 2.152.80.208.in-addr.arpa, which results in an authoritative response.
Client lookup
Web browser
A web browser is a software application for retrieving, presenting, and traversing information resources on the World Wide Web. An information resource is identified by a Uniform Resource Identifier and may be a web page, image, video, or other piece of content...
s, e-mail client
E-mail client
An email client, email reader, or more formally mail user agent , is a computer program used to manage a user's email.The term can refer to any system capable of accessing the user's email mailbox, regardless of it being a mail user agent, a relaying server, or a human typing on a terminal...
s, and other Internet applications. When an application makes a request that requires a domain name lookup, such programs send a resolution request to the DNS resolver in the local operating system, which in turn handles the communications required.
The DNS resolver will almost invariably have a cache (see above) containing recent lookups. If the cache can provide the answer to the request, the resolver will return the value in the cache to the program that made the request. If the cache does not contain the answer, the resolver will send the request to one or more designated DNS servers. In the case of most home users, the Internet service provider
Internet service provider
An Internet service provider is a company that provides access to the Internet. Access ISPs directly connect customers to the Internet using copper wires, wireless or fiber-optic connections. Hosting ISPs lease server space for smaller businesses and host other people servers...
to which the machine connects will usually supply this DNS server: such a user will either have configured that server's address manually or allowed DHCP
Dynamic Host Configuration Protocol
The Dynamic Host Configuration Protocol is a network configuration protocol for hosts on Internet Protocol networks. Computers that are connected to IP networks must be configured before they can communicate with other hosts. The most essential information needed is an IP address, and a default...
to set it; however, where systems administrators have configured systems to use their own DNS servers, their DNS resolvers point to separately maintained nameservers of the organization. In any event, the name server thus queried will follow the process outlined above, until it either successfully finds a result or does not. It then returns its results to the DNS resolver; assuming it has found a result, the resolver duly caches that result for future use, and hands the result back to the software which initiated the request.
Broken resolvers
An additional level of complexity emerges when resolvers violate the rules of the DNS protocol. A number of large ISPs have configured their DNS servers to violate rules (presumably to allow them to run on less-expensive hardware than a fully compliant resolver), such as by disobeying TTLs, or by indicating that a domain name does not exist just because one of its name servers does not respond.As a final level of complexity, some applications (such as web-browsers) also have their own DNS cache, in order to reduce the use of the DNS resolver library itself. This practice can add extra difficulty when debugging DNS issues, as it obscures the freshness of data, and/or what data comes from which cache. These caches typically use very short caching times—on the order of one minute.
Internet Explorer
Internet Explorer
Windows Internet Explorer is a series of graphical web browsers developed by Microsoft and included as part of the Microsoft Windows line of operating systems, starting in 1995. It was first released as part of the add-on package Plus! for Windows 95 that year...
represents a notable exception: versions up to IE 3.x cache DNS records for 24 hours by default. Internet Explorer 4.x and later versions (up to IE 8) decrease the default time out value to half an hour, which may be changed in corresponding registry keys.
Other applications
The system outlined above provides a somewhat simplified scenario. The Domain Name System includes several other functions:- Hostnames and IP addresses do not necessarily match on a one-to-one basis. Multiple hostnames may correspond to a single IP address: combined with virtual hostingVirtual hostingVirtual hosting is a method for hosting multiple domain names on a server using a single IP address. This allows one server to share its resources, such as memory and processor cycles, in order to use its resources more efficiently....
, this allows a single machine to serve many web sites. Alternatively a single hostname may correspond to many IP addresses: this can facilitate fault tolerance and load distribution, and also allows a site to move physical location seamlessly. - There are many uses of DNS besides translating names to IP addresses. For instance, Mail transfer agentMail transfer agentWithin Internet message handling services , a message transfer agent or mail transfer agent or mail relay is software that transfers electronic mail messages from one computer to another using a client–server application architecture...
s use DNS to find out where to deliver e-mailE-mailElectronic mail, commonly known as email or e-mail, is a method of exchanging digital messages from an author to one or more recipients. Modern email operates across the Internet or other computer networks. Some early email systems required that the author and the recipient both be online at the...
for a particular address. The domain to mail exchanger mapping provided by MX recordMX recordA mail exchanger record is a type of resource record in the Domain Name System that specifies a mail server responsible for accepting email messages on behalf of a recipient's domain, and a preference value used to prioritize mail delivery if multiple mail servers are available...
s accommodates another layer of fault tolerance and load distribution on top of the name to IP address mapping.
- E-mail Blacklists: The DNS system is used for efficient storage and distribution of IP addresses of blacklisted e-mail hosts. The usual method is putting the IP address of the subject host into the sub-domain of a higher level domain name, and resolve that name to different records to indicate a positive or a negative. Here is a hypothetical example blacklist:
- 102.3.4.5 is blacklisted => Creates 5.4.3.102.blacklist.example and resolves to 127.0.0.1
- 102.3.4.6 is not => 6.4.3.102.blacklist.example is not found, or default to 127.0.0.2
- E-mail servers can then query blacklist.example through the DNS mechanism to find out if a specific host connecting to them is in the blacklist. Today many of such blacklists, either free or subscription-based, are available mainly for use by email administrators and anti-spam software.
- Software Updates: many anti-virus and commercial software now use the DNS system to store version numbers of the latest software updates so client computers do not need to connect to the update servers every time. For these types of applications, the cache time of the DNS records are usually shorter.
- Sender Policy FrameworkSender Policy FrameworkSender Policy Framework is an email validation system designed to prevent email spam by detecting email spoofing, a common vulnerability, by verifying sender IP addresses. SPF allows administrators to specify which hosts are allowed to send mail from a given domain by creating a specific SPF...
and DomainKeysDomainKeysDomainKeys is an e-mail authentication system designed to verify the DNS domain of an e-mail sender and the message integrity. The DomainKeys specification has adopted aspects of Identified Internet Mail to create an enhanced protocol called DomainKeys Identified Mail...
, instead of creating their own record types, were designed to take advantage of another DNS record type, the TXT record. - To provide resilience in the event of computer failure, multiple DNS servers are usually provided for coverage of each domain, and at the top level, thirteen very powerful root serverRoot nameserverA root name server is a name server for the Domain Name System's root zone. It directly answers requests for records in the root zone and answers other requests returning a list of the designated authoritative name servers for the appropriate top-level domain...
s exist, with additional "copies" of several of them distributed worldwide via AnycastAnycastAnycast is a network addressing and routing methodology in which datagrams from a single sender are routed to the topologically nearest node in a group of potential receivers all identified by the same destination address.-Addressing methodologies:...
. - Dynamic DNSDynamic DNSDynamic DNS or DDNS is a term used for the updating in real time of Internet Domain Name System name servers to keep up to date the active DNS configuration of their configured hostnames, addresses and other information....
(sometimes called DDNS) allows clients to update their DNS entry as their IP address changes, as it does, for example, when moving between ISPsInternet service providerAn Internet service provider is a company that provides access to the Internet. Access ISPs directly connect customers to the Internet using copper wires, wireless or fiber-optic connections. Hosting ISPs lease server space for smaller businesses and host other people servers...
or mobile hot spots.
Protocol details
DNS primarily uses User Datagram ProtocolUser Datagram Protocol
The User Datagram Protocol is one of the core members of the Internet Protocol Suite, the set of network protocols used for the Internet. With UDP, computer applications can send messages, in this case referred to as datagrams, to other hosts on an Internet Protocol network without requiring...
(UDP) on port number 53 to serve requests. DNS queries consist of a single UDP request from the client followed by a single UDP reply from the server. The Transmission Control Protocol
Transmission Control Protocol
The Transmission Control Protocol is one of the core protocols of the Internet Protocol Suite. TCP is one of the two original components of the suite, complementing the Internet Protocol , and therefore the entire suite is commonly referred to as TCP/IP...
(TCP) is used when the response data size exceeds 512 bytes, or for tasks such as zone transfers
DNS zone transfer
DNS zone transfer, also sometimes known by its opcode mnemonic AXFR, is a type of DNS transaction. It is one of the many mechanisms available for administrators to employ for replicating the databases containing the DNS data across a set of DNS servers. Zone transfer comes in two flavors, full ...
. Some resolver implementations use TCP for all queries.
DNS resource records
A Resource Record (RR) is the basic data element in the domain name system. Each record has a type (A, MX, etc.), an expiration time limit, a class, and some type-specific data. Resource records of the same type define a resource record set (RRset). The order of resource records in a set, returned by a resolver to an application, is undefined, but often servers implement round-robin ordering to achieve load balancing. DNSSECDNSSEC
The Domain Name System Security Extensions is a suite of Internet Engineering Task Force specifications for securing certain kinds of information provided by the Domain Name System as used on Internet Protocol networks...
, however, works on complete resource record sets in a canonical order.
When sent over an IP network, all records use the common format specified in RFC 1035:
| Field | Description | Length (octet Octet (computing) An octet is a unit of digital information in computing and telecommunications that consists of eight bits. The term is often used when the term byte might be ambiguous, as there is no standard for the size of the byte.-Overview:... s) |
|---|---|---|
| NAME | Name of the node to which this record pertains | (variable) |
| TYPE | Type of RR in numeric form (e.g. 15 for MX RRs) | 2 |
| CLASS | Class code | 2 |
| TTL Time to live Time to live is a mechanism that limits the lifespan of data in a computer or network. TTL may be implemented as a counter or timestamp attached to or embedded in the data. Once the prescribed event count or timespan has elapsed, data is discarded. In computer networking, TTL prevents a data... |
Count of seconds that the RR stays valid (The maximum is 231-1, which is about 68 years.) | 4 |
| RDLENGTH | Length of RDATA field | 2 |
| RDATA | Additional RR-specific data | (variable) |
NAME is the fully qualified domain name of the node in the tree. On the wire, the name may be shortened using label compression where ends of domain names mentioned earlier in the packet can be substituted for the end of the current domain name.
TYPE is the record type. It indicates the format of the data and it gives a hint of its intended use. For example, the A record is used to translate from a domain name to an IPv4 address, the NS record lists which name server
Name server
In computing, a name server is a program or computer server that implements a name-service protocol. It maps a human-recognizable identifier to a system-internal, often numeric, identification or addressing component....
s can answer lookups on a DNS zone
DNS zone
A DNS zone is a portion of the global Domain Name System namespace for which administrative responsibility has been delegated.-Definition:...
, and the MX record specifies the mail server used to handle mail for a domain specified in an e-mail address
E-mail address
An email address identifies an email box to which email messages are delivered. An example format of an email address is lewis@example.net which is read as lewis at example dot net...
(see also List of DNS record types).
RDATA is data of type-specific relevance, such as the IP address for address records, or the priority and hostname for MX records. Well known record types may use label compression in the RDATA field, but "unknown" record types must not (RFC 3597).
The CLASS of a record is set to IN (for Internet) for common DNS records involving Internet hostnames, servers, or IP addresses. In addition, the classes Chaos
CHAOSnet
Chaosnet was first developed by Thomas Knight and Jack Holloway at MIT's AI Lab in 1975 and thereafter. It refers to two separate, but closely related, technologies...
(CH) and Hesiod
Hesiod (name service)
In computing, the Hesiod name service originated in Project Athena . It uses DNS functionality to provide access to databases of information that change infrequently...
(HS) exist. Each class is an independent name space with potentially different delegations of DNS zone
DNS zone
A DNS zone is a portion of the global Domain Name System namespace for which administrative responsibility has been delegated.-Definition:...
s.
In addition to resource records defined in a zone file
Zone file
A Domain Name System zone file is a text file that describes a DNS zone. A DNS zone is a subset, often a single domain, of the hierarchical domain name structure of the DNS. The zone file contains mappings between domain names and IP addresses and other resources, organized in the form of text...
, the domain name system also defines several request types that are used only in communication with other DNS nodes (on the wire), such as when performing zone transfers (AXFR/IXFR) or for EDNS
EDNS
Extension mechanisms for DNS is a specification for expanding the size of several parameters of the Domain Name System protocol which had size restrictions that the Internet engineering community deemed too limited for increasing functionality of the protocol...
(OPT).
Wildcard DNS records
The domain name system supports wildcard domain names which are names that start with the asterisk label, '*', e.g., *.example. DNS records belonging to wildcard domain names specify rules for generating resource records within a single DNS zone by substituting whole labels with matching components of the query name, including any specified descendants.For example, in the DNS zone x.example, the following configuration specifies that all subdomains (including subdomains of subdomains) of x.example use the mail exchanger a.x.example. The records for a.x.example are needed to specify the mail exchanger. As this has the result of excluding this domain name and its subdomains from the wildcard matches, all subdomains of a.x.example must be defined in a separate wildcard statement.
The role of wildcard records was refined in RFC 4592, because the original definition in RFC 1034 was incomplete and resulted in misinterpretations by implementers.
Protocol extensions
The original DNS protocol had limited provisions for extension with new features. In 1999, Paul Vixie published in RFC 2671 an extension mechanism, called Extension mechanisms for DNS (EDNS) that introduced optional protocol elements without increasing overhead when not in use. This was accomplished through the OPT pseudo-resource record that only exists in wire transmissions of the protocol, but not in any zone files. Initial extensions were also suggested (EDNS0), such as increasing the DNS message size in UDP datagrams.Dynamic zone updates
Dynamic DNS updatesDynamic DNS
Dynamic DNS or DDNS is a term used for the updating in real time of Internet Domain Name System name servers to keep up to date the active DNS configuration of their configured hostnames, addresses and other information....
use the UPDATE DNS opcode to add or remove resource records dynamically from a zone data base maintained on an authoritative DNS server. The feature is described in RFC 2136. This facility is useful to register network clients into the DNS when they boot or become otherwise available on the network. Since a booting client may be assigned a different IP address each time from a DHCP server, it is not possible to provide static DNS assignments for such clients.
Security issues
Originally, security concerns were not major design considerations for DNS software or any software for deployment on the early Internet, as the network was not open for participation by the general public. However, the expansion of the Internet into the commercial sector in the 1990s changed the requirements for security measures to protect data integrity and user authentication.Several vulnerability issues were discovered and exploited by malicious users. One such issue is DNS cache poisoning
DNS cache poisoning
DNS cache poisoning is a security or data integrity compromise in the Domain Name System . The compromise occurs when data is introduced into a DNS name server's cache database that did not originate from authoritative DNS sources. It may be a deliberate attempt of a maliciously crafted attack on a...
, in which data is distributed to caching resolvers under the pretense of being an authoritative origin server, thereby polluting the data store with potentially false information and long expiration times (time-to-live). Subsequently, legitimate application requests may be redirected to network hosts operated with malicious intent.
DNS responses are traditionally not cryptographically signed, leading to many attack possibilities; the Domain Name System Security Extensions (DNSSEC) modify DNS to add support for cryptographically signed responses. Several extensions have been devised to secure zone transfers as well.
Some domain names may be used to achieve spoofing effects. For example, paypal.com and paypa1.com are different names, yet users may be unable to distinguish them in a graphical user interface depending on the user's chosen typeface
Typeface
In typography, a typeface is the artistic representation or interpretation of characters; it is the way the type looks. Each type is designed and there are thousands of different typefaces in existence, with new ones being developed constantly....
. In many fonts the letter l and the numeral 1 look very similar or even identical. This problem is acute in systems that support internationalized domain name
Internationalized domain name
An internationalized domain name is an Internet domain name that contains at least one label that is displayed in software applications, in whole or in part, in a language-specific script or alphabet, such as Arabic, Chinese, Russian, Hindi or the Latin alphabet-based characters with diacritics,...
s, since many character codes in ISO 10646, may appear identical on typical computer screens. This vulnerability is occasionally exploited in phishing
Phishing
Phishing is a way of attempting to acquire information such as usernames, passwords, and credit card details by masquerading as a trustworthy entity in an electronic communication. Communications purporting to be from popular social web sites, auction sites, online payment processors or IT...
.
Techniques such as forward-confirmed reverse DNS can also be used to help validate DNS results.
Domain name registration
The right to use a domain name is delegated by domain name registrarDomain name registrar
A domain name registrar is an organization or commercial entity, accredited by both ICANN and generic top-level domain registry to sell gTLDs and/or by a country code top-level domain registry to sell ccTLDs; to manage the reservation of Internet domain names in accordance with the guidelines of...
s which are accredited by the Internet Corporation for Assigned Names and Numbers (ICANN), the organization charged with overseeing the name and number systems of the Internet. In addition to ICANN, each top-level domain (TLD) is maintained and serviced technically by an administrative organization, operating a registry. A registry is responsible for maintaining the database of names registered within the TLD it administers. The registry receives registration information from each domain name registrar authorized to assign names in the corresponding TLD and publishes the information using a special service, the whois
WHOIS
WHOIS is a query and response protocol that is widely used for querying databases that store the registered users or assignees of an Internet resource, such as a domain name, an IP address block, or an autonomous system, but is also used for a wider range of other information. The protocol stores...
protocol.
ICANN
ICANN
The Internet Corporation for Assigned Names and Numbers is a non-profit corporation headquartered in Marina del Rey, California, United States, that was created on September 18, 1998, and incorporated on September 30, 1998 to oversee a number of Internet-related tasks previously performed directly...
publishes the complete list of TLD registries and domain name registrars. Registrant information associated with domain names is maintained in an online database accessible with the WHOIS
WHOIS
WHOIS is a query and response protocol that is widely used for querying databases that store the registered users or assignees of an Internet resource, such as a domain name, an IP address block, or an autonomous system, but is also used for a wider range of other information. The protocol stores...
service. For most of the more than 240 country code top-level domain
Country code top-level domain
A country code top-level domain is an Internet top-level domain generally used or reserved for a country, a sovereign state, or a dependent territory....
s (ccTLDs), the domain registries maintain the WHOIS (Registrant, name servers, expiration dates, etc.) information. For instance, DENIC
DENIC
DENIC Verwaltungs- und Betriebsgesellschaft eG is the manager of the .de domain, the country-code top-level domain for Germany.In 2005, it was one of five bidders seeking to win contract to operate the .net contract offered by ICANN.- Etymology :...
, Germany NIC, holds the DE domain data. Since about 2001, most gTLD registries have adopted this so-called thick registry approach, i.e. keeping the WHOIS
WHOIS
WHOIS is a query and response protocol that is widely used for querying databases that store the registered users or assignees of an Internet resource, such as a domain name, an IP address block, or an autonomous system, but is also used for a wider range of other information. The protocol stores...
data in central registries instead of registrar databases.
For COM and NET domain names, a thin registry model is used: the domain registry (e.g. VeriSign
VeriSign
Verisign, Inc. is an American company based in Dulles, Virginia that operates a diverse array of network infrastructure, including two of the Internet's thirteen root nameservers, the authoritative registry for the .com, .net, and .name generic top-level domains and the .cc and .tv country-code...
) holds basic WHOIS (registrar and name servers, etc.) data. One can find the detailed WHOIS
WHOIS
WHOIS is a query and response protocol that is widely used for querying databases that store the registered users or assignees of an Internet resource, such as a domain name, an IP address block, or an autonomous system, but is also used for a wider range of other information. The protocol stores...
(registrant, name server
Name server
In computing, a name server is a program or computer server that implements a name-service protocol. It maps a human-recognizable identifier to a system-internal, often numeric, identification or addressing component....
s, expiry dates, etc.) at the registrars.
Some domain name registries, often called network information centers (NIC), also function as registrars to end-users. The major generic top-level domain registries, such as for the COM, NET, ORG, INFO domains, use a registry-registrar model consisting of many domain name registrars In this method of management, the registry only manages the domain name database and the relationship with the registrars. The registrants (users of a domain name) are customers of the registrar, in some cases through additional layers of resellers.
Internet standards
The Domain Name System is defined by Request for CommentsRequest for Comments
In computer network engineering, a Request for Comments is a memorandum published by the Internet Engineering Task Force describing methods, behaviors, research, or innovations applicable to the working of the Internet and Internet-connected systems.Through the Internet Society, engineers and...
(RFC) documents published by the Internet Engineering Task Force
Internet Engineering Task Force
The Internet Engineering Task Force develops and promotes Internet standards, cooperating closely with the W3C and ISO/IEC standards bodies and dealing in particular with standards of the TCP/IP and Internet protocol suite...
(Internet standard
Internet standard
In computer network engineering, an Internet Standard is a normative specification of a technology or methodology applicable to the Internet. Internet Standards are created and published by the Internet Engineering Task Force .-Overview:...
s). The following is a list of RFCs that define the DNS protocol.
- RFC 920, Domain Requirements – Specified original top-level domains
- RFC 1032, Domain Administrators Guide
- RFC 1033, Domain Administrators Operations Guide
- RFC 1034, Domain Names - Concepts and Facilities
- RFC 1035, Domain Names - Implementation and Specification
- RFC 1101, DNS Encodings of Network Names and Other Types
- RFC 1123, Requirements for Internet Hosts—Application and Support
- RFC 1178, Choosing a Name for Your Computer (FYI 5)
- RFC 1183, New DNS RR Definitions
- RFC 1591, Domain Name System Structure and Delegation (Informational)
- RFC 1912, Common DNS Operational and Configuration Errors
- RFC 1995, Incremental Zone Transfer in DNS
- RFC 1996, A Mechanism for Prompt Notification of Zone Changes (DNS NOTIFY)
- RFC 2100, The Naming of Hosts (Informational)
- RFC 2136, Dynamic Updates in the domain name system (DNS UPDATE)
- RFC 2181, Clarifications to the DNS Specification
- RFC 2182, Selection and Operation of Secondary DNS Servers
- RFC 2308, Negative Caching of DNS Queries (DNS NCACHE)
- RFC 2317, Classless IN-ADDR.ARPA delegation (BCP 20)
- RFC 2671, Extension Mechanisms for DNS (EDNS0)
- RFC 2672, Non-Terminal DNS Name Redirection
- RFC 2845, Secret Key Transaction Authentication for DNS (TSIG)
- RFC 3225, Indicating Resolver Support of DNSSEC
- RFC 3226, DNSSEC and IPv6 A6 aware server/resolver message size requirements
- RFC 3597, Handling of Unknown DNS Resource Record (RR) Types
- RFC 3696, Application Techniques for Checking and Transformation of Names (Informational)
- RFC 4343, Domain Name System (DNS) Case Insensitivity Clarification
- RFC 4592, The Role of Wildcards in the Domain Name System
- RFC 4635, HMAC SHA TSIG Algorithm Identifiers
- RFC 4892, Requirements for a Mechanism Identifying a Name Server Instance (Informational)
- RFC 5001, DNS Name Server Identifier (NSID) Option
- RFC 5452, Measures for Making DNS More Resilient against Forged Answers
- RFC 5625, DNS Proxy Implementation Guidelines (BCP 152)
- RFC 5890, Internationalized Domain Names for Applications (IDNA):Definitions and Document Framework
- RFC 5891, Internationalized Domain Names in Applications (IDNA): Protocol
- RFC 5892, The Unicode Code Points and Internationalized Domain Names for Applications (IDNA)
- RFC 5893, Right-to-Left Scripts for Internationalized Domain Names for Applications (IDNA)
- RFC 5894, Internationalized Domain Names for Applications (IDNA):Background, Explanation, and Rationale (Informational)
- RFC 5895, Mapping Characters for Internationalized Domain Names in Applications (IDNA) 2008 (Informational)
- RFC 6195, Domain Name System (DNS) IANA Considerations (BCP 42)
Security
- RFC 4033, DNS Security Introduction and Requirements
- RFC 4034, Resource Records for the DNS Security Extensions
- RFC 4035, Protocol Modifications for the DNS Security Extensions
- RFC 4509, Use of SHA-256 in DNSSEC Delegation Signer (DS) Resource Records
- RFC 4470, Minimally Covering NSEC Records and DNSSEC On-line Signing
- RFC 5011, Automated Updates of DNS Security (DNSSEC) Trust Anchors
- RFC 5155, DNS Security (DNSSEC) Hashed Authenticated Denial of Existence
- RFC 5702, Use of SHA-2 Algorithms with RSA in DNSKEY and RRSIG Resource Records for DNSSEC
- RFC 5910, Domain Name System (DNS) Security Extensions Mapping for the Extensible Provisioning Protocol (EPP)
- RFC 5933, Use of GOST Signature Algorithms in DNSKEY and RRSIG Resource Records for DNSSEC
See also
- Alternative DNS rootAlternative DNS rootThe Internet uses the Domain Name System to associate the names of computers with their numeric IP addresses and with other information. The top level of the domain name hierarchy, the DNS root, contains the top-level domains that appear as the suffixes of all Internet domain names. The official...
- Comparison of DNS server softwareComparison of DNS server softwareThis article presents a comparison of the features, platform support, and packaging of independent implementations of Domain Name System name server software.- Servers compared :...
- DNS cache poisoningDNS cache poisoningDNS cache poisoning is a security or data integrity compromise in the Domain Name System . The compromise occurs when data is introduced into a DNS name server's cache database that did not originate from authoritative DNS sources. It may be a deliberate attempt of a maliciously crafted attack on a...
- DNS hijackingDNS hijackingDNS hijacking or DNS redirection is the practice of redirecting the resolution of Domain Name System names to other DNS servers. This is done for malicious purposes such as phishing; for self-serving purposes by Internet service providers to direct users' HTTP traffic via the ISP's own webservers...
- DNS management softwareDNS management softwareDNS management software is computer software that controls Domain Name System server clusters. Its main purpose is to reduce human error when editing complex and repetitive text-based DNS server configuration files. Such files are often deployed on multiple physical servers.DNS service providers...
- Dynamic DNSDynamic DNSDynamic DNS or DDNS is a term used for the updating in real time of Internet Domain Name System name servers to keep up to date the active DNS configuration of their configured hostnames, addresses and other information....
- Internet Provider SecurityInternet Provider SecurityInternet Provider Security tags are used by Internet Service Providers to allow control of the Domain Name System . An IPS tag is the case sensitive label that applies to each ISP and is required to transfer domain names from one ISP to another...
- IPv6 brokenness and DNS whitelistingIPv6 brokenness and DNS whitelistingIn the field of IPv6 deployment, IPv6 brokenness is bad behavior seen in tunneled or dual stack IPv6 deployments where unreliable or bogus IPv6 connectivity is chosen in preference to working IPv4 connectivity...
- List of DNS record types
- Microsoft DNSMicrosoft DNSMicrosoft DNS is the name given to the implementation of domain name system services provided in Microsoft Windows operating systems.- Overview :...
- Round robin DNSRound robin DNSRound robin DNSis a technique of load distribution, load balancing, or fault-tolerance provisioning multiple, redundant Internet Protocol service hosts, e.g., Web servers, FTP servers, by managing the Domain Name System's responses to address requests from client computers according to an...
- Split-horizon DNSSplit-horizon DNSIn computer networking, split-horizon DNS, split-view DNS, or split-brain DNS is the facility of a Domain Name System implementation to provide different sets of DNS information, selected by, usually, the source address of the DNS request....
External links
- Zytrax.com, Open Source Guide – DNS for Rocket Scientists, an on-line technical.
- Domain Name System on Microsoft TechNet

